GATOR v0.5 releases: tool designed to aid in research and exploiting Google Cloud Environments
GATOR
GATOR – GCP Attack Toolkit for Offensive Research, a tool designed to aid in research and exploiting Google Cloud Environments. It offers a comprehensive range of modules tailored to support users in various attack stages, spanning from Reconnaissance to Impact.
Equipped with an extensive collection of modules, GATOR streamlines the process of attack discovery and exploitation. From Reconnaissance to Exfiltration & Impact, this toolkit covers a wide range of attack vectors and techniques.
Modules Implemented
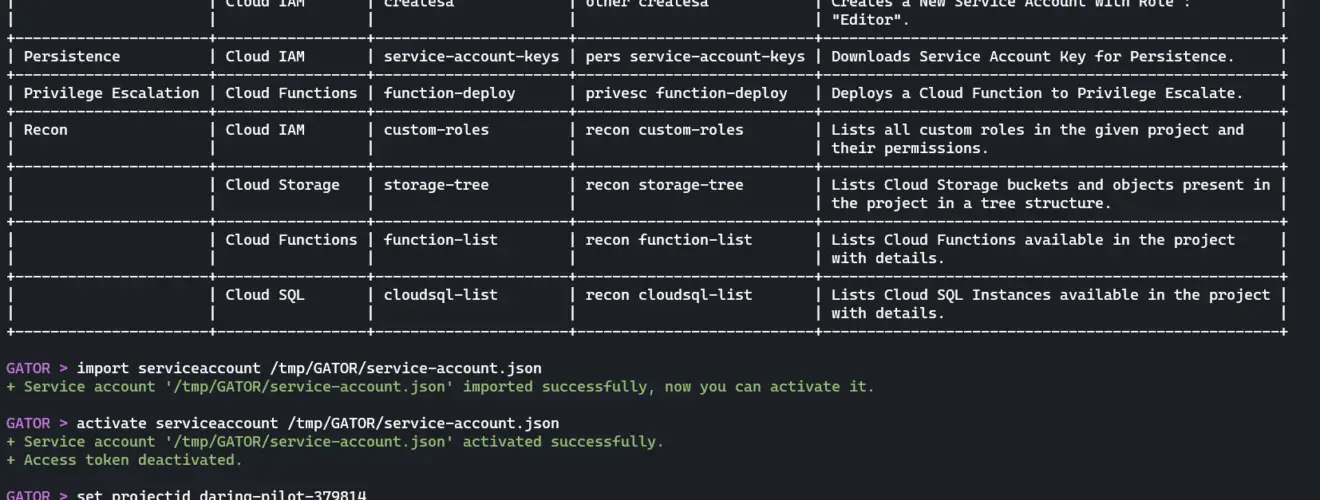
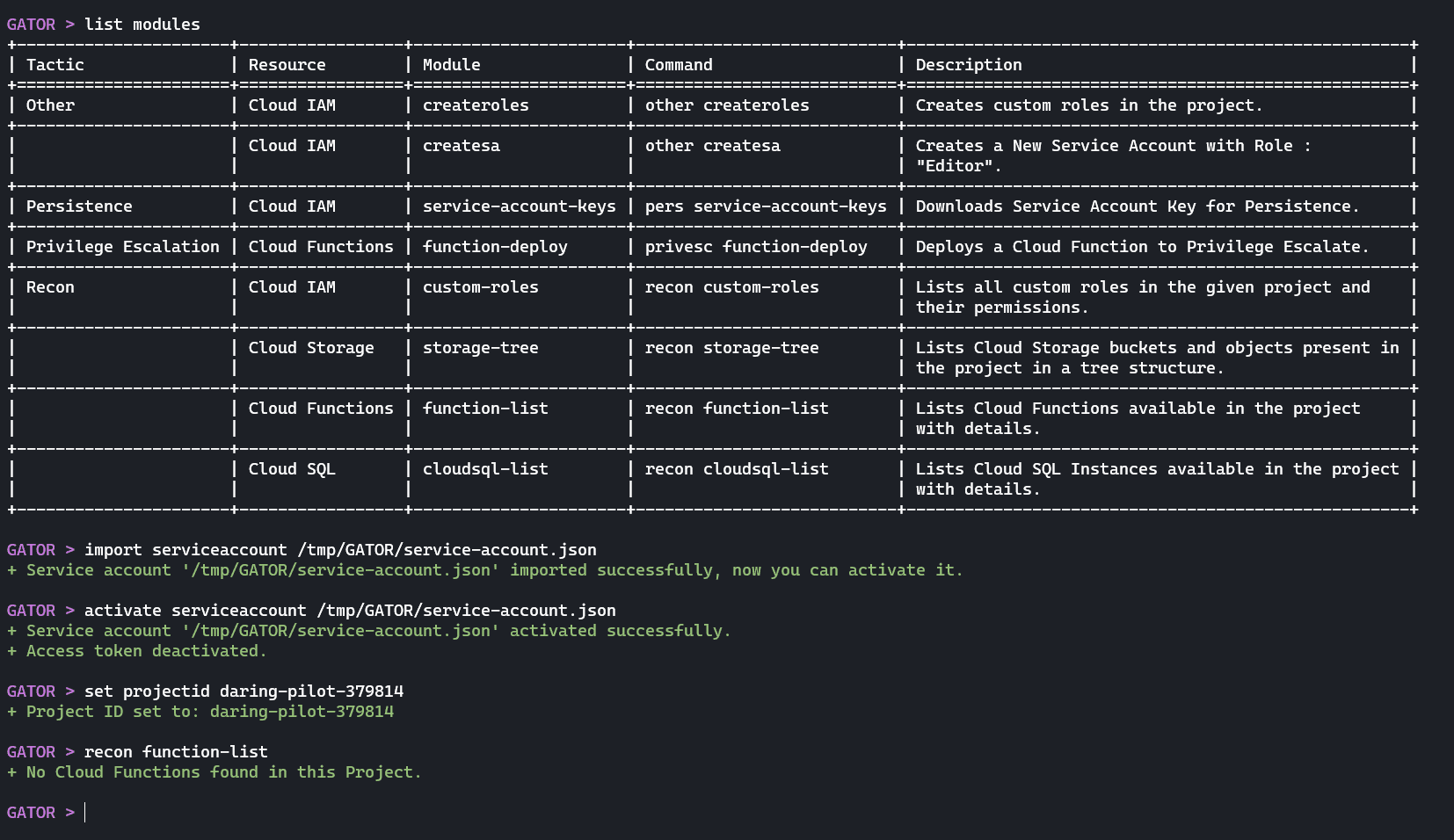
| Tactic | Resource | Modules | Description |
| Recon | Cloud Functions | list-function | List Functions. |
| Cloud IAM | custom-roles | List Custom Roles. | |
| Cloud Storage | storage-tree | List Storage Buckets & Object (Tree). | |
| Cloud SQL | cloudsql-list | List Cloud SQL Instances. | |
| Privilege Escalation | Cloud Functions | function-deploy | PrivEsc via Deploying Cloud Function. |
| Persistence | Cloud IAM | service-account-keys | Persistence via Downloading Service Account Key(s). |
| Other | Cloud IAM | createroles | Create Custom Roles. |
| Cloud IAM | createsa | Create Service Accounts. |
Install & Use
Copyright (c) 2023 Anirban Das






