Ghostbuster
Eliminate dangling elastic IPs by performing analysis on your resources within all your AWS accounts.
Ghostbuster obtains all the DNS records present in all of your AWS accounts (Route53), and can optionally take in records via CSV input, or via Cloudflare.
After these records are collected, Ghostbuster iterates through all of your AWS Elastic IPs and Network Interface Public IPs and collects this data.
By having a complete picture of the DNS records (from route53, file input, or Cloudflare) and having a complete picture of the AWS IPs owned by your organization, this tool can detect subdomains that are pointing to dangling elastic IPs (IPs you no longer own).
The problem
When you are deploying infrastructure to AWS, you may spin up EC2 instances which have an IP associated with them. When you create DNS records pointing to these IPs, but forget to remove the DNS records after the EC2 instance has been given a new IP or destroyed, you are susceptible to subdomain takeover attacks.
There has been a great amount of research done on elastic IP takeovers, where it is possible for attackers to continually claim elastic IPs until they obtain an IP associated with a subdomain of the company they are targeting.
While AWS frequently bans accounts that are attempting to perform this attack pattern, no long-term fix has been released by AWS.
The impact of dangling elastic IP subdomain takeover attacks are more serious than a typical subdomain takeover where you can only control the content being served. With dangling elastic IP takeovers, it is possible for an attacker to do the following:
- Claim SSL certificates for the subdomain
- Listen for traffic on all ports (potentially discovering sensitive information still being sent to the subdomain)
- Run server-side scripts with the ability to steal HTTPOnly cookies, typically leading to a one-click account takeover attack when cookies are scoped to *.domain.com
Project Features
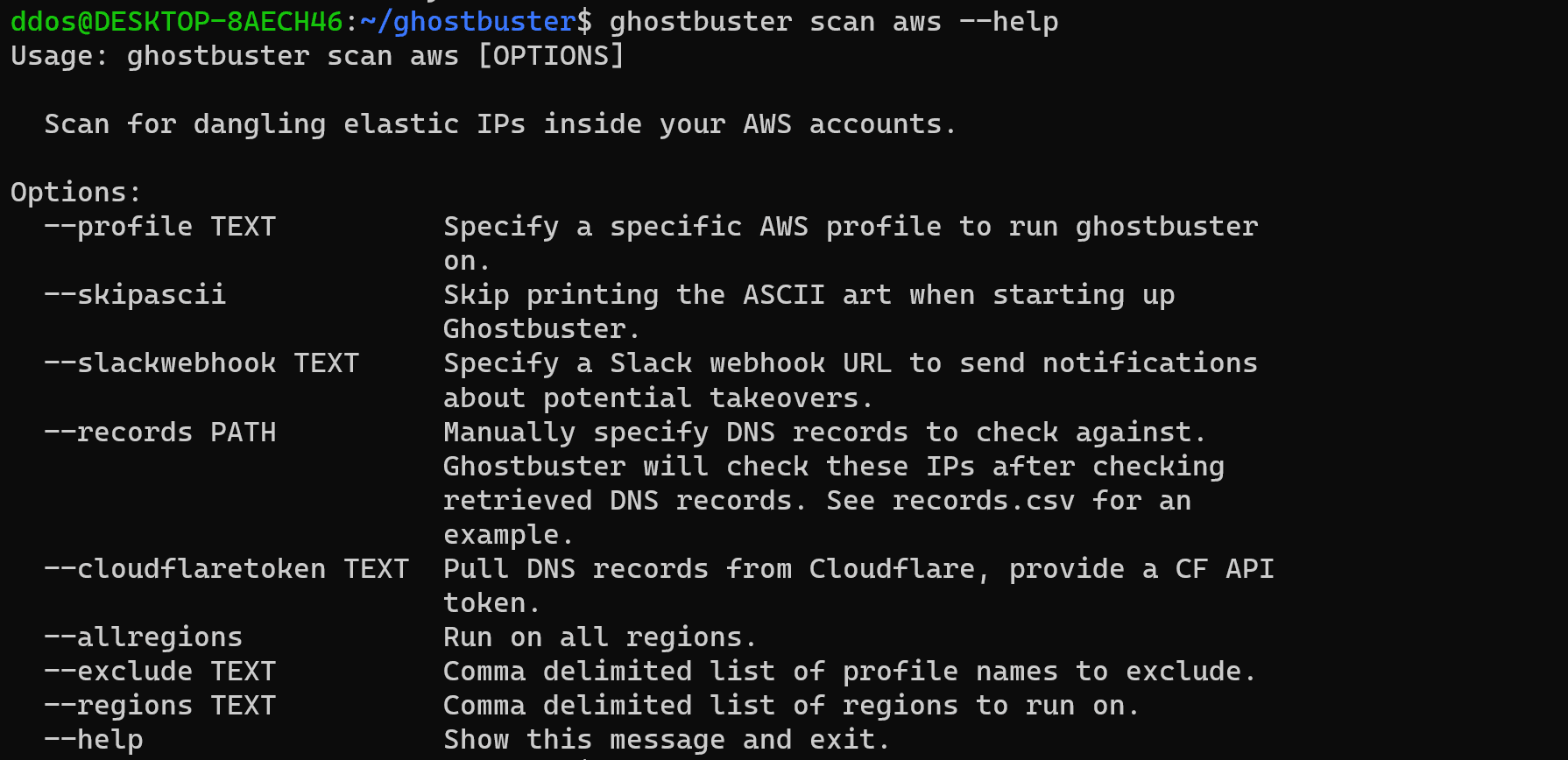
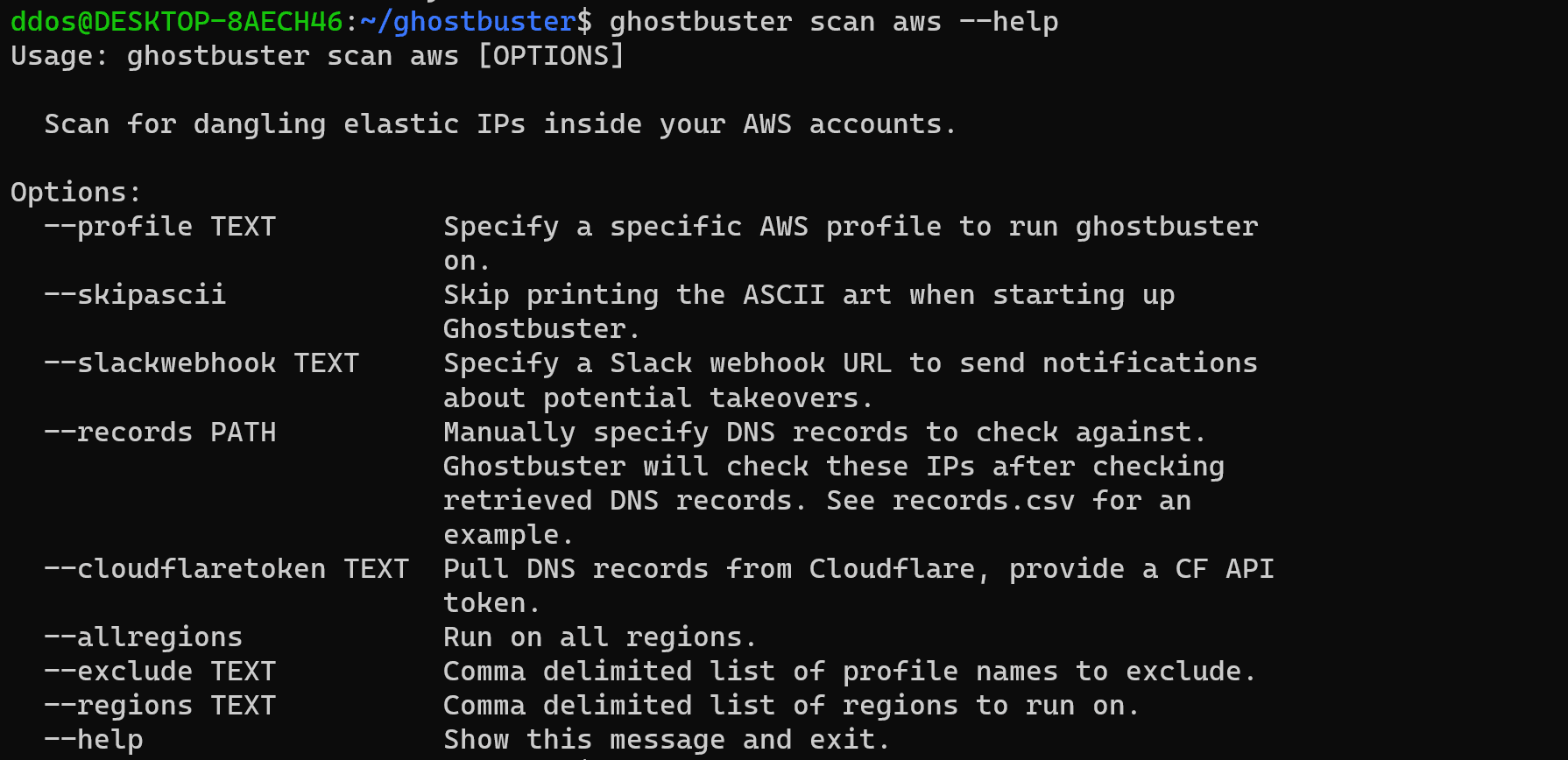
- Dynamically iterates through each AWS profile configured in .aws/config
- Pulls A records from AWS Route53
- Pulls A records from Cloudflare (optional)
- Pulls A records from CSV input (optional)
- Iterate through all regions, a single region, or a comma-delimited list of regions
- Obtains all Elastic IPs associated with all of your AWS accounts
- Obtains all Public IPs associated with all of your AWS accounts
- Cross checks the DNS records, with IPs owned by your organization to detect potential takeovers
- Slack Webhook support to send notifications of takeovers
Important:
In order for this tool to be effective, it must have a complete picture of your AWS environment. If it does not have a complete picture, it will lead to false-positive findings.
Install & Use
Copyright (C) 2022 infosec-au