Image credit: Sucuri Blog
A widespread malware campaign is abusing fake Cloudflare verification prompts to trick users into running malicious PowerShell commands that install the notorious LummaStealer Trojan. The campaign is actively leveraging compromised WordPress websites as launchpads for infection.
According to security analyst Ben Martin at Sucuri, this campaign “continues to use WordPress websites as staging grounds to trick website visitors into running malicious powershell commands on their Windows computers in order to infect their machines with LummaStealer trojan malware.”
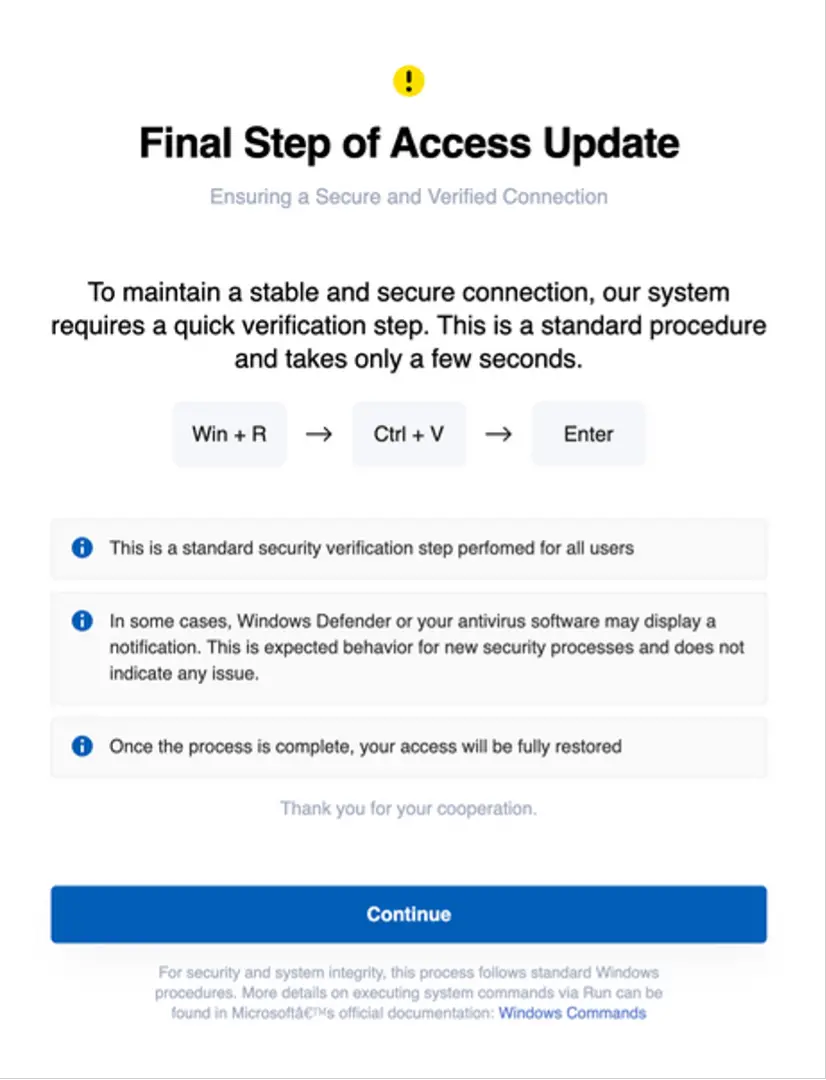
Once a user visits an infected WordPress site, they may encounter a seemingly routine human verification page. But instead of a CAPTCHA, it instructs them to press Windows + R and run a PowerShell command—under the false pretense of running “Windows Defender.”
“In no universe should any user need to ‘Run Windows Defender’ to interact with a website and certainly should not have to run any powershell commands.”

LummaStealer, also known as LummaC2, is an information-stealing Trojan. It collects login credentials, browser cookies, crypto wallet data, and more. The Trojan is designed to remain hidden for as long as possible to maximize stolen data.
“Once the malware has been deployed onto the victim’s computer the attackers have full access and the system is at their mercy.”
The PowerShell command downloaded a payload known as TestLAB.exe, flagged by over 50 antivirus tools as LummaStealer-related. This command:
- Launches a hidden command prompt
- Runs PowerShell without a user profile
- Downloads a malicious .msi installer
- Installs the malware
The infection is powered by fake plugins like:
- ./wp-content/plugins/SwiftPress/SwiftPress.php
- ./wp-content/plugins/nwPostSaver/nwPostSaver.php
These plugins contain base64-encoded and hex-encoded links to malicious payloads hosted on domains like:
- hxxps://qq525f[.]short[.]gy/claud
- hxxps://warther[.]info/collect.php
The malware also creates hidden WordPress admin accounts and uses obfuscated JavaScript injections like the one seen in:
- ./wp-includes/js/jquery/jquery-migrate.min.js
“The malicious plugin also has an admin user generator to act as a backdoor into the WordPress environment… and hides itself from the list of installed plugins.”