Category: Penetration Testing
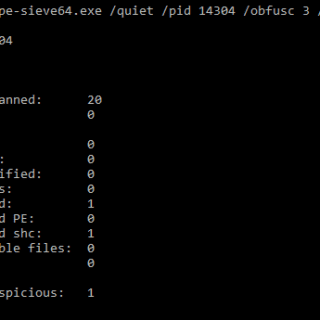
Shelter Shelter is a completely weaponized sleep obfuscation technique that allows you to fully encrypt your in-memory payload making extensive use of ROP. This crate comes with the following characteristics: AES-128 encryption. Whole PE...
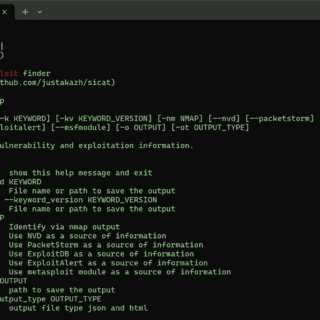
SiCat – The useful exploit finder SiCat is an advanced exploit search tool designed to identify and gather information about exploits from both open sources and local repositories effectively. With a focus on cybersecurity,...
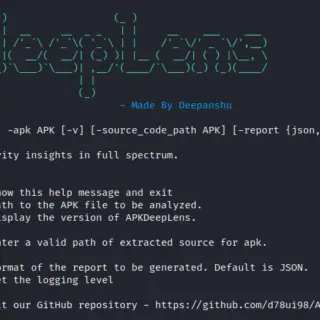
APKDeepLens APKDeepLens is a Python-based tool designed to scan Android applications (APK files) for security vulnerabilities. It specifically targets the OWASP Top 10 mobile vulnerabilities, providing an easy and efficient way for developers, penetration...
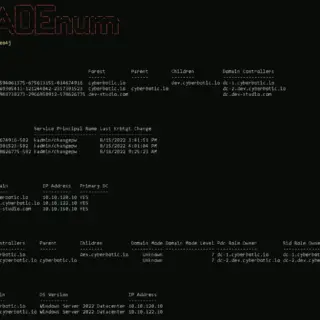
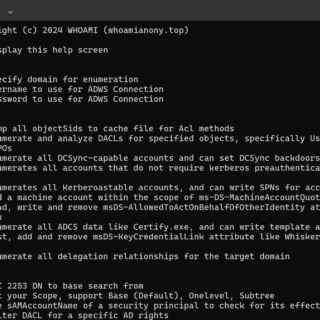
Invoke-ADEnum Active Directory Enumeration Invoke-ADEnum is an Active Directory enumeration tool designed to automate the process of gathering information from an Active Directory environment, leveraging the capabilities of PowerView. With Invoke-ADEnum, you can quickly...
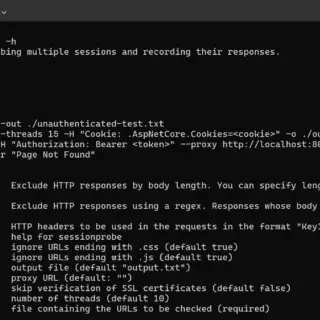
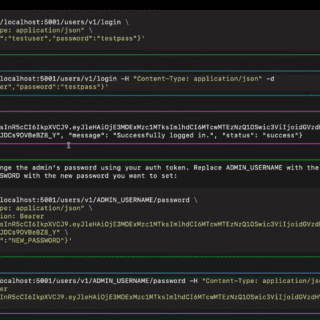
SessionProbe SessionProbe is a multi-threaded pentesting tool designed to assist in evaluating user privileges in web applications. It takes a user’s session token and checks for a list of URLs if access is possible,...
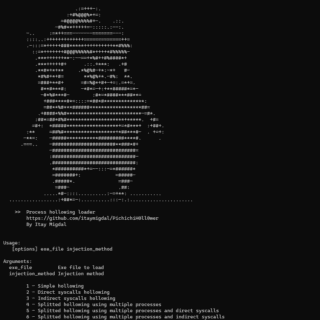
PichichiH0ll0wer Process hollowing loader written in Nim for PEs only PichichiH0ll0wer has some features to protect your payload. Features Configurable builder Payload encrypted and compressed (and optionally splitted) in the hollow loader Supports splitted...
VMware has released urgent patches addressing multiple critical-severity vulnerabilities in ESXi, Workstation, Fusion, and Cloud Foundation. These flaws center around USB controllers and could allow attackers with local administrative privileges on a virtual machine...
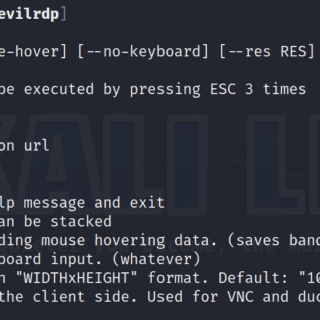
EVILRDP – More control over RDP The evil twin of aardwolfgui using the aardwolf RDP client library that gives you extended control over the target and additional scripting capabilities from the command line. Features Control the mouse...
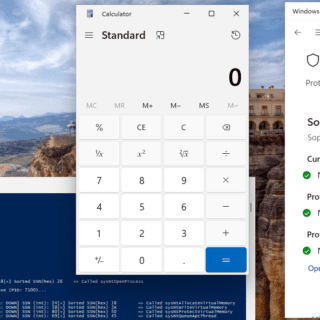
DarkWidow This is a Dropper/Post Exploitation Tool (or can be used in both situations) targeting Windows. Capabilities: Indirect Dynamic Syscall SSN + Syscall address sorting via Modified TartarusGate approach Remote Process Injection via APC...
SharpADWS SharpADWS is an Active Directory reconnaissance and exploitation tool for Red Teams that collects and modifies Active Directory data via the Active Directory Web Services (ADWS) protocol. Typically, enumeration or manipulation of Active...
MultiDump MultiDump is a post-exploitation tool written in C for dumping and extracting LSASS memory discreetly, without triggering Defender alerts, with a handler written in Python. MultiDump supports LSASS dump via ProcDump.exe or comsvc.dll, it offers...
Pentest Muse Building an AI agent that can automate parts of pentesting jobs and provide live suggestions to pentesters. Requirements Python 3.12 or later Necessary Python packages as listed in requirements.txt OpenAI API key Modes...
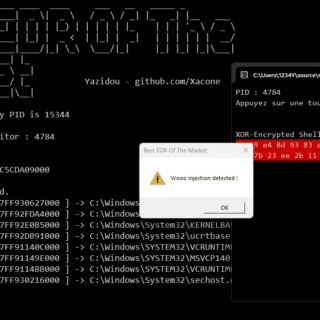
Best EDR Of The Market (BEOTM) BestEDROfTheMarket is a naive user-mode EDR (Endpoint Detection and Response) project, designed to serve as a testing ground for understanding and bypassing EDR’s user-mode detection methods that are...
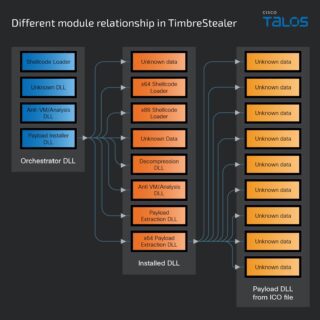
Cisco Talos has discovered a highly targeted and persistent phishing campaign preying on users in Mexico. The attackers are luring potential victims with financial-themed emails tailored to the region and then tricking them into...
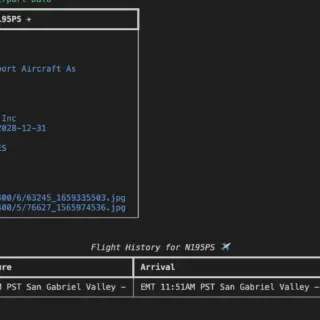
skytrack skytrack is a command-line-based plane spotting and aircraft OSINT reconnaissance tool made using Python. It can gather aircraft information using various data sources, generate a PDF report for a specified aircraft, and convert...