melting-cobalt: Cobalt Strike Scanner
melting-cobalt
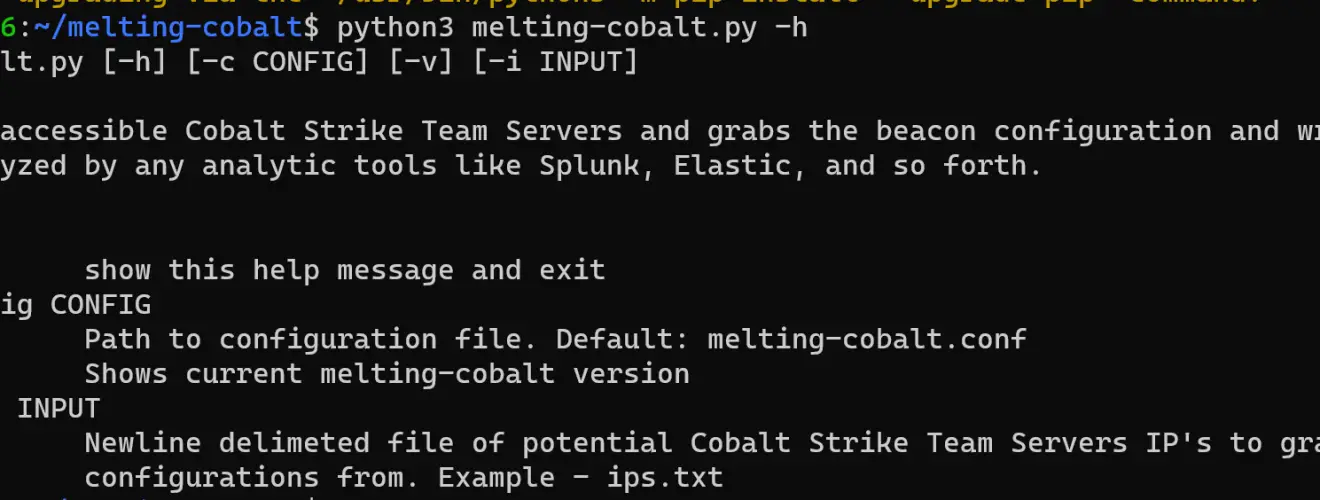
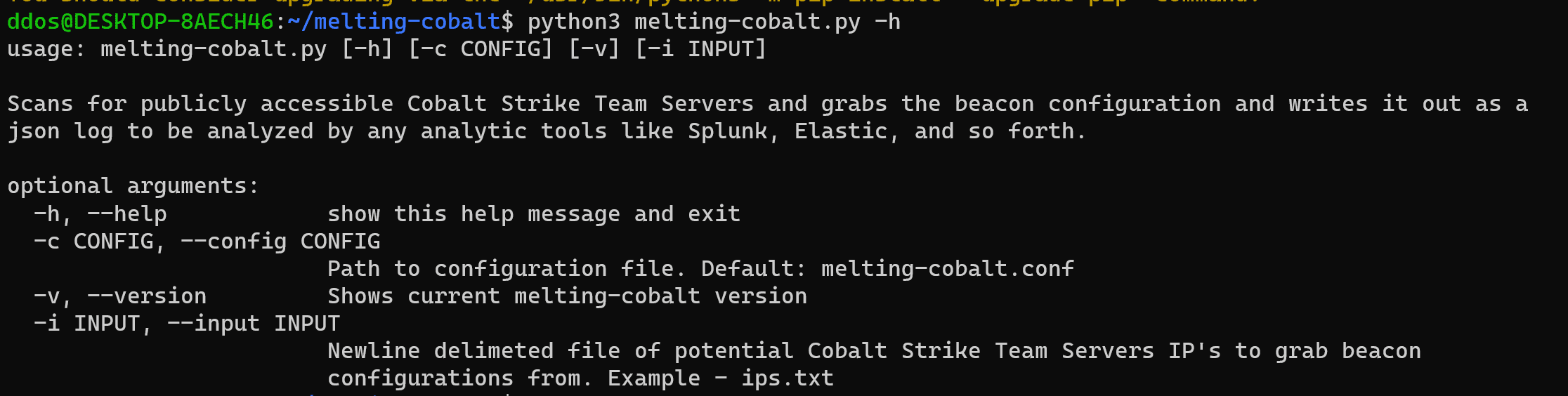
A tool to hunt/mine for Cobalt Strike beacons and “reduce” their beacon configuration for later indexing. Hunts can either be expansive and internet-wide using services like SecurityTrails, Shodan, or ZoomEye or a list of IPs.
Installation
Requirements: virtualenv, and python3.8+
- git clone https://github.com/splunk/melting-cobalt && cd melting-cobalt Clone project and cd into the project dir.
- pip install virtualenv && virtualenv -p python3 venv && source venv/bin/activate && pip install -r requirements.txt Create Virtualenv and install requirements.
Continue to configure for SecurityTrails, Shodan, or ZoomEye API key.
Configuration melting-cobalt.conf
Copy melting-cobalt.conf.example to melting-cobalt.conf!
Make sure to set a token for one of the available providers. If you need to create one for your account follow [these](htt://need wiki page) instructions.
Configuration example:
Search The Internet
To modify the default mining performed across different providers, customize search.yml. The default melting-cobalt Search Examples are below.
Run:
python melting-cobalt.py
Search IP list
populate ips.txt with potential Cobalt Strike C2 IPs a new line delimited, example:
1.1.1.1 2.2.2.2 3.3.3.3
Run:
python melting-cobalt.py -i ips.txt
Use
Search Examples
The following searches are provided out of the box and more may be added to search.yml for more data.
Shodan
Find specific JARM signatures, out of the box we track Cobalt Strike 4.x
Filter by HTTP headers and ports to reduce noisy results
Team server detected by Shodan
‘product:”cobalt strike team server”‘
note: will generate lots of noisy results, do not actually schedule this unless you want to burn your license credits.
Team server certificate serial
‘ssl.cert.serial:146473198’
SecurityTrails
Find specific JARM signatures
Filter by HTTP Headers and ports to reduce noisy nmap_results
Copyright 2020 Splunk Inc.
Source: https://github.com/splunk/






