Image: TRU
eSentire’s Threat Response Unit (TRU) has detected an intrusion attempt involving a new version of KoiLoader, a malware loader used to facilitate Command and Control (C&C) and deploy Koi Stealer, an information stealer.
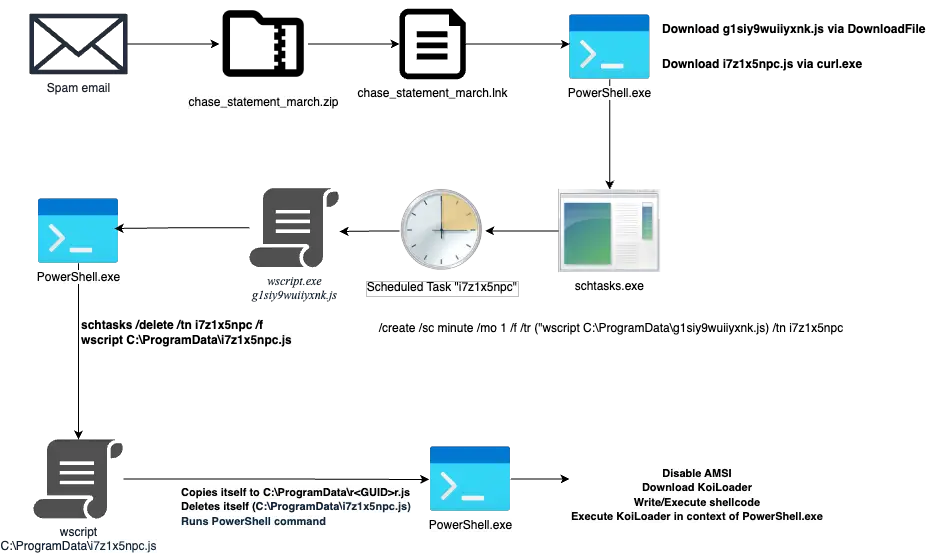
The attack begins with a phishing email carrying a ZIP attachment titled chase_statement_march.zip. Inside: a deceptive .lnk file masquerading as a legitimate document. “The shortcut file makes use of a well-known, low-severity bug in Windows to effectively conceal the command line arguments when viewing the file’s properties,” TRU explains in its detailed report.
Clicking it triggers a hidden PowerShell command that downloads two malicious JScript files: g1siy9wuiiyxnk.js and i7z1x5npc.js. These scripts:
- Establish scheduled tasks using schtasks.exe
- Swap execution contexts to create the illusion of system-trusted processes
- Download further payloads from compromised websites
“This technique is being used to evade detection, as the parent process of wscript.exe appears to be svchost.exe… giving the impression that WScript was launched by a more trustworthy parent process.”
The second script (i7z1x5npc.js) acts as the infection’s engine room:
- Retrieves system info (GUID)
- Creates a unique file path for persistence
- Downloads two PowerShell scripts from casettalecese[.]it
- Uses Invoke-WebRequest and Invoke-Expression to run them
The first script disables Anti-Malware Scan Interface (AMSI); the second loads the KoiLoader binary into memory using shellcode and CreateThread.
Once unpacked, KoiLoader’s second stage checks for:
- Language settings (bails on Russian, Belarusian, Kazakh, etc.)
- VM artifacts like VirtualBox files and display drivers
- Sandbox telltales like dummy Word docs and research environment usernames (e.g., “WDAGUtilityAccount”, “Joe Cage”, or “Harry Johnson”)
- System specs (e.g., RAM ≥ 3 GB, running under PowerShell)
KoiLoader gains persistence by:
- Abusing ICMLuaUtil for a UAC bypass to exclude itself from Defender scanning
- Creating a scheduled task tied to a script named after the machine’s GUID
- Creating a custom mutex based on the volume serial number to prevent duplicate execution
Finally, KoiLoader uses PowerShell to download and execute sd4.ps1 or sd2.ps1, both of which:
- Download the KoiStealer malware
- Execute it via PowerShell
- Begin systematic data theft
KoiStealer is built to extract:
- Saved passwords
- System credentials
- Session cookies
- Browser and application data
KoiLoader uses a custom HTTP-based Command and Control (C2) protocol:
- Registers the infected host with a GUID, build ID, and X25519 public key
- Sends encrypted system info using a derived shared secret
- Enters a loop to poll for commands, one per second
Command options include:
- Running shell or PowerShell commands
- Injecting payloads into explorer.exe or certutil.exe
- Performing shutdowns
- Creating scheduled tasks
- Loading DLLs dynamically
TRU has released a Python-based emulation toolkit for researchers to simulate C2 traffic.
The 2025 variant of KoiLoader demonstrates malware engineering at its finest — blending social engineering, multi-layered scripting, anti-analysis techniques, and custom cryptographic C2 channels.