FirmWire: full-system baseband firmware analysis platform
FirmWire
FirmWire is a full-system baseband firmware analysis platform that supports Samsung and MediaTek. It enables fuzzing, root-cause analysis, and debugging of baseband firmware images.
FirmWire is the result of a multi-year, cross-university research effort. See the paper for more details.
Technical Background
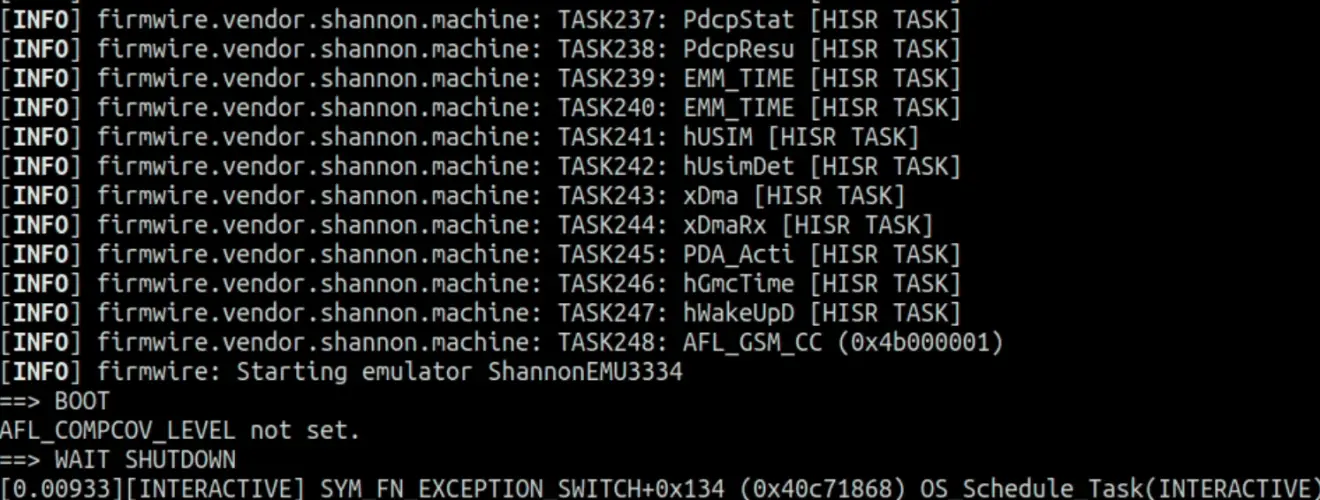
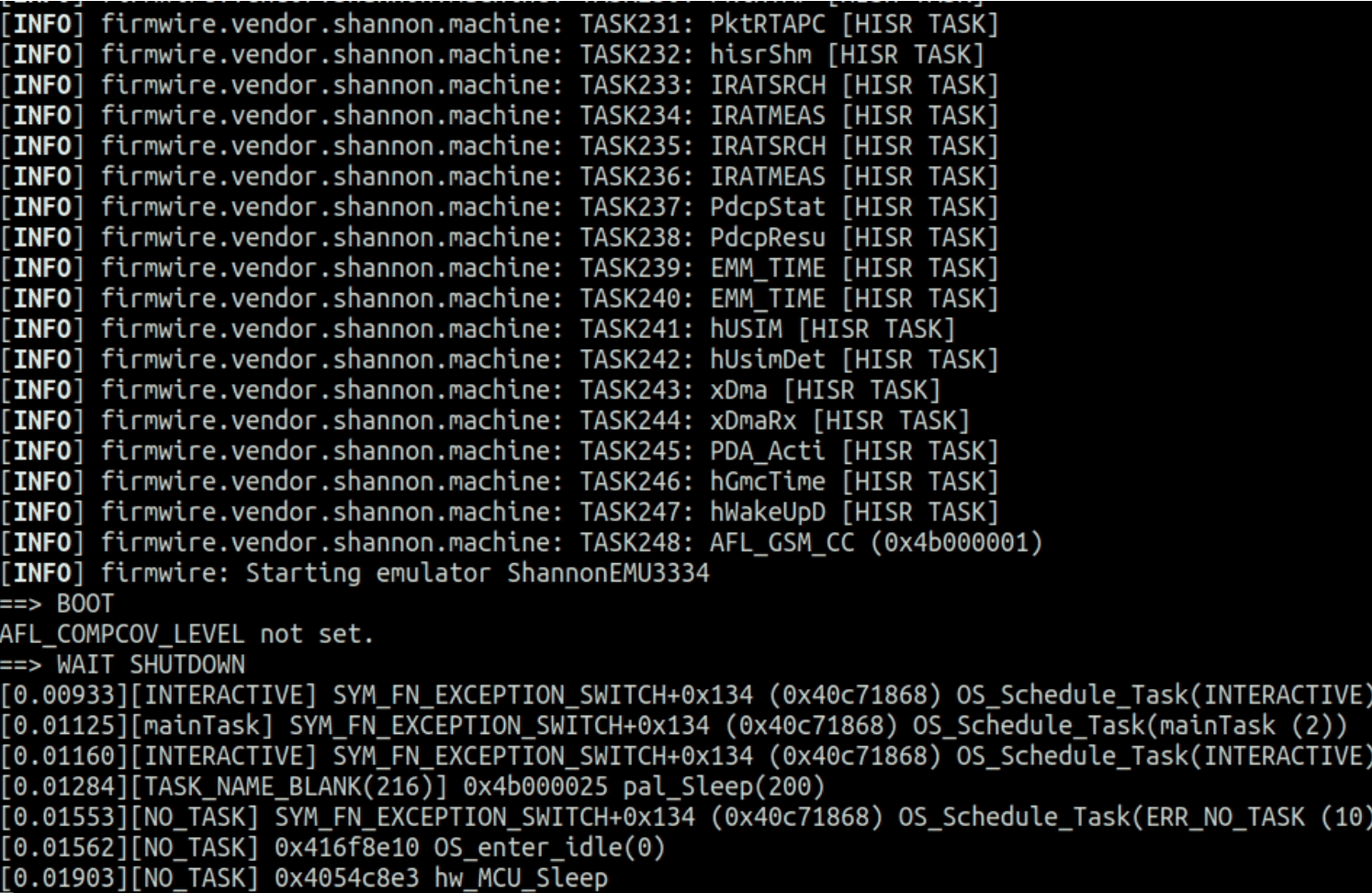
FirmWire is a baseband analysis platform. As input, it takes a baseband firmware image and tries to create an emulation environment for this image on the fly.
Emulation Core
The Emulation Core of FirmWire is built on top of avatar2 and PANDA. The core emulation capabilities are provided by PANDA, while avatar2 is used as middleware to orchestrate the execution state of the emulator, including spin-up, breakpoint registration, and starting/stopping of the emulation. Additionally, we use avatar2’s Python Peripherals to implement peripherals which react on Memory-Mapped I/O accesses.
Under the hood, FirmWire implements vendor-specific machines which use avatar2’s PyPanda target to embed PANDA as a dynamic library in the same process space as the Python Interpreter keeping the required inter-process communication for FirmWire to a bare minimum.
Emulator configuration
PANDA and avatar2 use the so-called configurable machine to enable emulation of arbitrary embedded systems with custom memory mappings. In essence, the embedded systems’ memory map (including ROM, RAM, and peripherals) is described in a JSON file, which gets automatically generated by avatar2 based on individually registered memory ranges. This JSON file is then passed on to PANDA, which uses it to register and emulate the memory ranges accordingly.
Inside FirmWire, we use the configurable machine to create the emulation environments for the target baseband images on the fly. In more detail, our loader is responsible for parsing a binary firmware file and automatically extracting the required memory mappings, for instance by finding pre-defined MPU tables within the binary image.
Install & Use
Copyright (c) 2022, Team FirmWire.






