Kansa: A Powershell incident response framework
Kansa
A modular incident response framework in Powershell, useful for data collection and analysis.
What does it do?
It uses Powershell Remoting to run user-contributed, ahem, user-contributed modules across hosts in an enterprise to collect data for use during incident response, breach hunts, or for building an environmental baseline.
Download
git clone https://github.com/davehull/Kansa.git
Usage
- unblock the ps1 files.
ls -r *.ps1 | Unblock-File
Ensure that you check your execution policies with PowerShell. Check Using the Set-ExecutionPolicy Cmdlet for information on how to do so within your environment.
Set-ExecutionPolicy AllSigned | RemoteSigned | Unrestricted - Open an elevated Powershell Prompt (Right-click Run As Administrator)
- At the command prompt, enter:
.\kansa.ps1 -Target $env:COMPUTERNAME -ModulePath .\Modules -Verbose
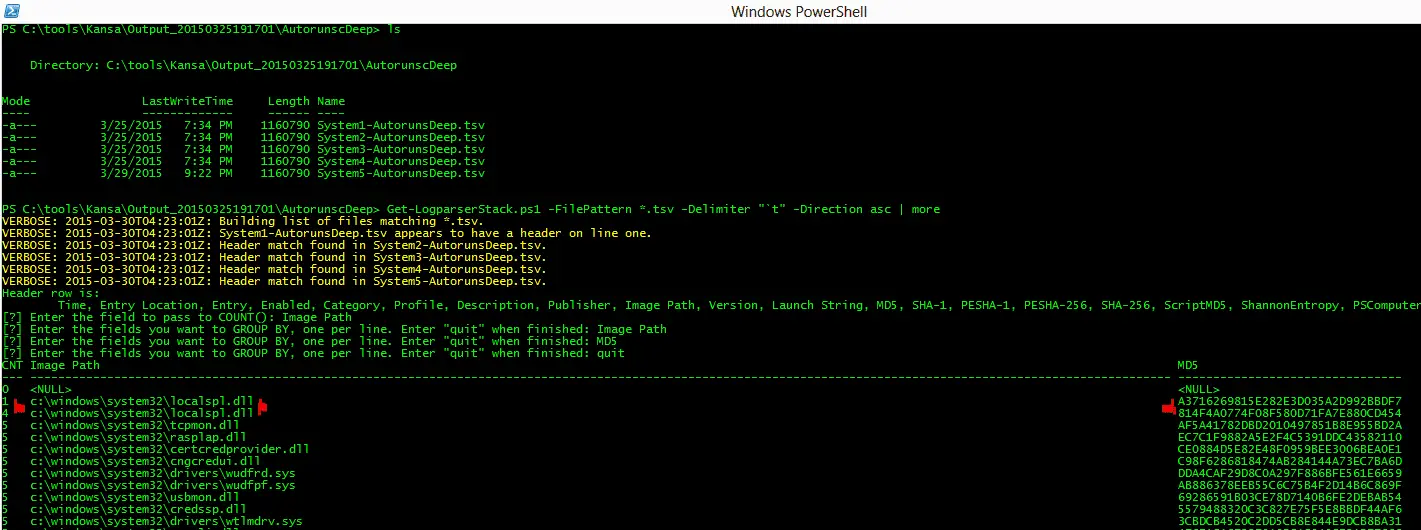
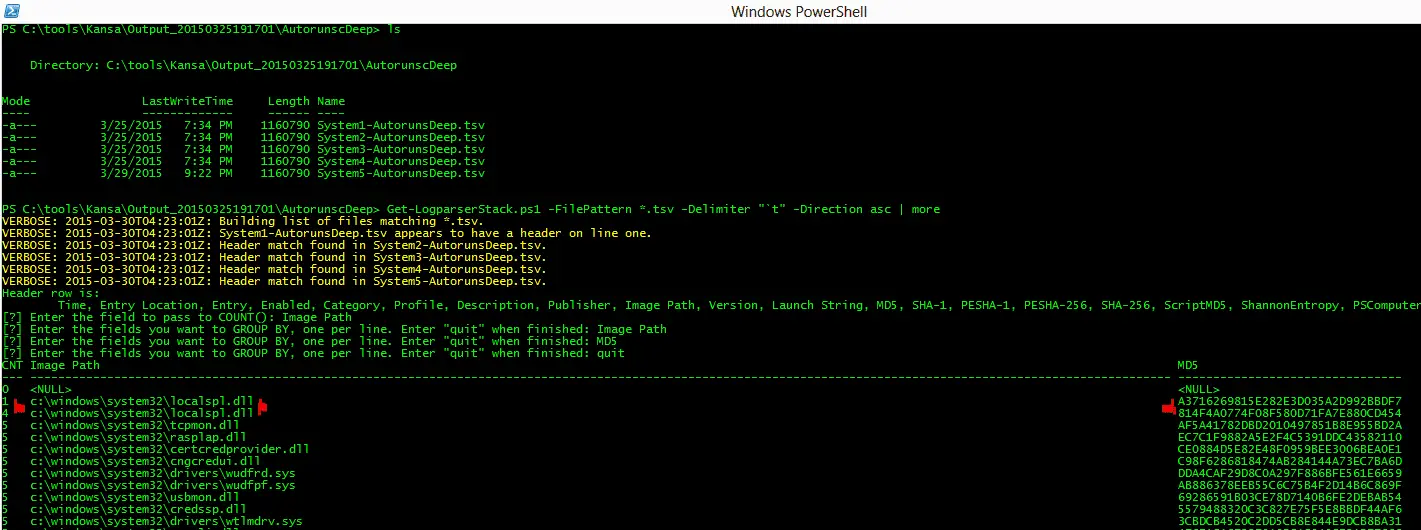
The script should start collecting data or you may see an error about not having Windows Remote Management enabled. If so, do a little searching online, it’s easy to turn on. Turn it on and try again. When it finishes running, you’ll have a new Output_timestamp subdirectory, with subdirectories for data collected by each module. You can cd into those subdirectories and check out the data. There are some analysis scripts in the Analysis directory, but many of those won’t make sense on a collection of data from a single host. Kansa was written for collection and analysis of data from dozens, hundreds, thousands, tens of thousands of systems.
Running Modules Standalone
Kansa modules can be run as standalone utilities outside of the Kansa framework. Why might you want to do this? Consider netstat -naob, the output of the command line utility is ugly and doesn’t easily lend itself to analysis. Running
Modules\Net\Get-Netstat.ps1
as a standalone script will call netstat -naob, but it will return Powershell objects in an easy to read, easy to analyze format. You can easily convert its output to CSV, TSV or XML using normal Powershell cmdlets. Here’s an example:
.\Get-Netstat.ps1 | ConvertTo-CSV -Delimiter “`t” -NoTypeInformation | % { $_ -replace “`”” } | Set-Content netstat.tsv
the result of the above will be a file called netstat.tsv containing unquoted, tab separate values for netstat -naob’s ouput.
Tutorial
- https://trustedsignal.blogspot.com/search/label/Kansa
- http://www.powershellmagazine.com/2014/07/18/kansa-a-powershell-based-incident-response-framework/
Copyright 2014 davehull
Source: https://github.com/davehull/





