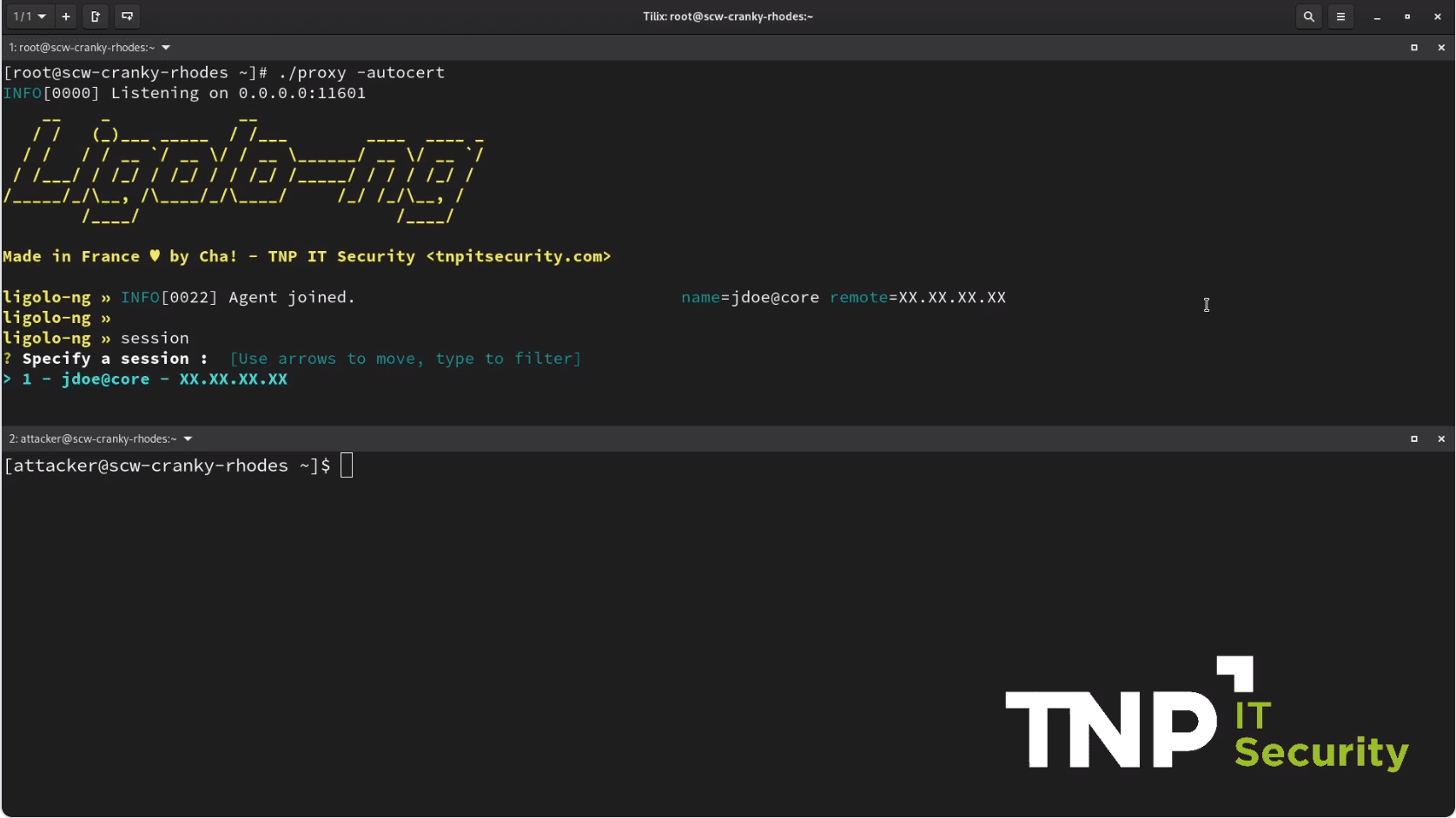
ligolo-ng v0.4.5 releases: advanced tunneling/pivoting tool
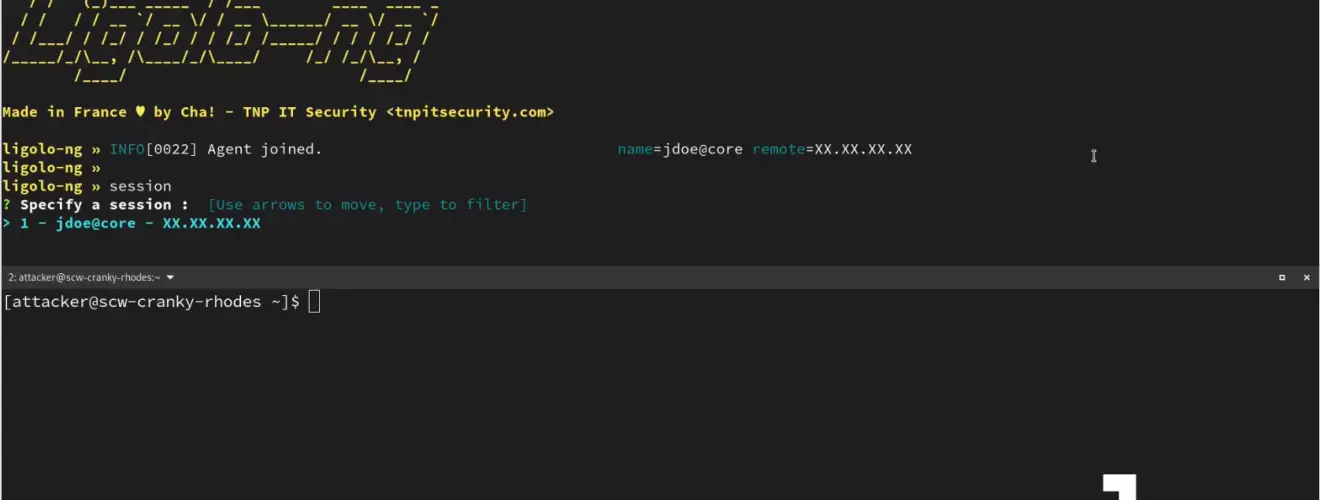
Ligolo-ng : Tunneling like a VPN
An advanced, yet simple, tunneling tool that uses a TUN interface.
Ligolo-ng is a simple, lightweight, and fast tool that allows pentesters to establish tunnels from a reverse TCP/TLS connection without the need of SOCKS.
Features
- Tun interface (No more SOCKS!)
- Simple UI with agent selection and network information
- Easy to use and setup
- Automatic certificate configuration with Let’s Encrypt
- Performant (Multiplexing)
- Does not require high privileges
- Socket listening/binding on the agent
- Multiple platforms supported for the agent
How is this different from Ligolo/Chisel/Meterpreter…?
Instead of using a SOCKS proxy or TCP/UDP forwarders, Ligolo-ng creates a userland network stack using Gvisor.
When running the relay/proxy server, a tun interface is used, packets sent to this interface are translated and then transmitted to the agent remote network.
As an example, for a TCP connection:
- SYN is translated to connect() on remote
- SYN-ACK is sent back if connect() succeed
- RST is sent if ECONNRESET, ECONNABORTED, or ECONNREFUSED syscall are returned after connect
- Nothing is sent if a timeout
This allows running tools like nmap without the use of proxychains (simpler and faster).
Changelog v0.4.5
- c9e1ffc ci update
- 80c6fec dependency update
- d0ae589 fix #49, implement udp listeners
- 1308edd Update README.md
- 8342046 Update README.md
- dcc5d27 Create FUNDING.yml
Install & Use
Copyright (C) 2021 tnpitsecurity