Recently, Imperva revealed a new cryptocurrency mining attack named “RedisWannaMine”. It used database servers and application servers as attacks.
Imperva said that many mining attacks have been documented so far, but these attacks usually appear to be relatively simple and generally limited in complexity and attack capabilities. However, the newly discovered RedisWannaMine attack is even more complicated in terms of escape skills and attack capabilities. It exhibits worm-like behavior and incorporates advanced attack techniques to increase the success rate of infections on the target server.
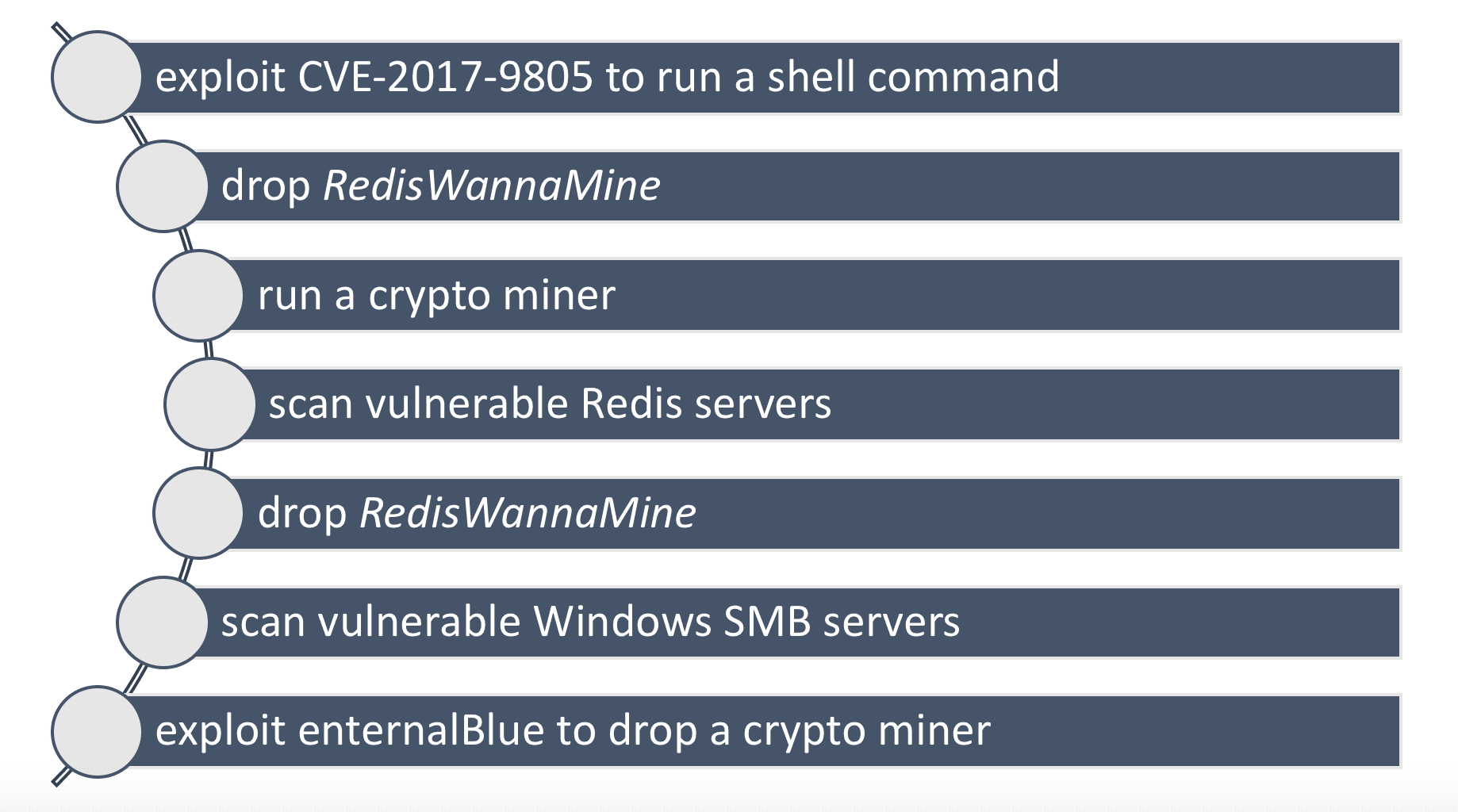
Last week, Imperva monitored a remote code execution (RCE) attack attempting to attempt to download external resources through its deployed sensor network. The attack exploited the Apache Struts vulnerability CVE-2017-9805, a remote code execution vulnerability publicly disclosed last year that affected the Struts REST plug-in through an XStream handler. If used successfully, it will allow an attacker to remotely execute arbitrary code on the application server without authentication.
In detecting the target server, Imperva discovered a series of suspicious files:
The list includes known malicious files, such as minerd; but it also includes some unknown suspicious files, such as transfer.sh.
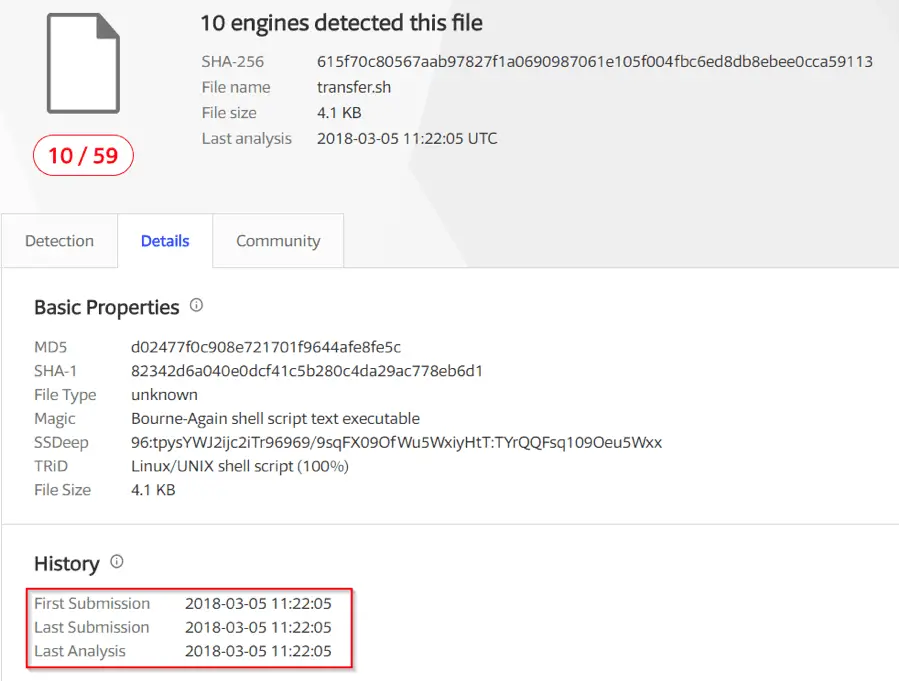
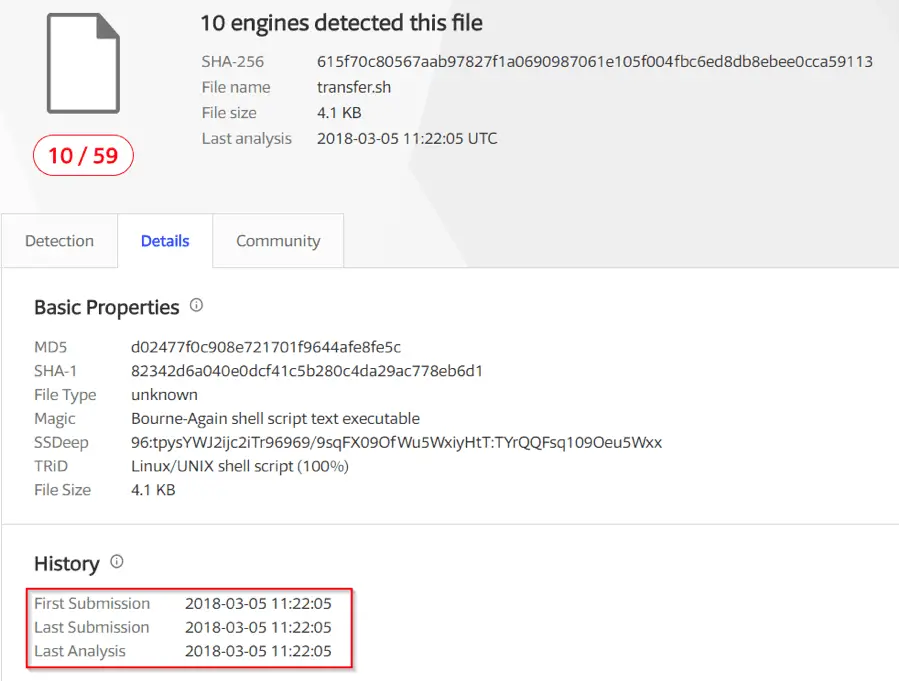
Imperva submitted the hash check of transfer.sh to the VirusTotal website for parsing. The results show that this is a relatively new malicious file, the first submission was detected on March 6, 2018, and was detected by only 10 anti-virus engines.
 Return to monitored Remote Code Execution (RCE) attack activity. The shell script file in the attack is a download program, which is similar in some respects to the older, encrypted download program we know of. This is shown as:
Return to monitored Remote Code Execution (RCE) attack activity. The shell script file in the attack is a download program, which is similar in some respects to the older, encrypted download program we know of. This is shown as:
- It downloads a crypto miner malware from an external location
- It gains persistency in the machine through new entries in crontab
- It gains remote access to the machine through a new ssh key entry in /root/.ssh/authorized_keys and new entries in the system’s iptables
However, Imperva stated that this shell script is not the same as any download program they saw before. It has more new features than other download programs.
The script uses a Linux standard package manager like Apt and Yum to install a lot of software packages (such as Git, Python, Redis-tools, Wget, Gcc, and Make, etc.), which is likely to ensure “self-sufficient” so that there is no need to rely on software libraries in victim devices.
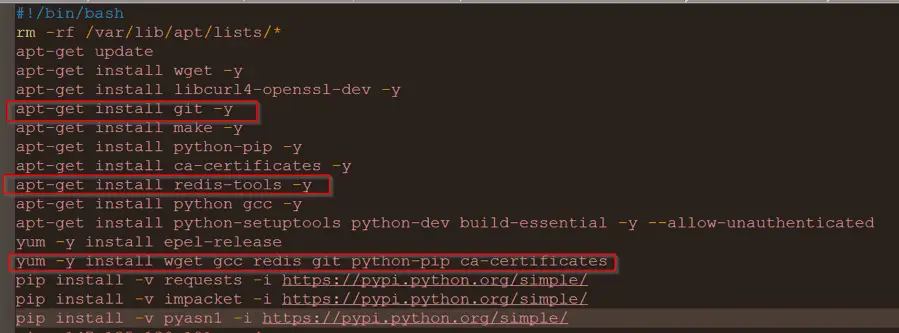
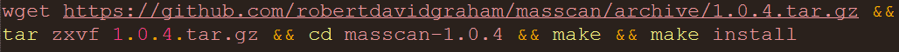
In addition, the script also downloads a publicly available tool named “Masscan” from the Github repository and compiles and installs it. Masscan is described as the “fastest Internet port scanner”, which scans the entire Internet in 6 minutes and sends 10 million packets per second.
 After the download is complete, the script starts a process named “redisscan.sh”. This process will use the aforementioned Masscan tool to discover and infect online exposed Redis servers.
After the download is complete, the script starts a process named “redisscan.sh”. This process will use the aforementioned Masscan tool to discover and infect online exposed Redis servers.
After the script finishes scanning for the Redis server, it starts another scanning process named “ebscan.sh”. This process also uses the Masscan tool to discover and infect online exposed servers. The difference is that it targets the Windows servers that are exposed online and vulnerable to the “Eternal Blue” vulnerability.
EternalBlue (CVE-2017-0144) originally came from the National Security Agency (NSA) and was publicly disclosed by shadow brokers (shadow brokers) in four of the last year, and also in WannaCry, Petya, NotPetya, and other malicious software. Used in communication.
When the script finds a vulnerable server, it launches “ebrun.sh” to run Python code that can trigger the EternalBlue vulnerability. This code creates a malicious VBScript file called “poc.vbs” and runs it, and this VBScript file will download and run the executable “anceinit.exe” from an external location. As we all know, this is a cryptocurrency miner malware.
Although Imperva did not disclose the scale of the attack in the article, which systems may be used. However, it emphasizes the fact that if IT administrators do not install patches for certain well-known vulnerabilities, they may bring cyberattacks to their side at any time.
Source, Image: Imperva