ELFEN: Linux Malware Analysis Sandbox
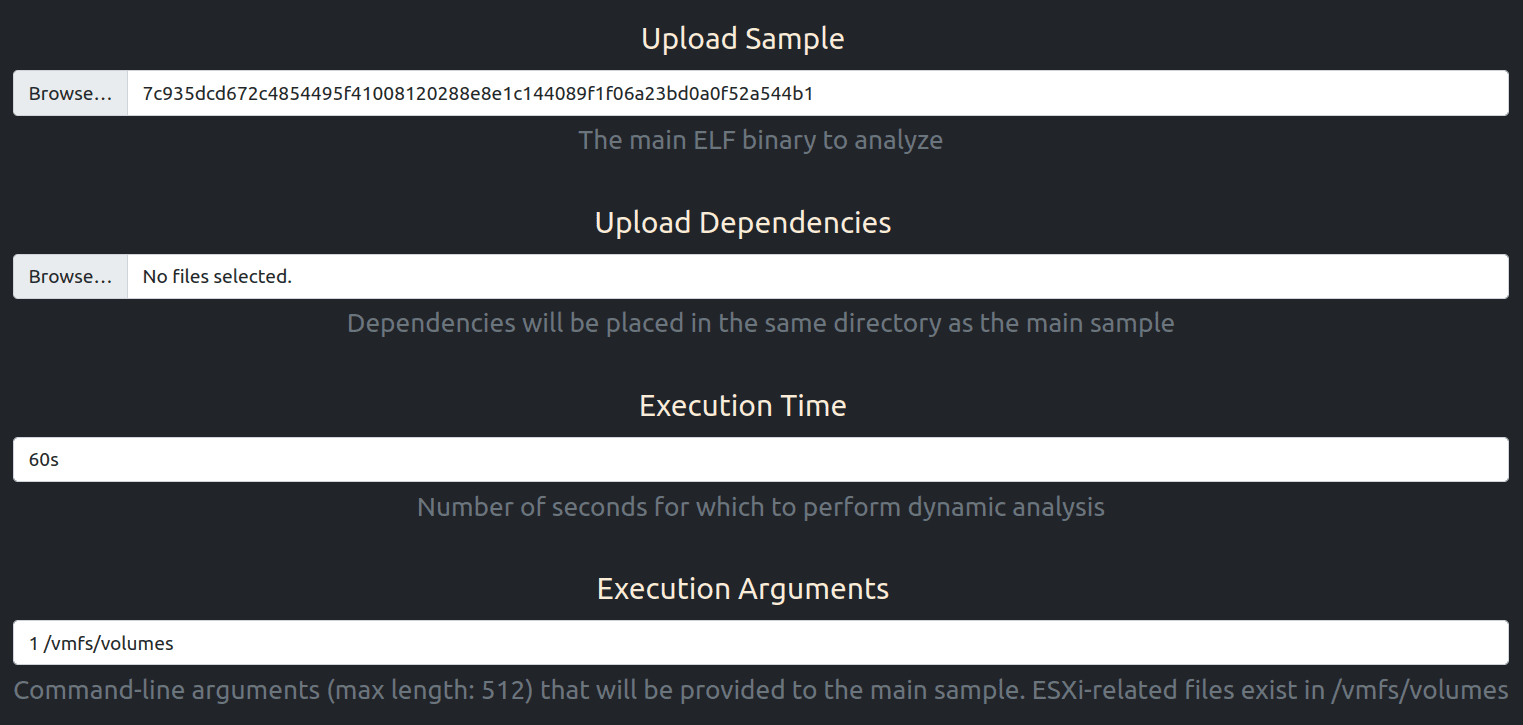
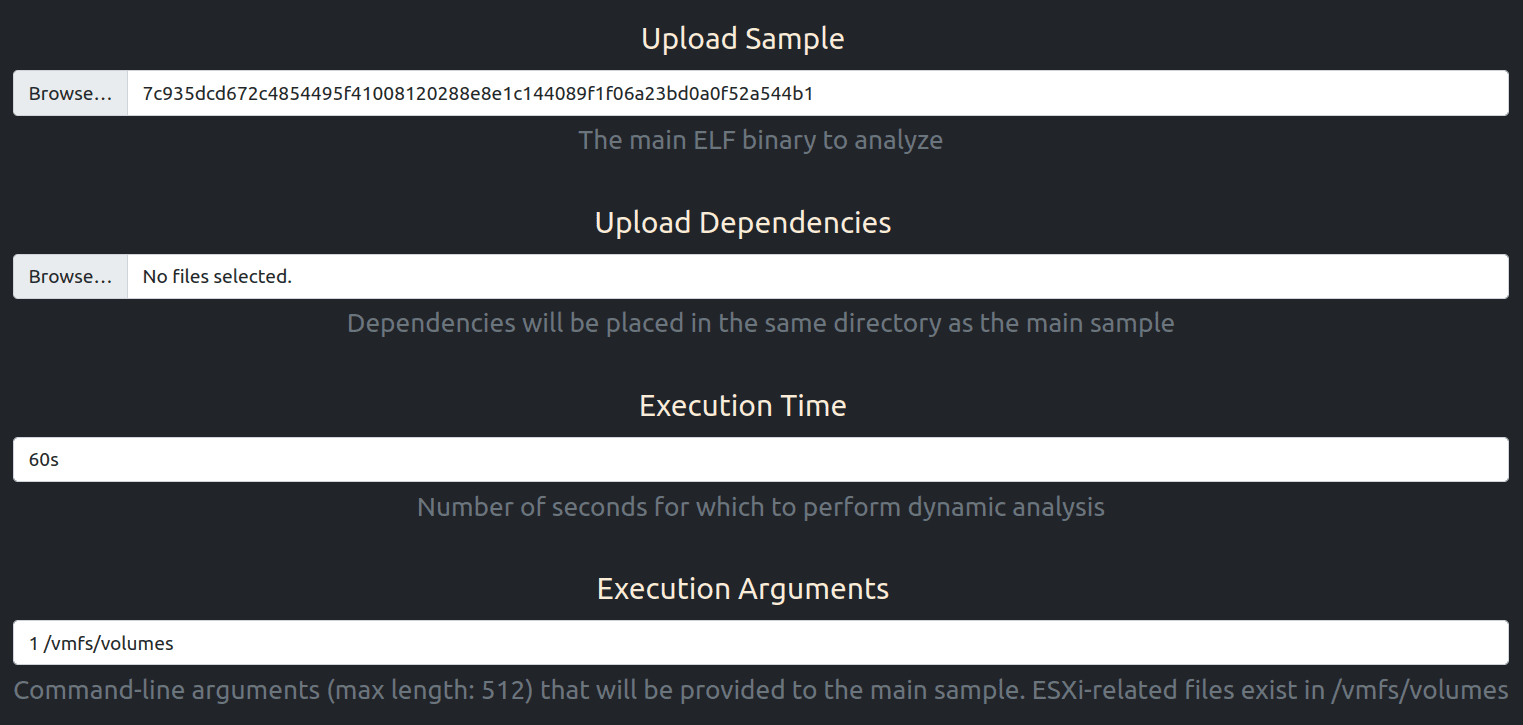
ELFEN is a dockerized sandbox for analyzing Linux (file type: ELF) malware. It leverages an array of open-source technologies to perform both static and dynamic analysis. Results are available through both the GUI and API.
Currently, ELFEN supports the analysis of ELF binaries for the following architectures:
- x86-64
- MIPS 32-bit big/little-endian
- PowerPC 32-bit big-endian
- ARMv5 32-bit little-endian
API
ELFEN provides an API to submit samples and retrieve analysis reports. Ready-to-use scripts are available under the scripts directory.
API Token
To retrieve your API token, visit http://127.0.0.1:8000/api/token/ and login with your username and password. If you’re using the default Django superuser, the credentials are admin:admin.
You should now see two values: access and refresh tokens. The access token will be valid for 7 days after which it will have to be re-generated (visit http://127.0.0.1:8000/api/token/refresh/) using the refresh token (valid for 30 days).
Submitting Samples
Copy the access token into scripts/submit_samples.py. Given a file containing newline-separated full paths to samples, this script can be used to submit them to ELFEN. The output JSON is a mapping between the submitted sample path and ELFEN task UUID.
Retrieving Full Analysis Report
Copy the access token into scripts/get_report_task.py. Given a task UUID, it retrieves the full analysis JSON report.
Retrieving Analysis Report for Given Backend
ELFEN leverages multiple backends to conduct analysis. Some backends like elfheader and capa are associated with static analysis, whereas others such as fileops, c2config are associated with dynamic analysis. Reports can be retrieved for a given backend using scripts/get_report_backend.py. Copy the access token into the script.
Install
Copyright (C) 2023 nikhilh-20