enum4linux-ng v1.3.2 releases: enumerating information from Windows and Samba systems

enum4linux-ng
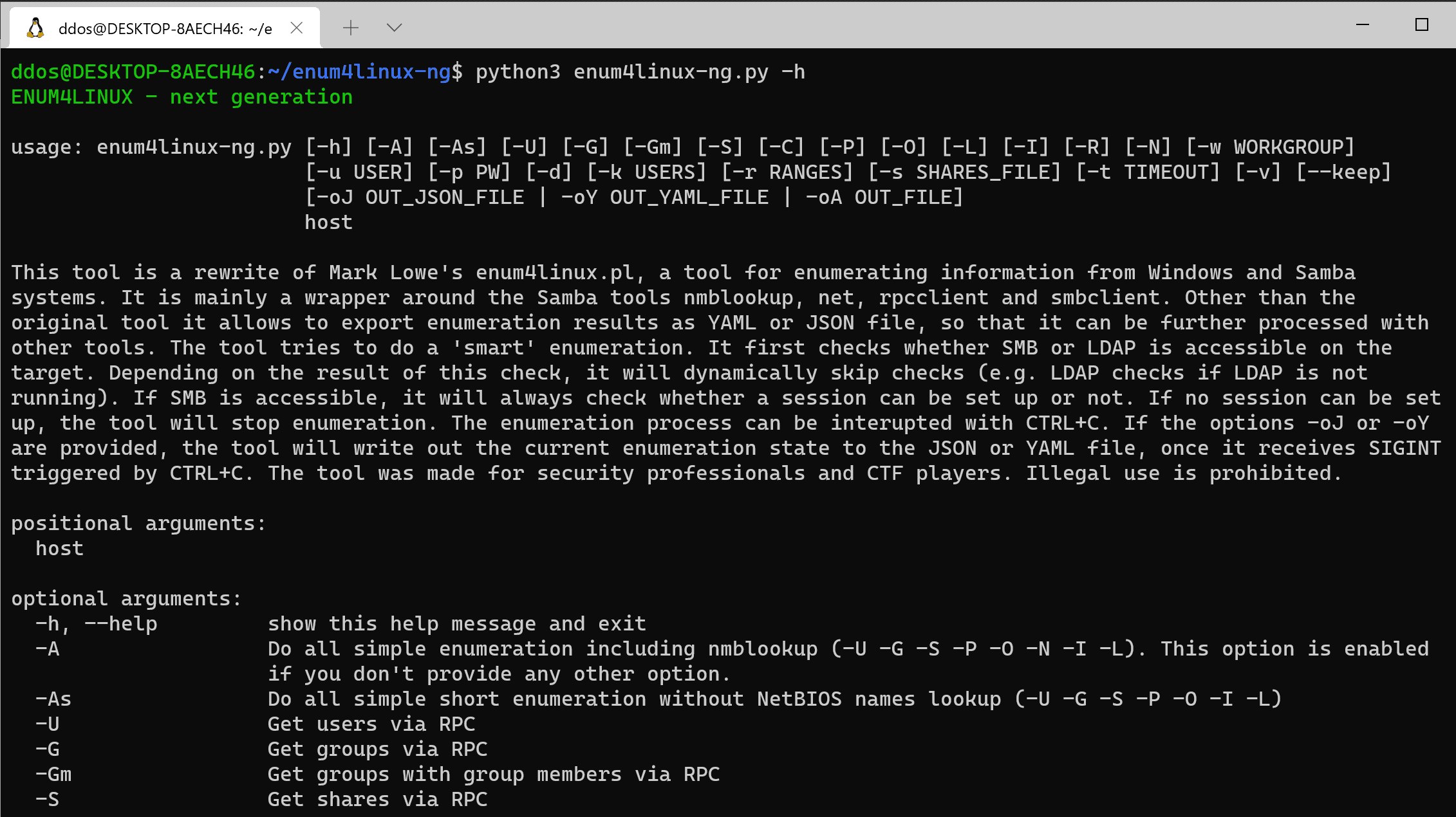
enum4linux-ng.py is a rewrite of Mark Lowe’s (former Portcullis Labs now Cisco CX Security Labs) enum4linux.pl, a tool for enumerating information from Windows and Samba systems, aimed at security professionals and CTF players. The tool is mainly a wrapper around the Samba tools nmblookup, net, rpcclient, and smbclient.
I made it for educational purposes for myself and to overcome issues with enum4linux.pl. It has the same functionality as the original tool (though it does some things differently). Other than the original tool it parses all output of the Samba tools and allows to the export of all findings as YAML or JSON files. The idea behind this is to allow other tools to import the findings and further process them. It is planned to add new features in the future.
Features
- support for YAML and JSON export
- colored console output (can be disabled via NO_COLOR)
- ldapsearch und polenum are natively implemented
- support for legacy SMBv1 connections
- auto-detection of IPC signing support
- ‘smart’ enumeration will automatically disable tests which would otherwise fail
- timeout support
- SMB dialect checks
- IPv6 support (experimental)
Differences
Some things are implemented differently compared to the original enum4linux. These are important differences:
- RID cycling is not part of the default enumeration (-A) but can be enabled with -R
- parameter naming is slightly different (e.g. -A instead of -a)
Changelog v1.3.2
- Minor code refactoring
- Fix error message when a timeout happens
Use
Demo
This demonstrates a run against Windows Server 2012 R2 standard installation. The following command is being used:
enum4linux-ng.py 192.168.125.131 -u Tester -p ‘Start123!’ -oY out
A user ‘Tester’ with password ‘Start123!’ was created. Firewall access was allowed. Once the enumeration is finished, I scroll up so that the results become more clear. Since no other enumeration option is specified, the tool will assume -A which behaves similarly to the enum4linux -a option. User and password are passed in. The -oY option will export all enumerated data as a YAML file for further processing in out.yaml. The tool automatically detects at the beginning that LDAP is not running on the remote host. It will therefore skip any further LDAP checks which would normally be part of the default enumeration.
The second demo shows a run against Metasploitable2. The following command is being used:
enum4linux-ng.py 192.168.125.145 -A -C
This time the -A and -C options are used. While the first one behaves similarly to enum4linux -a option, the second one will enable the enumeration of services. This time no credentials were provided. The tool automatically detects that it needs to use SMBv1. No YAML or JSON file is being written. Again I scroll up so that the results become more clear.
Install
Copyright (C) 2020 cddmp








