Kunyu v1.7.2 releases: More efficient corporate asset collection
Kunyu
Kunyu (kunyu), whose name is taken from , is actually a professional subject related to geographic information, which counts the geographic information of the sea, land, and sky. The same applies to cyberspace. The same is true for discovering unknown and fragile assets. It is more like a cyberspace map, which is used to comprehensively describe and display cyberspace assets, various elements of cyberspace, and the relationship between elements, as well as cyberspace and real space. The mapping relationship. So I think “Kun Yu” still fits this concept.
Kunyu aims to make corporate asset collection more efficient and enable more security-related practitioners to understand and use cyberspace surveying and mapping technology.
Application scenario
For the use of kunyu, there can be many application scenarios, such as:
- Forgotten and isolated assets in the enterprise are identified and added to security management.
- Perform quick investigation and statistics on externally exposed assets of the enterprise.
- Red and blue are used against related requirements, and batch inspections of captured IPs are performed.
- Collect vulnerable assets in batches (0day/1day) for equipment and terminals within the impact.
- Information on sites involved in new-type cybercrime cases is quickly collected and merged for more efficient research, judgment, and analysis.
- Statistic and reproduce the fragile assets on the Internet that are affected by related vulnerabilities.
- …….
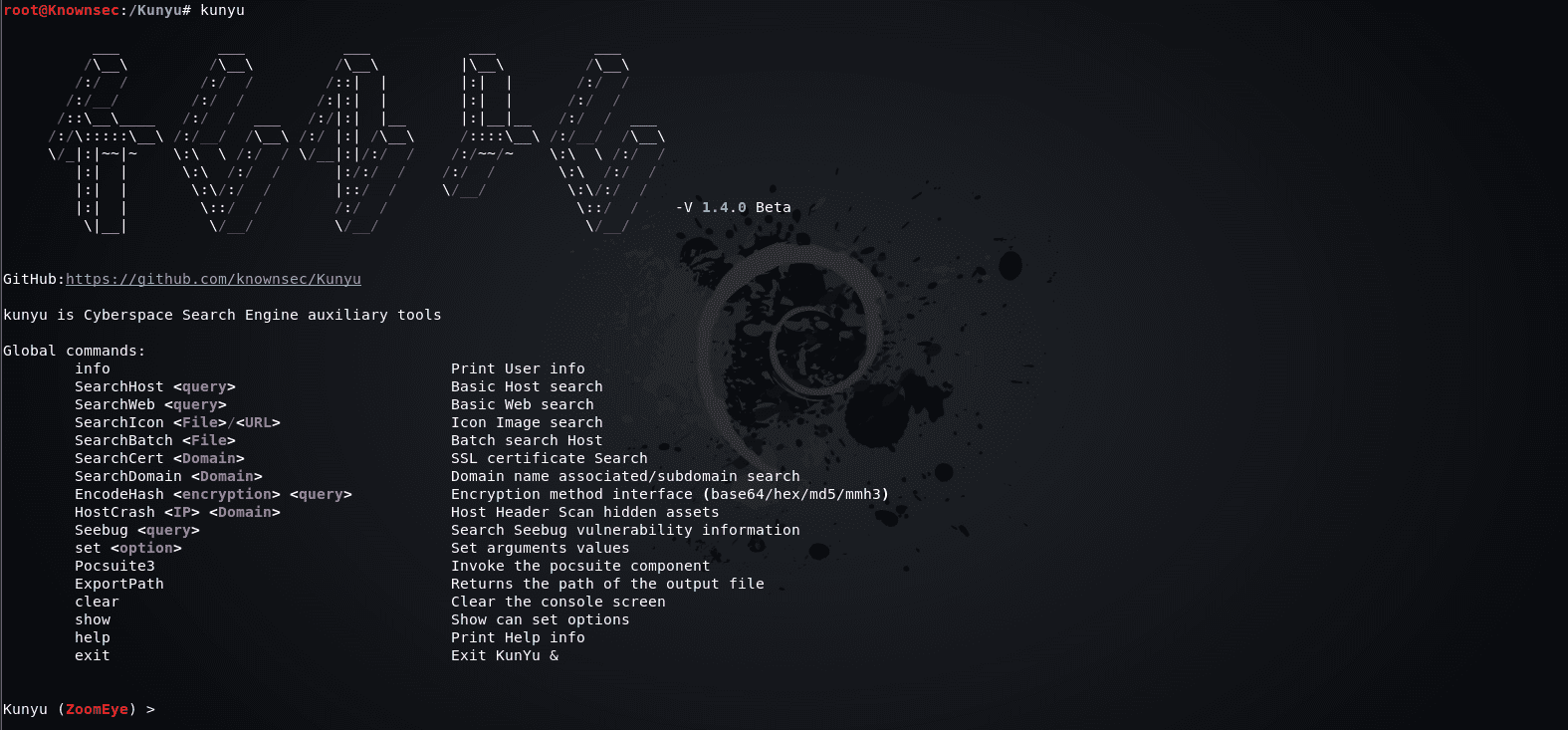
Use
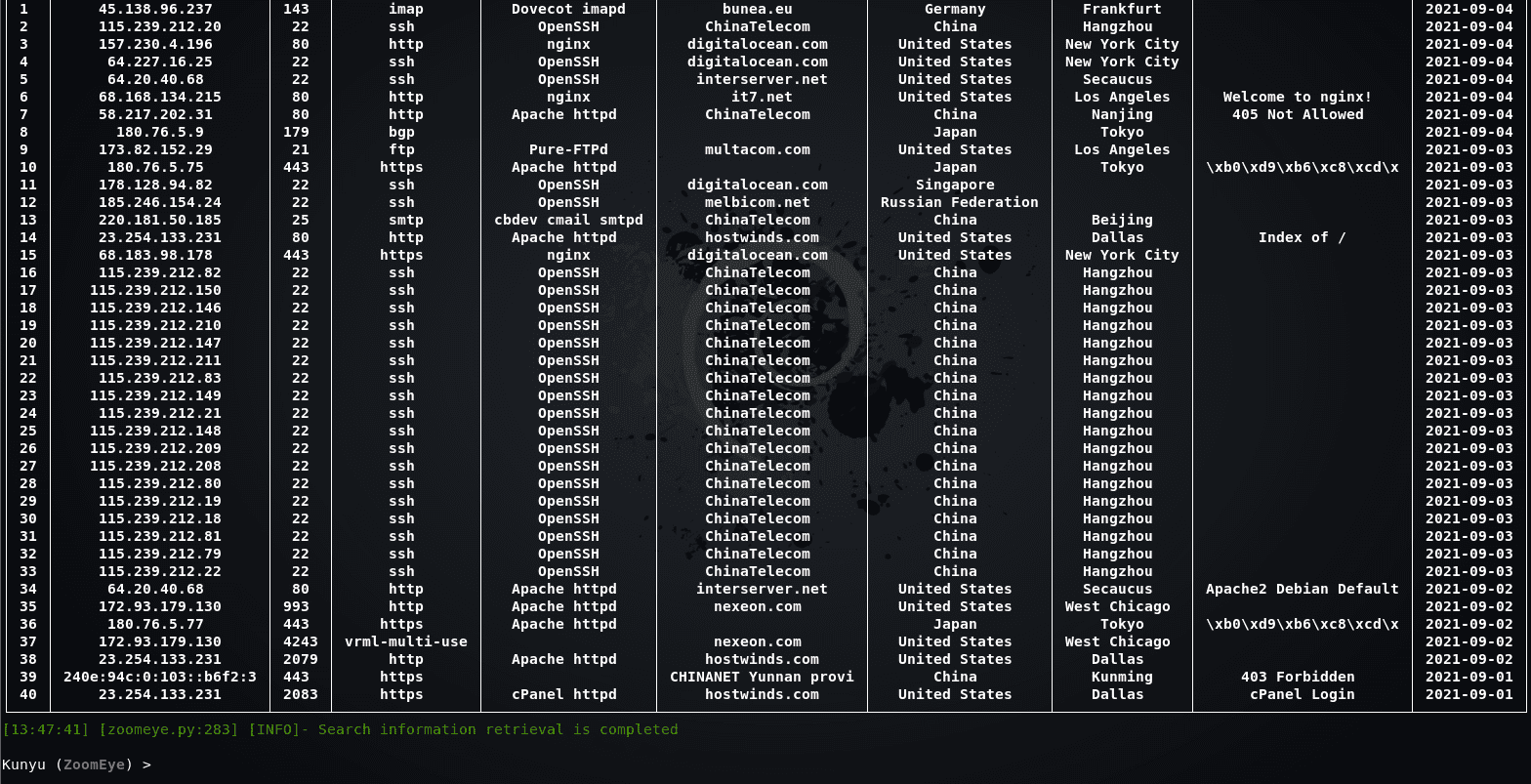
Here we use the ZoomEye module for demonstration
User information query

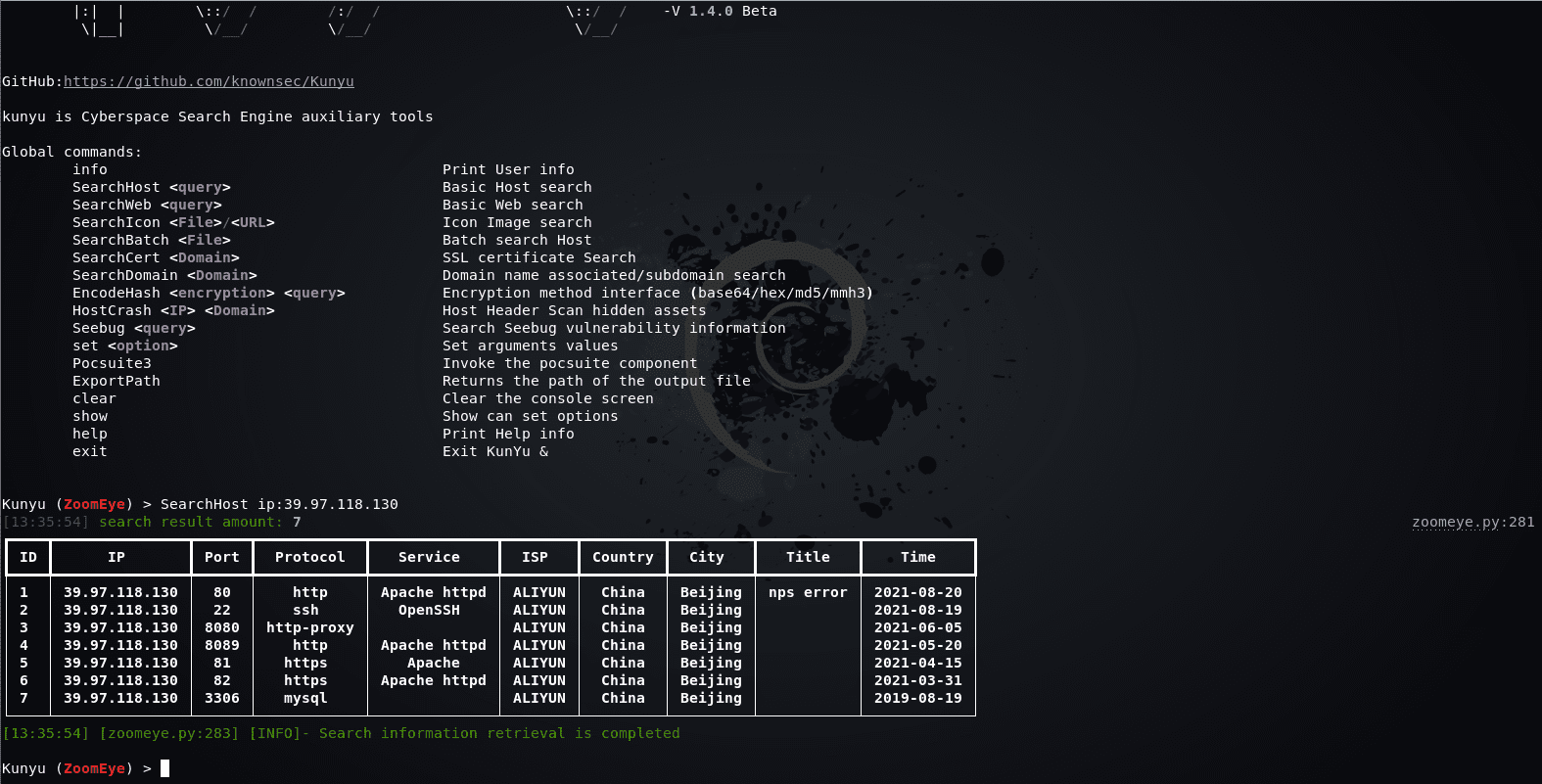
HOST host search
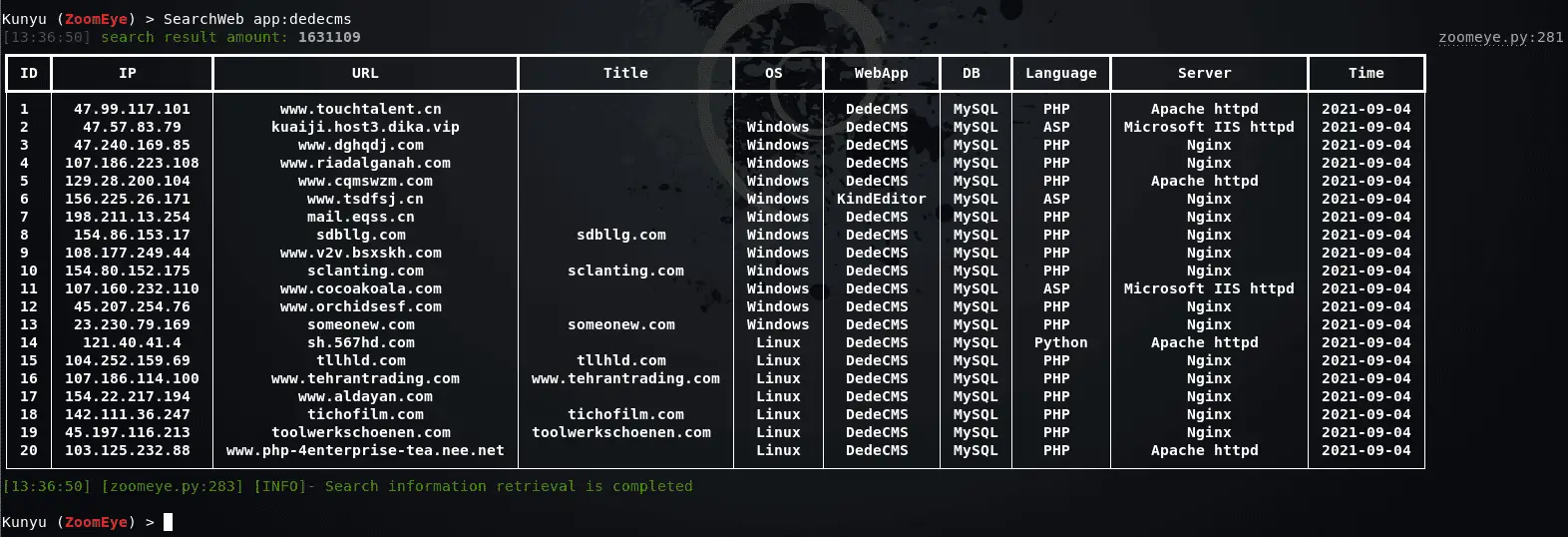
Web host search
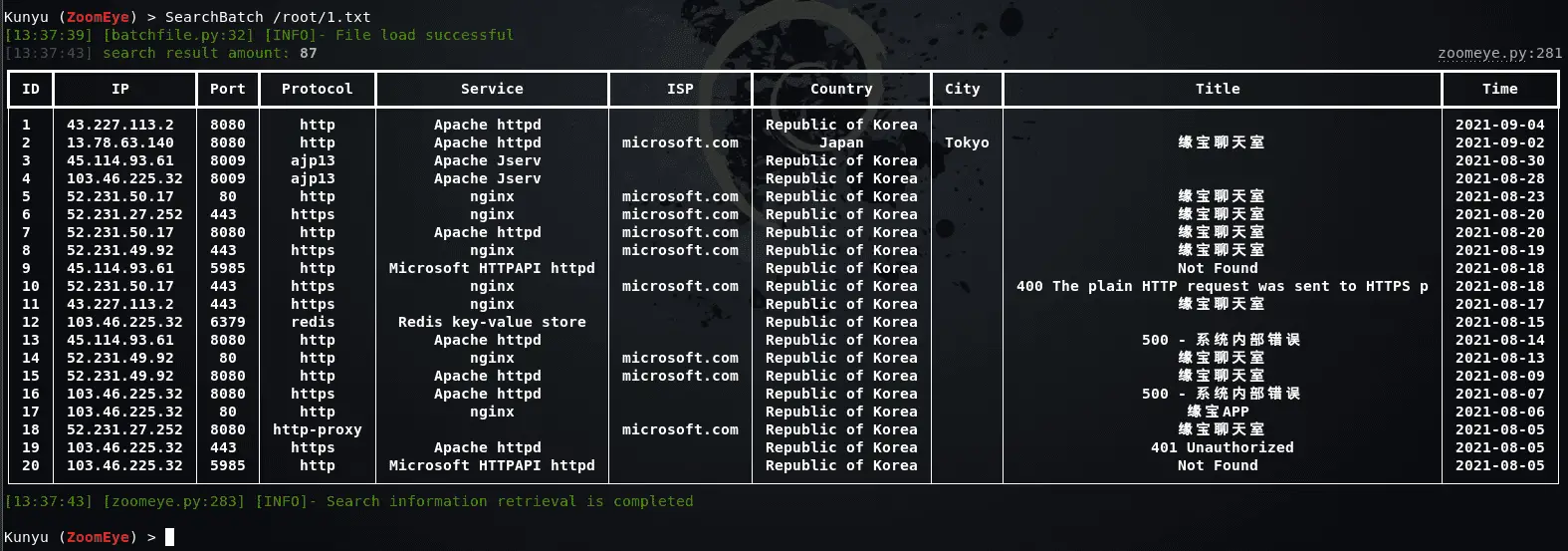
Batch IP search
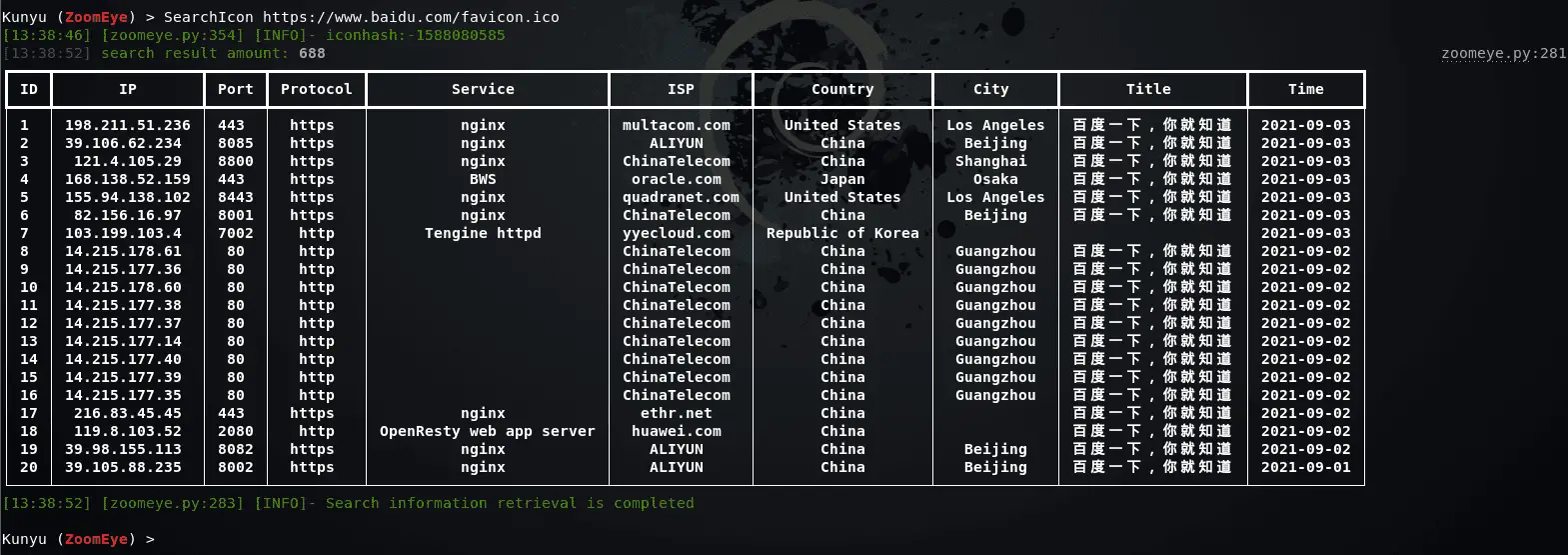
Icon Search
When collecting corporate assets, we can use this method to retrieve the same ico icon assets, which usually has a good effect when associating related corporate assets. But it should be noted that if some sites also use this ico icon, irrelevant assets may be associated (but people who are bored with other people’s ico icons are always in the minority). Support url or local file search.
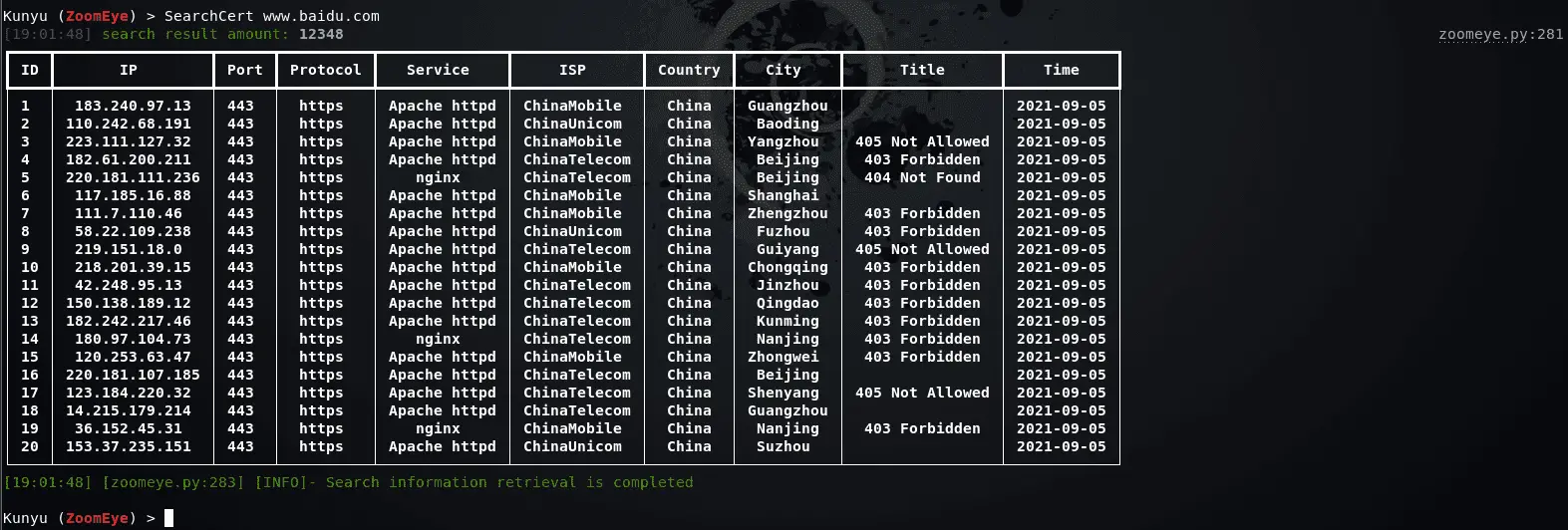
SSL certificate search
Query through the serial number of the SSL certificate, so that the associated assets are more accurate, and services that use the same certificate can be searched. When you encounter an https site, you can use this method.
Multi-factor query
Similarly, Kunyu also supports multi-factor conditional query-related assets, which can be realized through ZoomEye logic operation syntax.
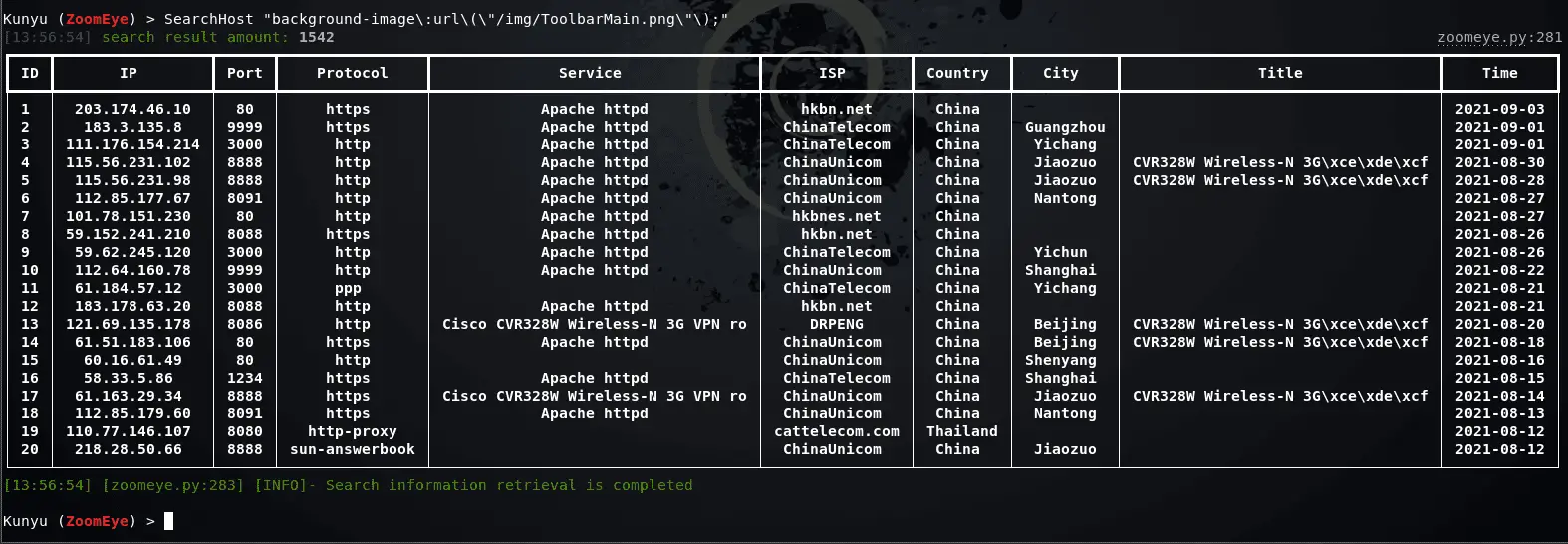
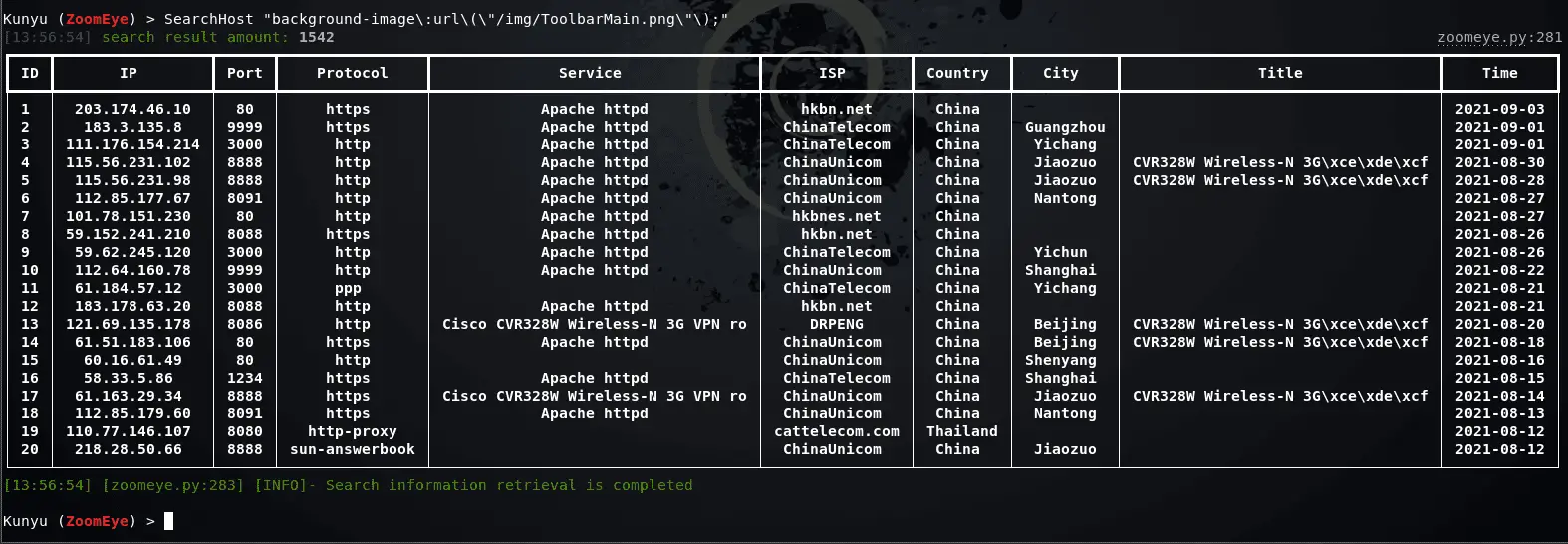
Feature Search
Through HTTP request packet features or website-related features, the same framework assets can be concatenated more accurately

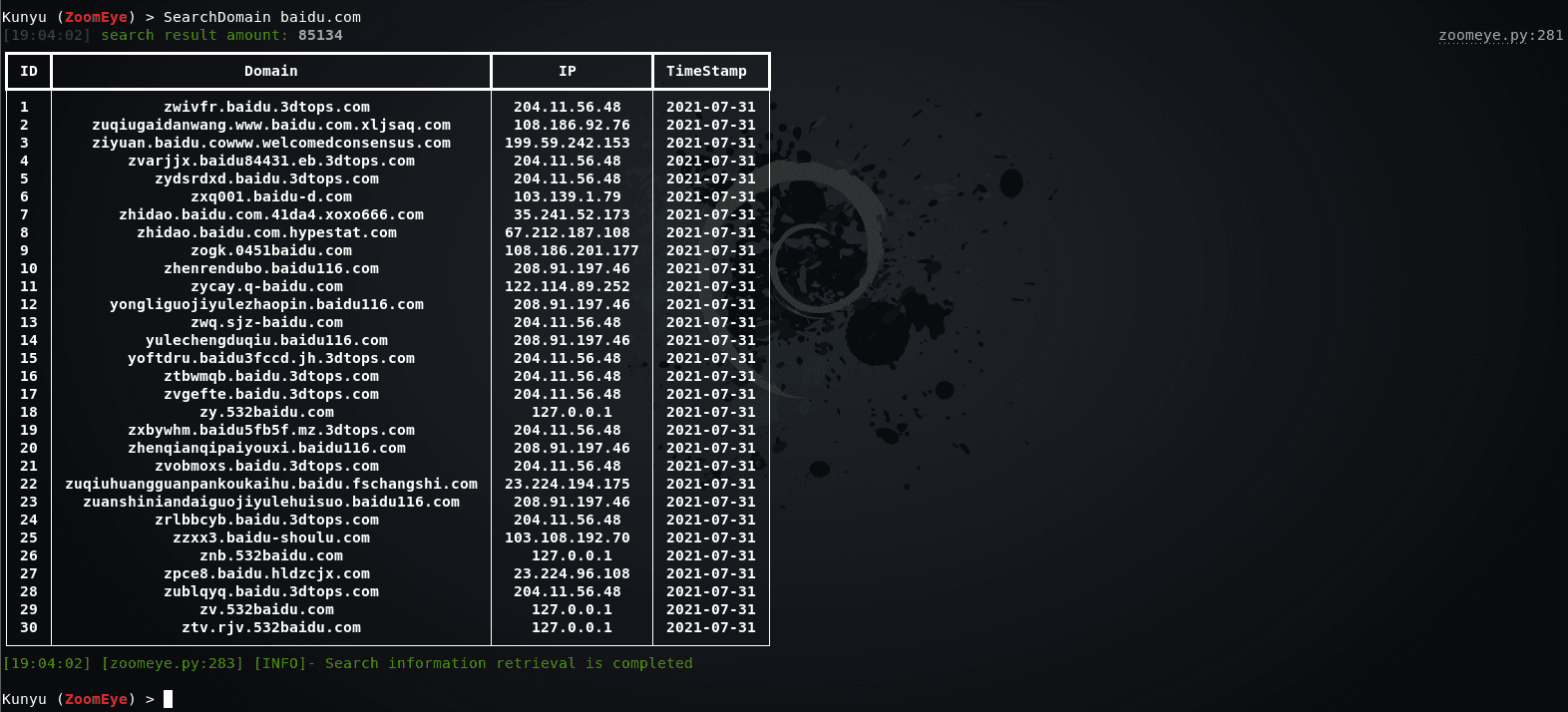
Associated Domain/Subdomain Search
Search for associated domain names and subdomains, and query associated domain names by default. Two modes can be set by setting the dtype parameter.
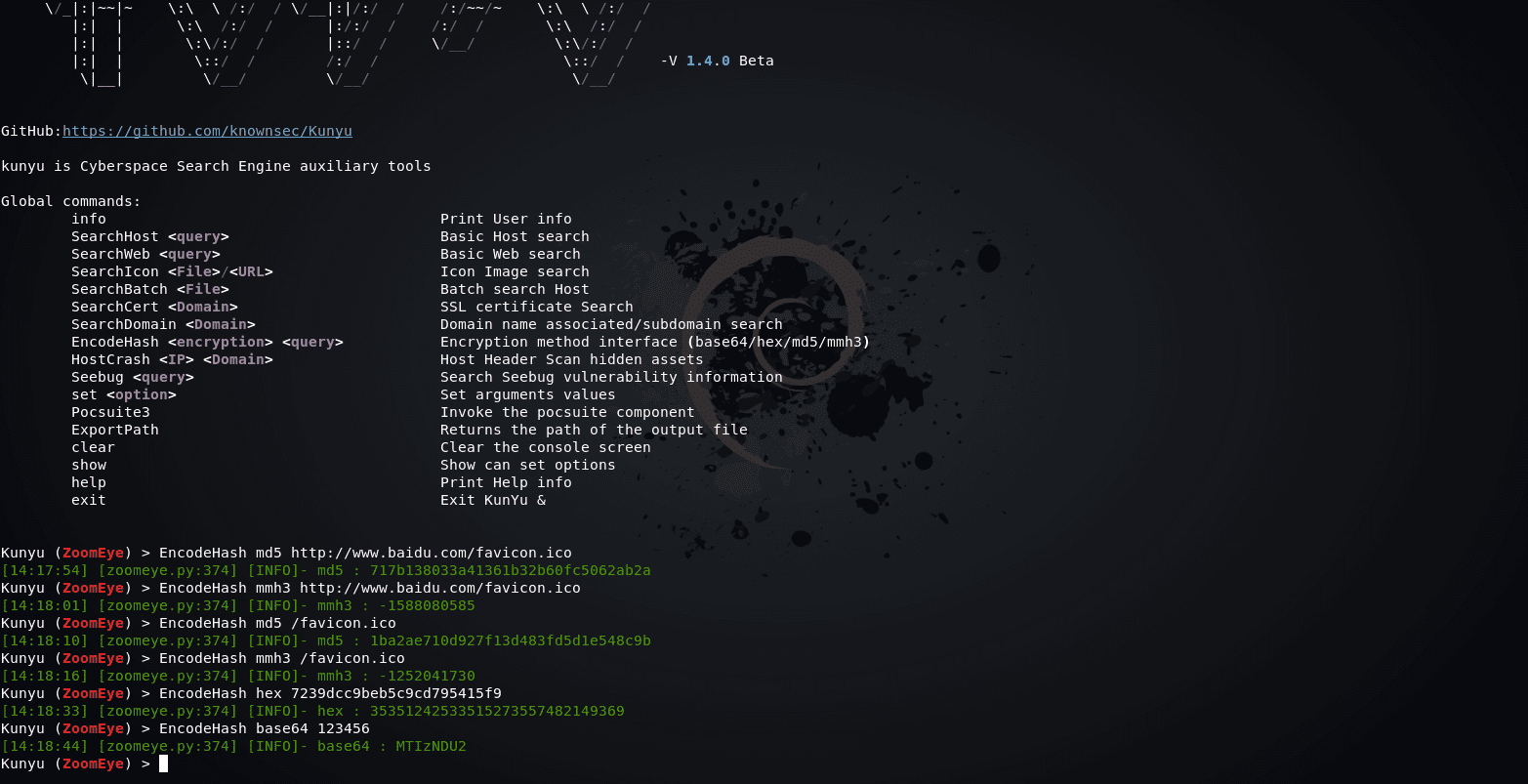
Encoding hash calculation
In some scenarios, you can use this command to perform common HASH encryption/encoding, such as BASE64, MD5, mmh3, HEX encoding, and debug in this way.
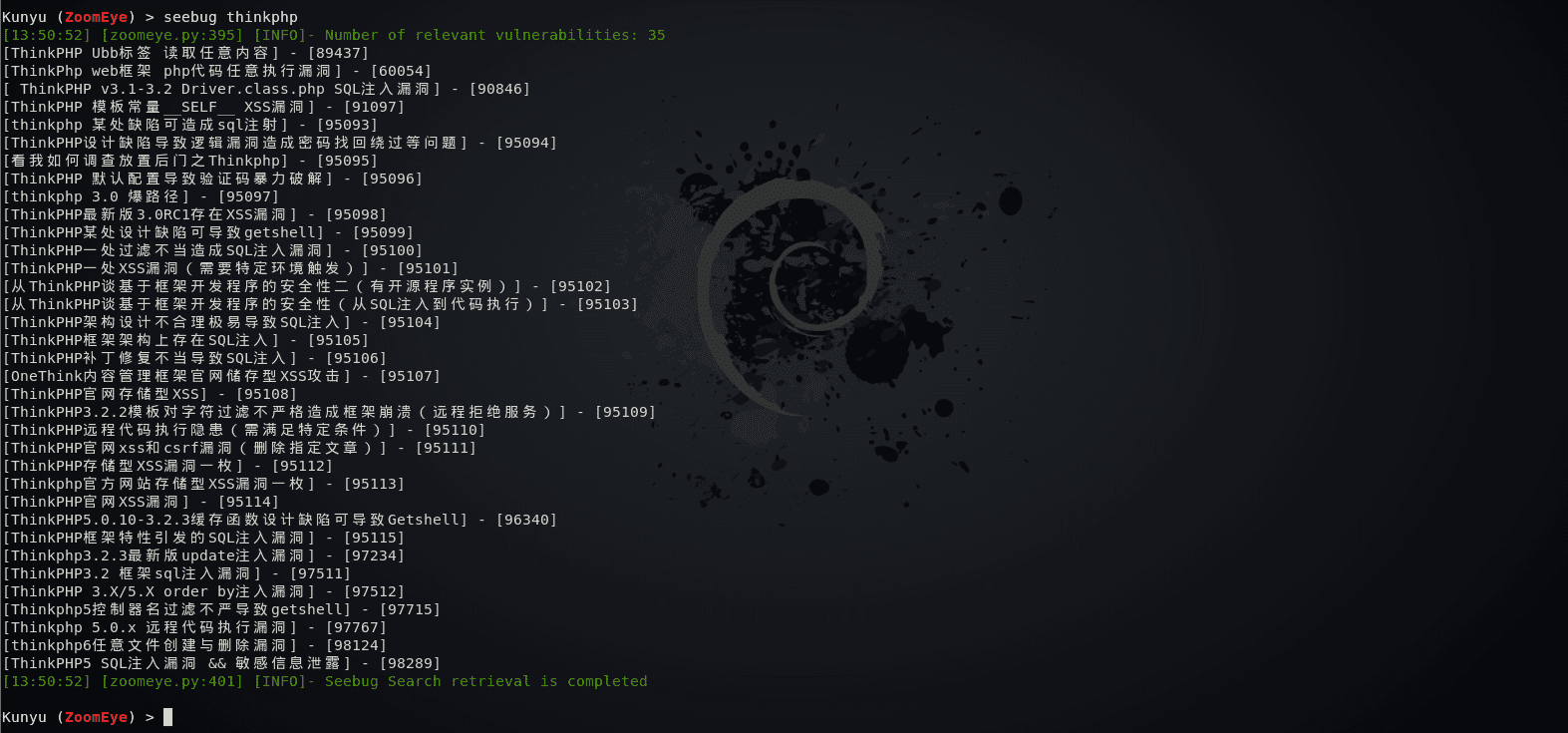
Seebug vulnerability query
You can query historically related vulnerabilities by entering information about the framework and equipment you want to find, but you need to note that only English is supported, and improvements and upgrades will be made later.
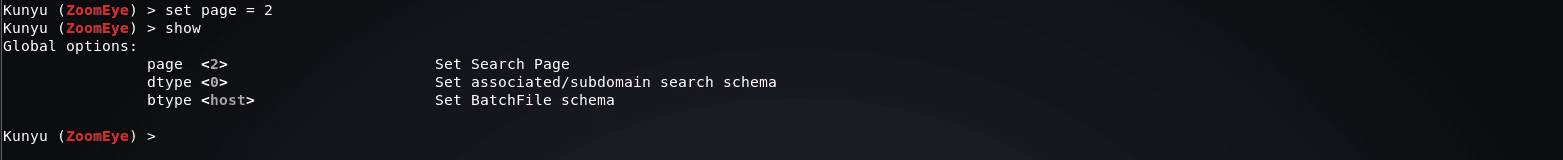
Setting parameters
When set page = 2, the returned results are 40. You can modify the page parameter to set the number of pages to be queried. Note that 1 page = 20/items. You can modify the value according to your needs to get more returned results.
The configurable parameters and the current values of the parameters are displayed through the show.
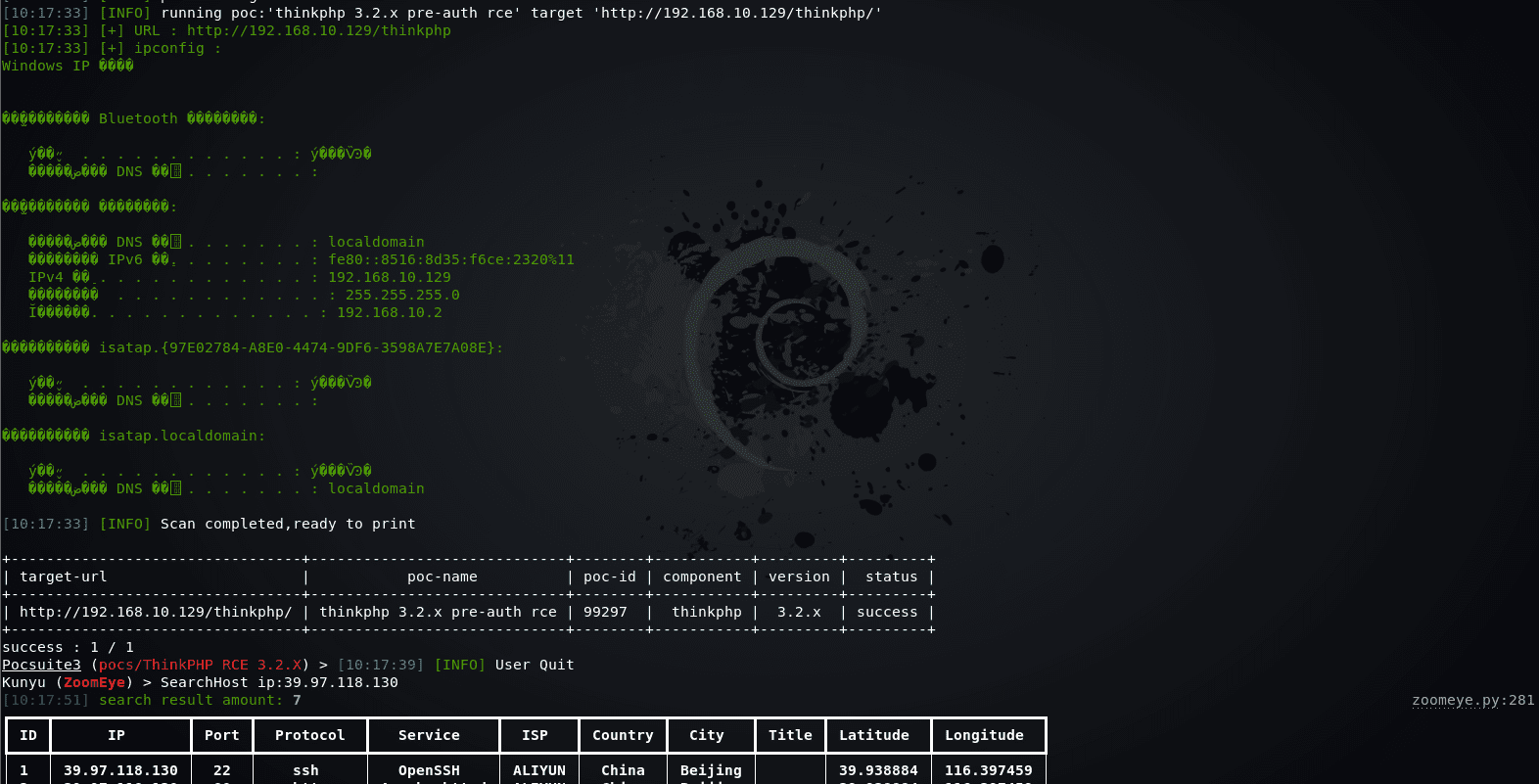
Pocsuite linkage
In versions after v1.3.1, you can use kunyu to link the console mode of pocsuite3 for integrated use.
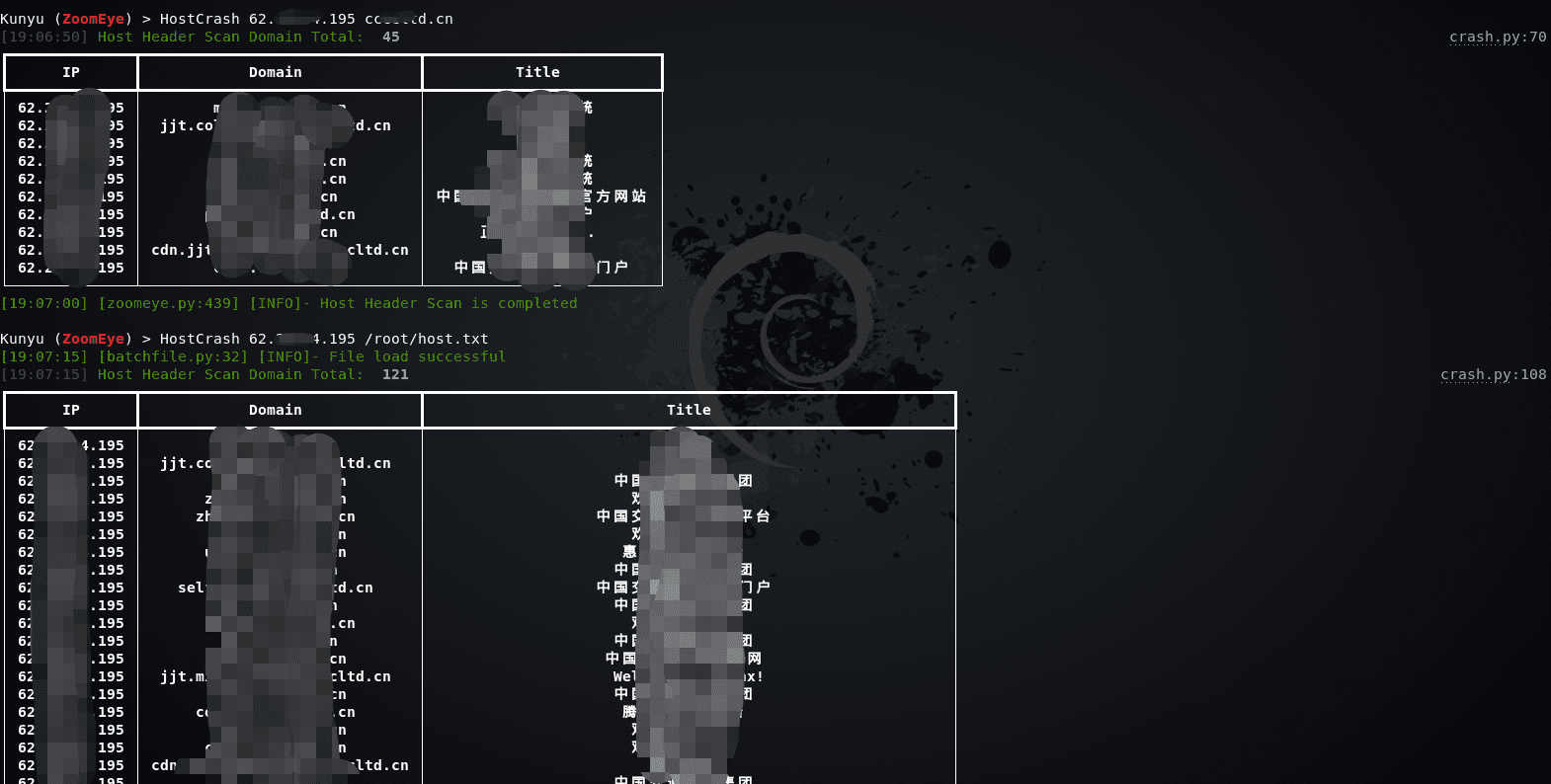
HOSTS head collision
Through the HOSTS collision, the hidden assets in the intranet can be effectively collided, and the intranet service can be accessed according to the ServerName domain name and IP configured in the middleware httpf. conf. This can be achieved by setting the local hosts file later because the local hosts file takes precedence. The level is higher than DNS server resolution. Support reverse checks through ZoomEye domain name library or read TXT file to get the list of domain names.
Data result
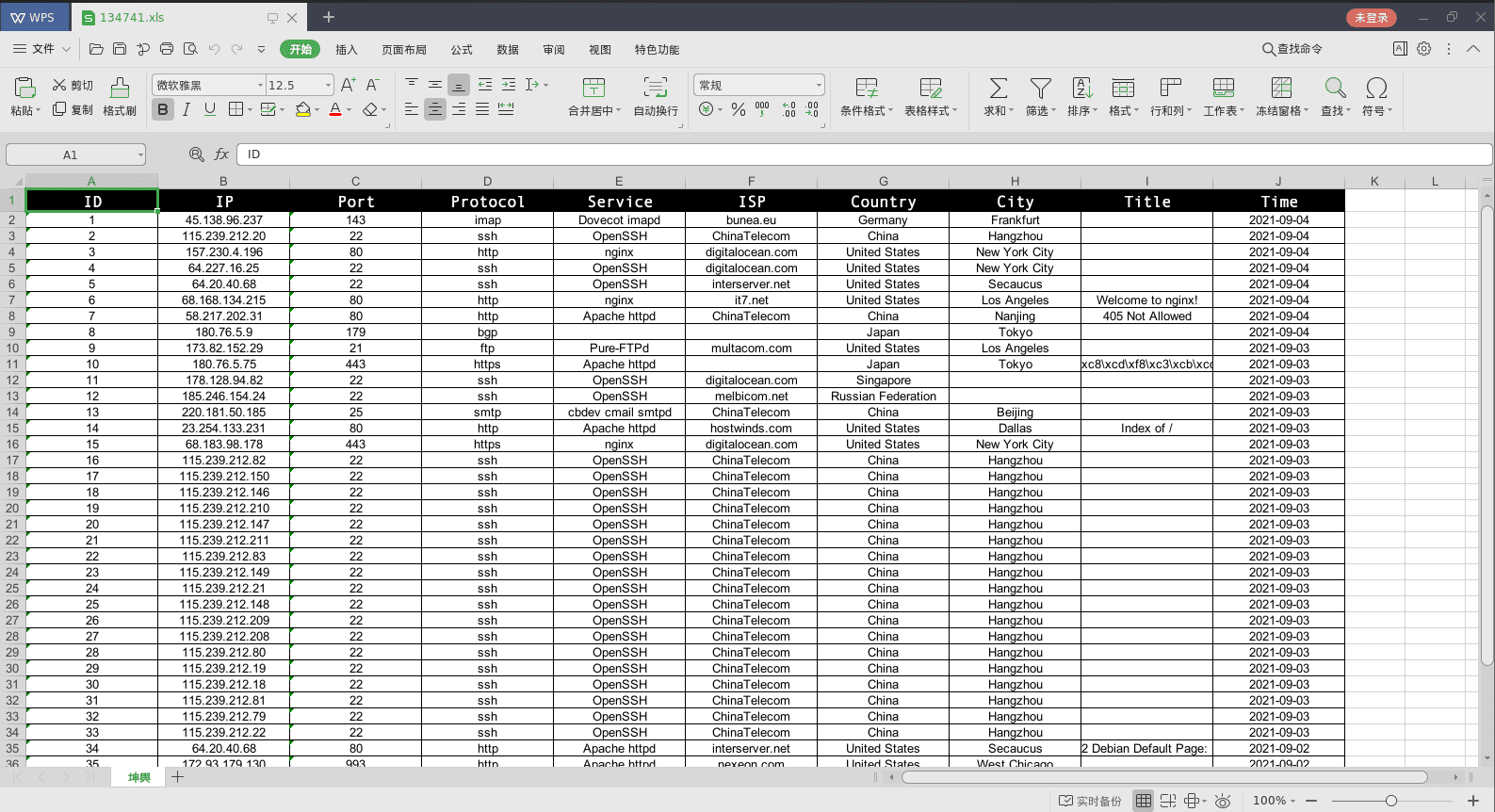
All search results are saved in the user’s root directory, and the directory is created based on the current timestamp. All query results of a single start are stored in an Excel format under one directory, giving a more intuitive experience. The output path can be returned through the ExportPath command.
Changelog v1.7.2
Added
- Added the Cscan command, Scans port information about cobaltStrike
- Fixed LAT/LON missing bug
Install & Use
Copyright (C) 2021 knownsec





