kubeletmein v1.2 releases: Security testing tool for Kubernetes
Kubeletmein
This is a simple penetration testing tool which takes advantage of public cloud provider approaches to provide kubelet credentials to nodes in a Kubernetes cluster in order to gain privileged access to the k8s API. This access can then potentially be used to further compromise the applications running in the cluster or, in many cases, access secrets that facilitate complete control of Kubernetes.
How it works
kubeletmein is a simple Go binary that is designed to be run from a pod inside your target cluster. Typically this will be either via exploiting a weakness in a web application running on Kubernetes or, perhaps an internal penetration test where the client has given you exec access into a pod.
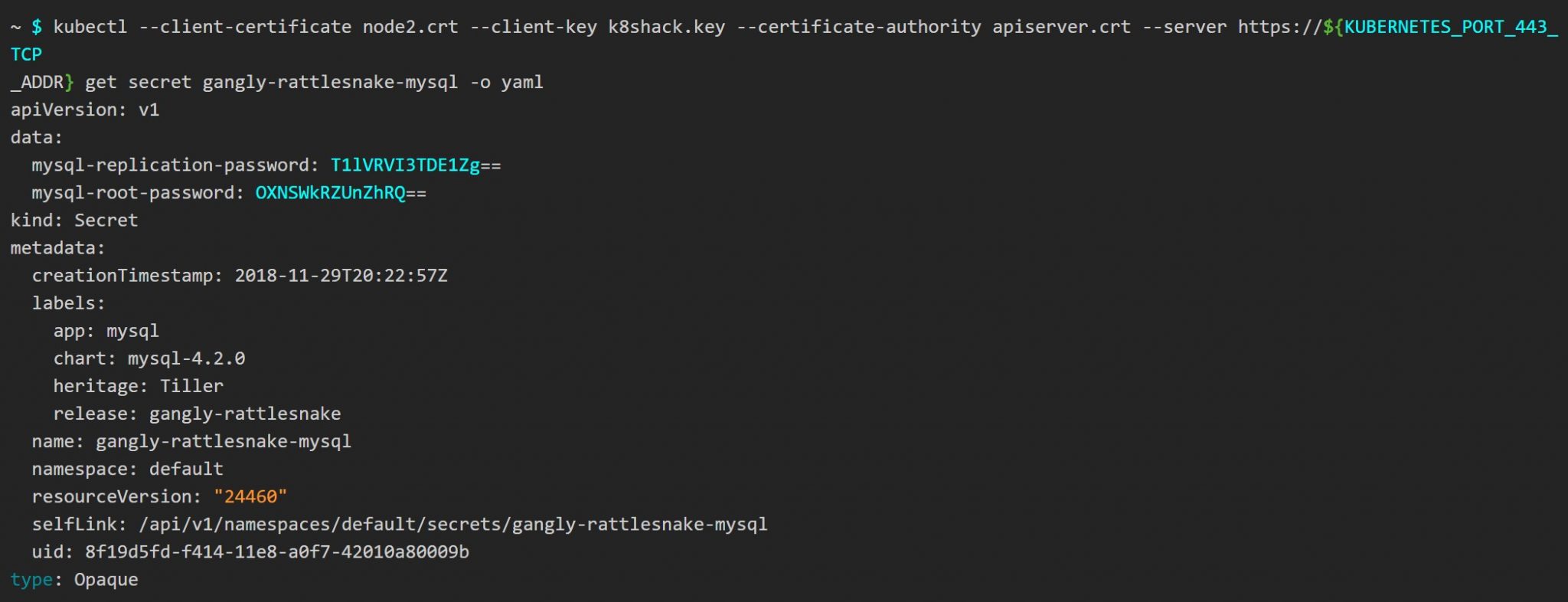
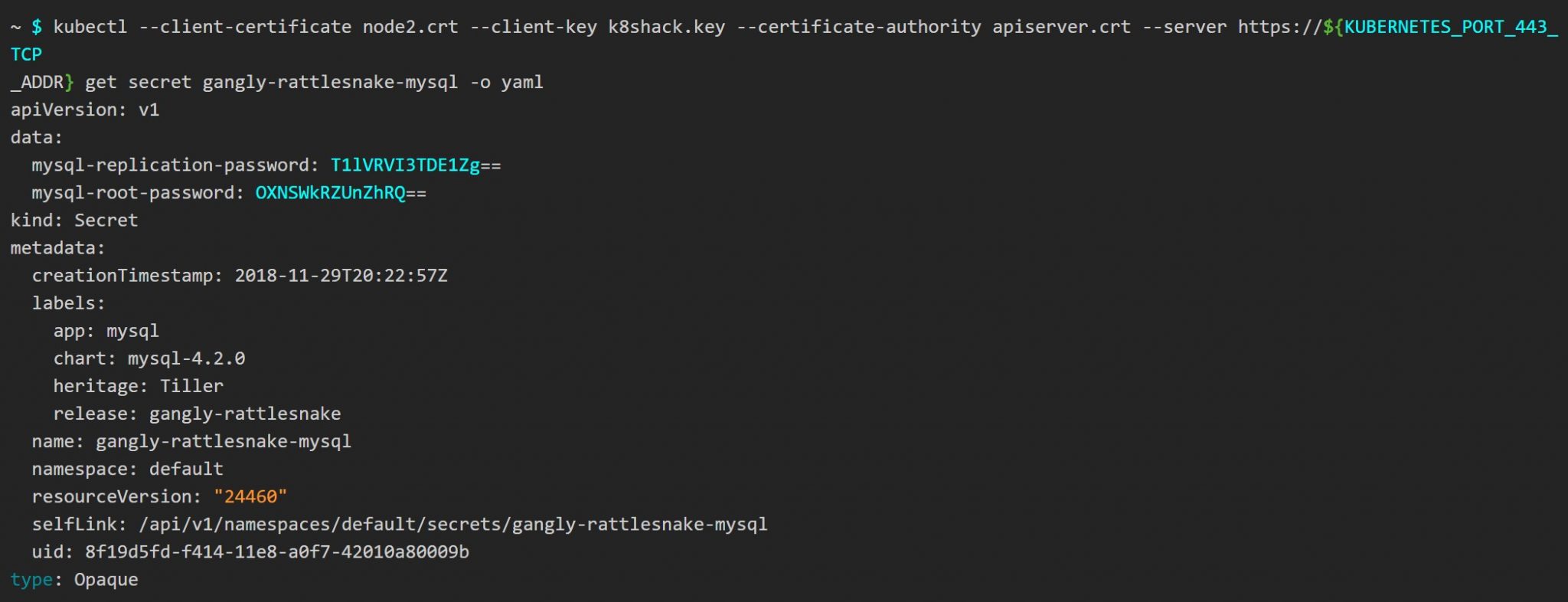
It reads kubelet credentials from the cloud provider metadata and configures a kubeconfig file that you can use with kubectl to access the API.
There’s more info in our blog post here.
Supported providers
GKE
GKE is fully supported and relies on the metadata concealmeant being disabled (the default setting).
EKS
I’m working on support for EKS. It’s actually a lot easier to exploit this on EKS than GKE.
Digital Ocean
By default, DO provides creds by metadata and this cannot be disabled.
AKS
I should probably look at Azure at some point but…Microsoft. 😉
Changelog v1.2
- 913ff74 Add test
- 0e81405 Fix image tag generation
- f9b167a Merge pull request #18 from 4ARMED/eks-update
- eb09691 Move to GHCR
- 3474520 Run incremental build on main
- 1579923 Update to Go 1.19
Use
GKE
On GKE kubeletmein is a two-stage process. First, we write out a bootstrap-kubeconfig using the certificates and key from the kube-env instance attribute. Then we generate a certificate signing request and use the bootstrap config to submit it to the API for approval.
Then we download the certificate and configure kubeconfig.
Now you can use the kubeconfig, as it suggests.
Digital Ocean
Now generate the kubeconfig with a downloaded cert
Download
Copyright (C) 2018 4ARMED
Source: https://github.com/4ARMED/





