Ingram: webcam device vulnerability scanning tool
Ingram
This is a webcam device vulnerability scanning tool, that already supports Hikvision, Dahua, and other devices.
Installation
- Firstly, clone this repo:
git clone https://github.com/jorhelp/Ingram.git
- Then, go to the repo dir, create a virtual environment, and activate it:
cd Ingram
pip3 install virtualenv
python3 -m virtualenv venv
source venv/bin/activate
- After that, install dependencies:
pip3 install -r requirements.txt
Use
-
Since it is configured in a virtual environment, pls activate the virtual environment before each running
-
You need to prepare a target file, let’s name it input, which contains the targets that will be scanned. The content of the input file can be:
- With the input file, let’s start scanning:
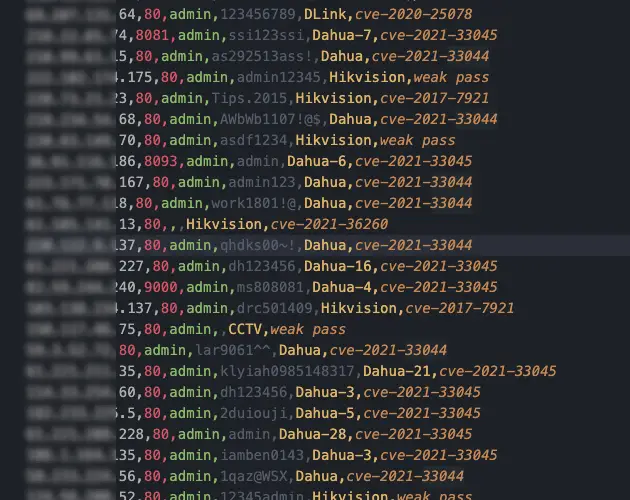
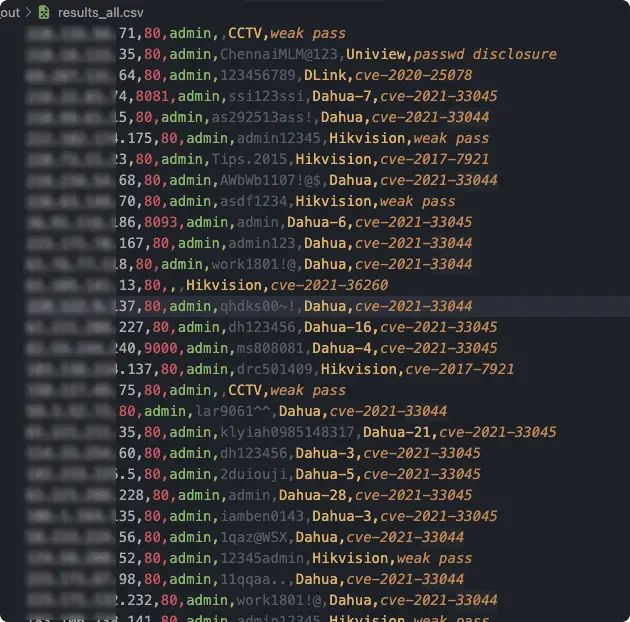
python3 run_ingram.py -i input -o output
If you specify the port like: a.b.c.d:80, then port 80 will be scanned, otherwise common ports will be scanned(defined in Ingram/config.py). You can also override it with the -p argument such as:
python3 run_ingram.py -i input -o output -p 80 81 8000
The number of coroutines can be controlled by the -t argument:
python3 run_ingram.py -i input -o output -t 500
- all arguments:
Port scanner
-
We can use a powerful port scanner to obtain active hosts, thereby reducing the scanning range of Ingram and improving the running speed. The specific method is to organize the result file of the port scanner into the format of ip:port and use it as the input file for Ingram
-
Here is a brief demonstration of masscan as an example (the detailed usage of masscan will not be repeated here).
-
First, use masscan to scan the surviving host on port 80 or 8000-8008 (you can change the port to anything else if you want): masscan -p80,8000-8008 -iL INPUT -oL OUTPUT –rate 8000
-
After masscan is done, sort out the result file: grep ‘open’ OUTPUT | awk ‘{printf”%s:%s\n”, $4, $3}’ > input
-
Then: python run_ingram.py -i input -o output
Copyright (C) 2023 jorhelp
Source: https://github.com/jorhelp/






