BestEdrOfTheMarket: Little AV/EDR bypassing lab for training & learning purposes
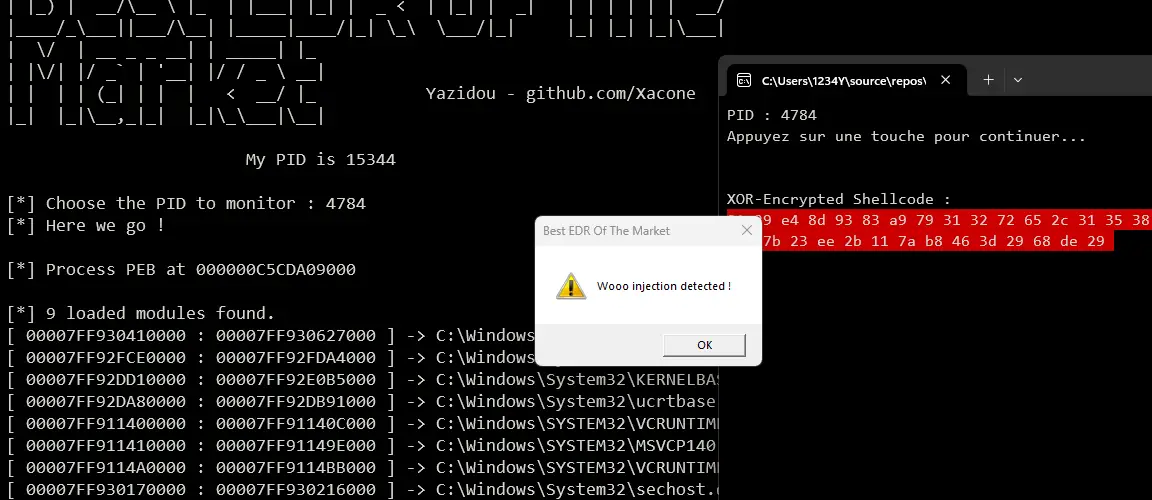
Best EDR Of The Market (BEOTM)
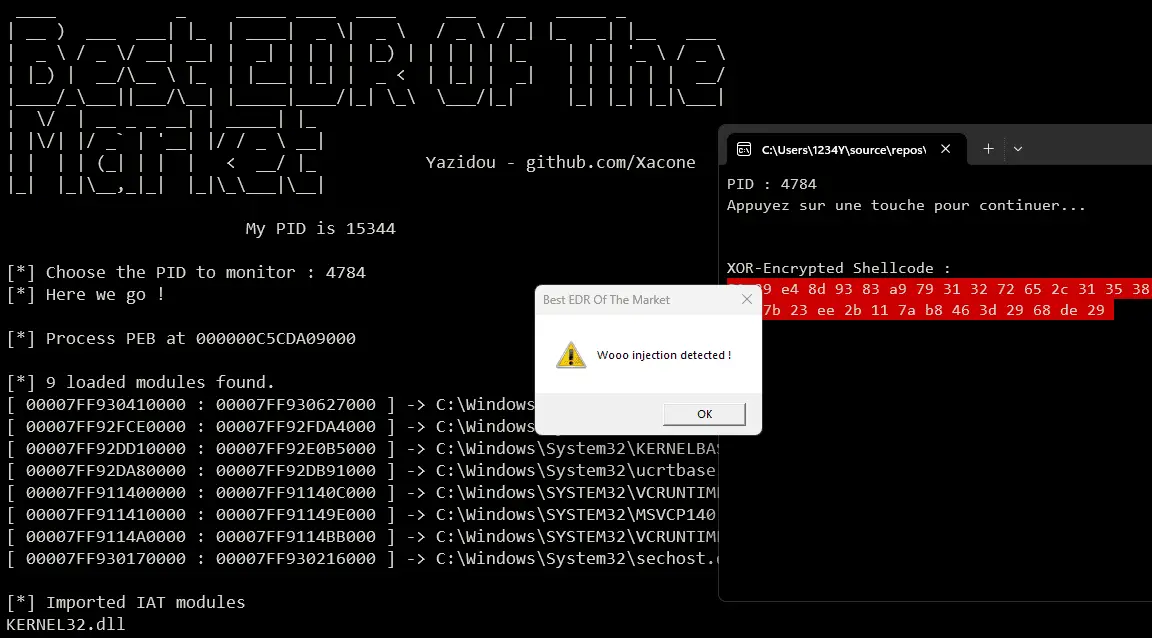
BestEDROfTheMarket is a naive user-mode EDR (Endpoint Detection and Response) project, designed to serve as a testing ground for understanding and bypassing EDR’s user-mode detection methods that are frequently used by these security solutions.
These techniques are mainly based on a dynamic analysis of the target process state (memory, API calls, etc.),
Defensive Techniques ⚔️
- Multi-Levels API Hooking
- SSN Hooking/Crushing
- IAT Hooking
- Shellcode Injection Detection
- Reflective Module Loading Detection
- Call Stack Monitoring
In progress:
- Heap Monitoring
- ROP Mitigation
- AMSI Patching Mitigation
- ETW Patching Mitigation
Structure & Config files
YaroRules.json: Contains a json array filled with the patterns you would like to be identified while monitoring threads call stacks.
TrigerringFunctions.json: Describes the functions that are already hooked or/and to hook:
ℹ️ Note on call stack monitoring: Some NT routines are more appropriate and less exposed to false positives, for instance, it is strongly recommended to monitor the NtCreateFile when targeting an encrypted shellcode loader, but you should avoid it when targeting a reflective loader in favor of NtCreateUserProcess, which is better suited.
- DLLBasedHooking: Not modifiable 🚫, changing its values will have absolutely no effect at all. Information purposes only.
- StackBasedHooking: Modifiable ✅, the functions you specify here will be monitored and their call will trigger an analysis of the calling thread’s call stack.
- SSNCrushingRoutines: Modifiable ✅, the NT-level routines you will specify here will be attributed a corrupted SSN, Be careful of specifying NT-level routines ONLY!
- IATHooking: Modifiable ✅, the functions you specify here will be hooked at IAT level
If you don’t compile your DLLs, take a look at the functions already hooked into the DLLs provided in sources.






