Javascript security analysis (JSA)
Javascript security analysis (JSA) is a program for javascript analysis during web application security assessment.
Capabilities of jsa.py:
- Looking for js files inside the first, second, and third-level js files. For example, http(s)://host.com/file.js contains a string “https://host.com/file.js” which could be different from already known 1st level js files and have additional endpoints or secrets.
- Displaying endpoints for the first, second, and third-level js files.
- Modifying found endpoints in the javascript file from /endpoint to http(s)://host_from_js_file.com/endpoint. This approach is handy when you have a massive list of javascript files and want to collect a list of all URLs.
- Excluding and printing 3rd party js files like https://googleapis.com or //facebook.net (most likely 2nd level js file) to reduce script runtime and remove unnecessary endpoints. It is useful to identify 3rd party js files since we can expand our attack surface and exploit vulnerabilities on a 3rd party website to change the javascript file.
- Checking the http code of the second and third level js files using the HEAD method. If 200 – it goes for further processing (because all js files should have a 200 code; otherwise, there will be no loading on the page). If 404 – then such a code indicates a non-existing file that can be uploaded by an attacker for insertion on the target page.
- Removing duplicates – js files and endpoints. By default, most of the js grabbing tools (like subjs, gau, etc) can provide a list of js files containing duplicates. Even if they performed a deduplication procedure, a list could still have duplicates since, for example, http(s)://host.com/file.js and http(s)://host.com/file.js?identifier=random_str are the same js files. Deleting duplicates can significantly boost the program’s performance.
- Removing unnecessary lines with non-word characters (not a-z0-9 – http(s)://domain.com/().|[]{},), 1 word character (like http(s)://domain.com/1|a|1a – most likely to be js variable and not useful endpoint) and such extensions .css|.png|.jpg|.svg|.jpeg|.ico|.gif|.woff|.woff2|.swf.
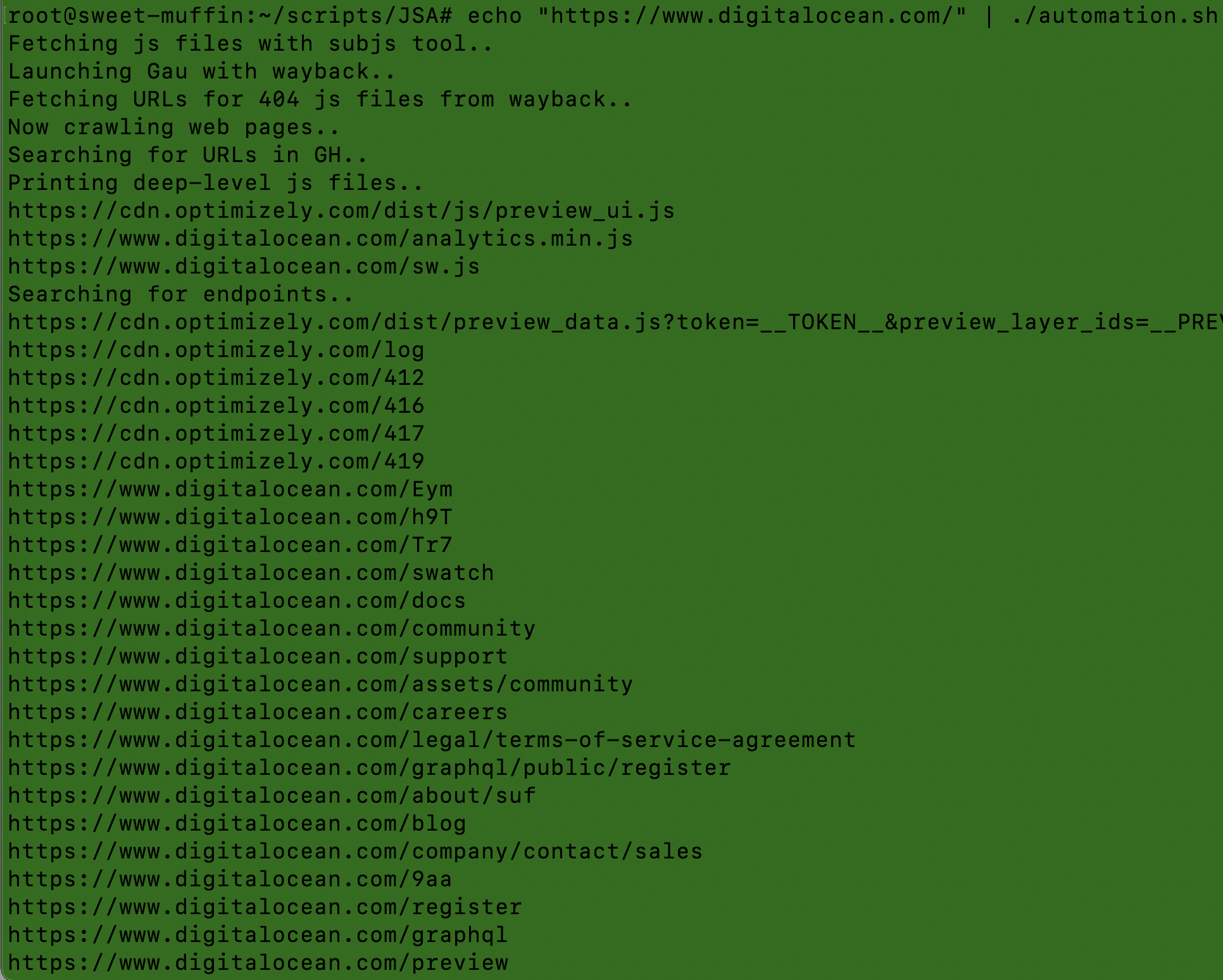
Capabilities of automation.sh:
- Searching for js files for provided host (http(s)://host.tld) in stdin using:
- Wayback Machine (GAU), – launching wayback with mimetype:(application|text)/javascript to reduce execution time;
- subjs tool;
- Crawling (hackrawler) (classic crawling for js files only with depth 1; t could give different results than a subjs tool)
- GitHub search (github.py; it could give some unique results, too but it’s time-consuming considering GH api rate-limit)
- Extraction of js files from js files.
- Printing endpoints.
- Separating 200 OK js files from non-existent and processing Wayback Machine output. If js file parsed from wayback didn’t return 200 OK, we are generating a URL (https://web.archive.org/web/20060102150405if_/$url) to see a file’s content on wayback’s server; it’s ~useless for endpoints discovery but there is a point to search for credentials in the old content – that’s what we’ll do.
- Checking for credentials leakage using nuclei and a custom template containing 957 regexes on:
- Alive js files (200 OK on the target host);
- A copy of deleted js files from Wayback Machine.
- Parameters discovery on found endpoints using modified Arjun (it still needs some improvements).
Usage & installation for jsa.py:
git clone https://github.com/w9w/JSA.git && cd JSA
echo “https://host.com/file.js” | python3 jsa.py
Example for pulling out js files and processing:
echo “https://subdomain.host.com” | subjs | python3 jsa.py
Usage & installation for automation.sh:
chmod +x installation.sh
./installation.sh
copy your github API key to .tokens
echo “http(s)://host.com” | ./automation.sh
Usage for massive and parallel scanning (~lightning-fast execution):
cat ~/lists/domains/host.com/http_s_hosts.txt | subjs | parallel -j 20 ‘echo “{}” | python3 jsa.py’.
Copyright (C) 2020 w9w