ivre v0.9.20 releases: open source network recon framework
IVRE is an open-source framework for network recon. It relies on open-source well-known tools (Nmap, Zmap, Masscan, Bro, and p0f) to gather data (network intelligence), stores it in a database (MongoDB), and provides tools to analyze it.
It includes a Web interface aimed at analyzing Nmap scan results (since it relies on a database, it can be much more efficient with huge scans than a tool like Zenmap, the Nmap GUI, for example).
Feature
- Scan & sniff
IVRE includes tools to run Nmap or Masscan against targets like a network or an address range, a whole country, a specific AS, or the full IPv4 connected address space. It can use Zmap for a fast pre-scan and collect info from network traffic (passively) using Bro, Argus, Nfdump & p0f. - Browse
Use the CLI tools, the Python API, or the Web interface to browse the results. Filter, look for specific services or vulnerable versions, within a specific country or network, quick access to previous results for a specific host, etc. - Analyze
Make the best of your scan results to identify similar hosts and corner-cases. Look for most (and least) common ports, services, or products, and get a quick overview of the address space with the “heatmap”
Demo
Nmap results
Homepage with “heatmap” IP addresses.
Scan result details, using the “heatmap” IP addresses to “zoom” in the address space
Screenshots containing the word “solar” and map
Most common products seen on port 80
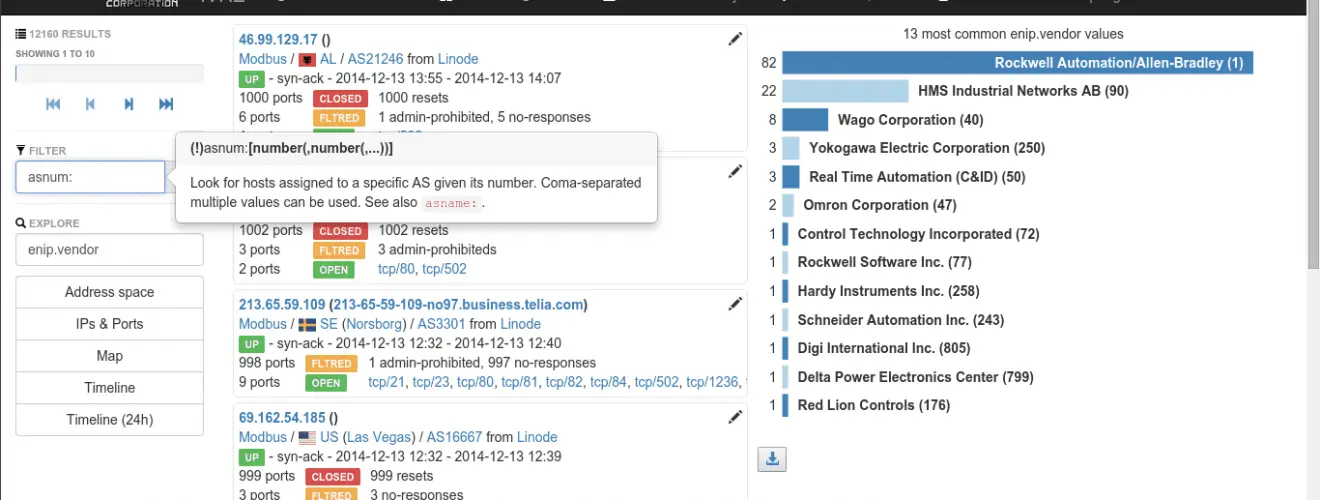
Help tooltip and most common ENIP vendors
Flow analysis
DNS flows with halo to show connected nodes
Flows with details for a specific host
Flows with details for a specific flow
Copyright 2011 – 2017 Pierre LALET
Source: https://github.com/cea-sec/















