The Danish Centre for Cyber Security (CFCS) is warning of increased ransomware activity, exploiting CVE-2023-20269, a vulnerability...
Penetration Testing
GraphRunner GraphRunner is a post-exploitation toolset for interacting with the Microsoft Graph API. It provides various tools...
IDEMIA, a prominent player in this field, recently issued an advisory that highlights critical vulnerabilities in its...
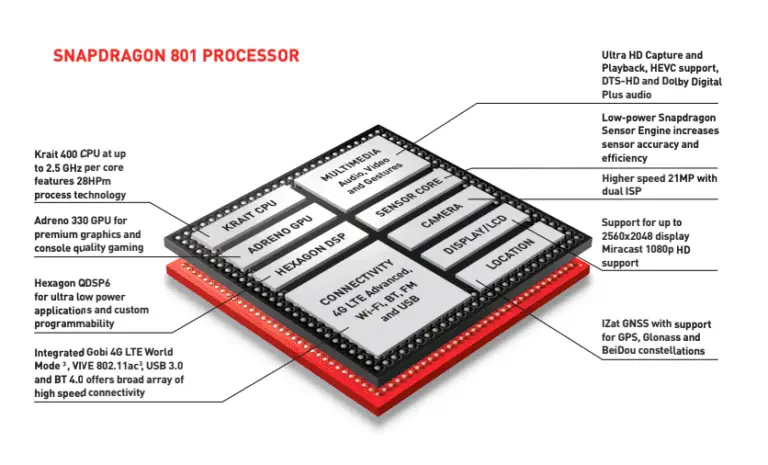
The blog title”Deep Dive: Qualcomm MSM & ARM Mali Kernel 0-day Exploit Attacks of October 2023″ by...
CATSploit CATSploit is an automated penetration testing tool using the Cyber Attack Techniques Scoring (CATS) method that...
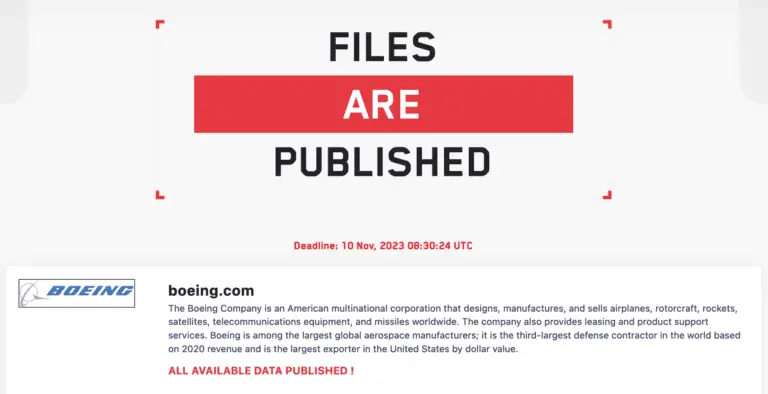
The hacker group LockBit, specializing in ransomware, has published data belonging to the globally renowned aerospace company...
This week, OpenAI experienced several outages that disrupted the normal functioning of the OpenAI API and ChatGPT...
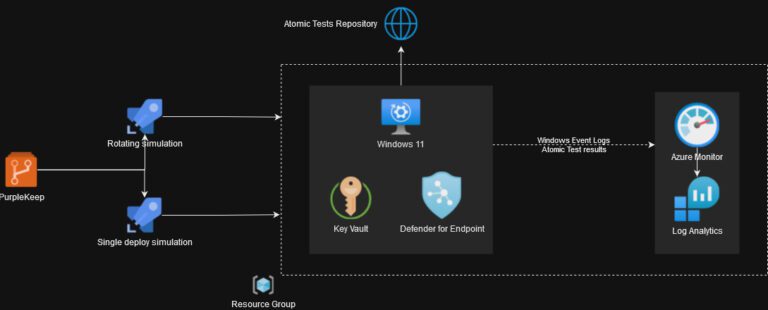
PurpleKeep With the rapidly increasing variety of attack techniques and a simultaneous rise in the number of...
go-exploit: Go Exploit Framework go-exploit is an exploit development framework for Go. The framework helps exploit developers...
Proof-of-concept (PoC) exploit code has been released for a critical CVE-2023-29357 vulnerability allowing the elevation of privilege...
NtRemoteLoad Remote shellcode injector, based on HWSyscalls by ShorSec, leveraging undetectable (currently) indirect native syscalls to inject...
Qlik Sense Enterprise is a powerful business intelligence (BI) and data analytics platform that helps organizations make...
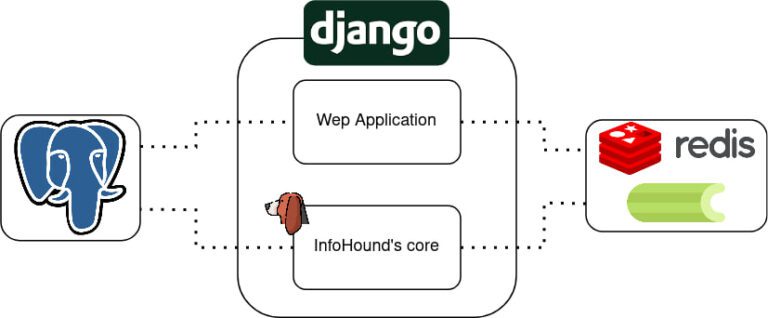
InfoHound – OSINT tool for domain profiling During the reconnaissance phase, an attacker searches for any information...
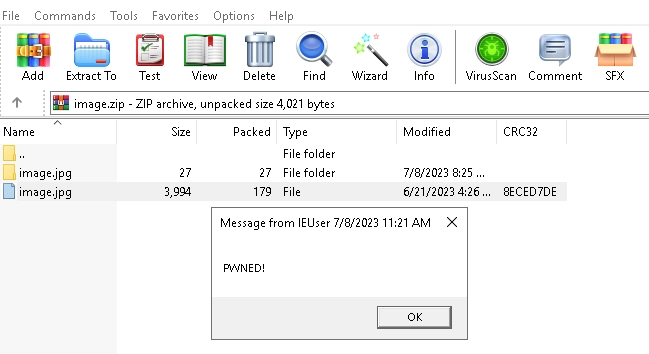
In the digital age, few tools have garnered the universal familiarity of WinRAR. With over 500 million...
Google this week announced the August 2023 security updates for Android devices, with patches for over 48...