Mondoo v10.0 releases: Cloud-Native Security & Vulnerability Risk Management
Mondoo
Mondoo is a natural language query system for scanning, deploying, and remediating your cloud-native applications.
Feature
Insights into your fleet
Ask questions about your deployments and get answers. Simple questions are answered using AI for recognition and a fast search. Developers use queries based on GraphQL with added JS extensions. Stop searching across multiple tools, parsing and aggregating information.
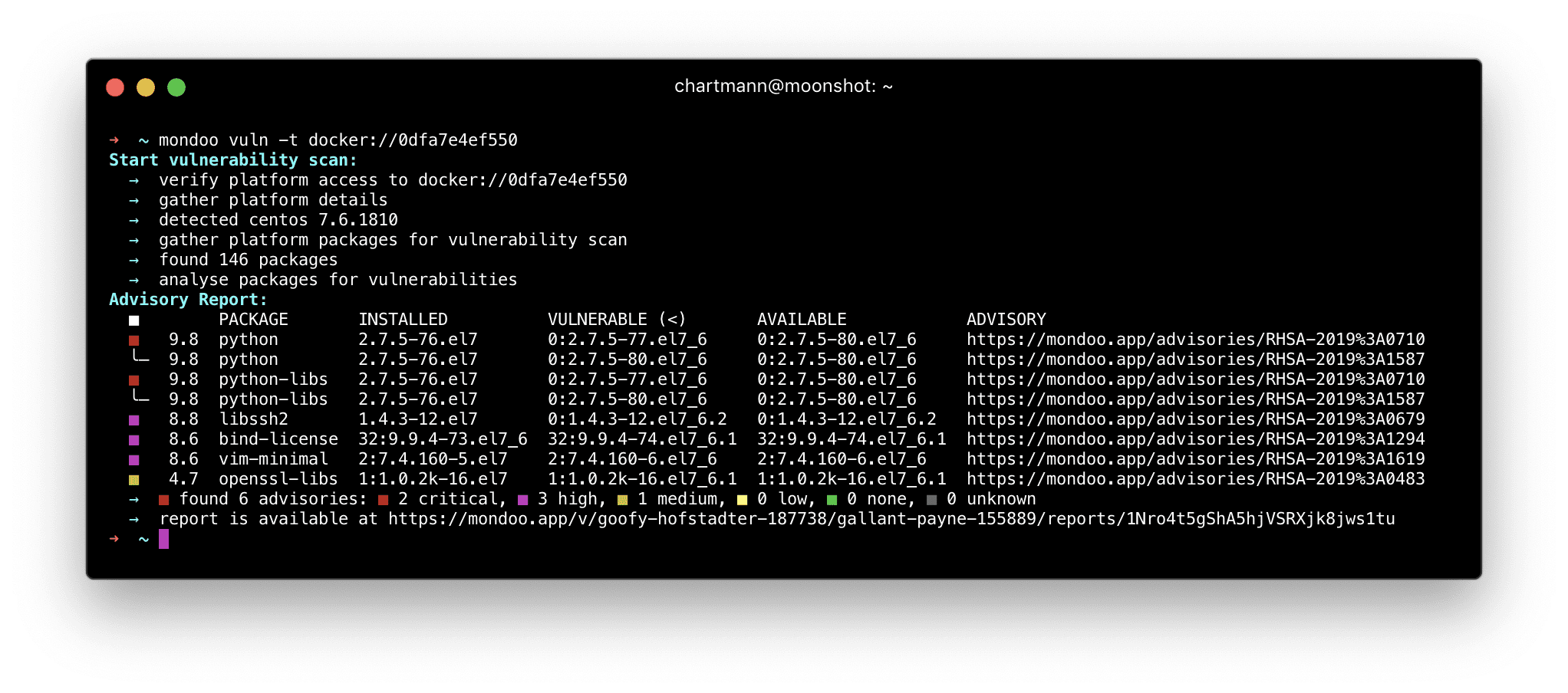
Find Vulnerabilities
Mondoo helps find vulnerabilities across all deployments. It works with cloud workloads, containers, kubernetes, VMs, and bare-metal servers. Quickly assess and monitor your assets continuously. Use it as a developer, in your CI/CD, or in your production fleet.
Scorecards
Gain quick understanding into your deployments with our scoring system. Mondoo provides reports for security, and operational efficiency. This helps to prioritize and tackle the problems that have the largest impact. Score are incredibly effective in communicating what needs work and where you shine.
Cloud native and flexible
Mondoo easily integrates with all major cloud providers (AWS, Azure, GCP) and the leading container runtime, Kubernetes. It also supports on-prem deployments. This mix makes it especially well suited for hybrid or multi-cloud use-cases.
Live and uncut
Once set up, Mondoo will watch for changes and update your queries. No need to refresh. Provide IDS functionality with assertions across your fleet. Integrate custom actions and cloud functions whenever a query changes you care about.
The Mondoo agent is a small & cross-platform binary that makes it easy to assess system vulnerabilities. Its main responsibility is to determine installed packages and send the package list including their versions for further analysis to Mondoo’s vulnerability database.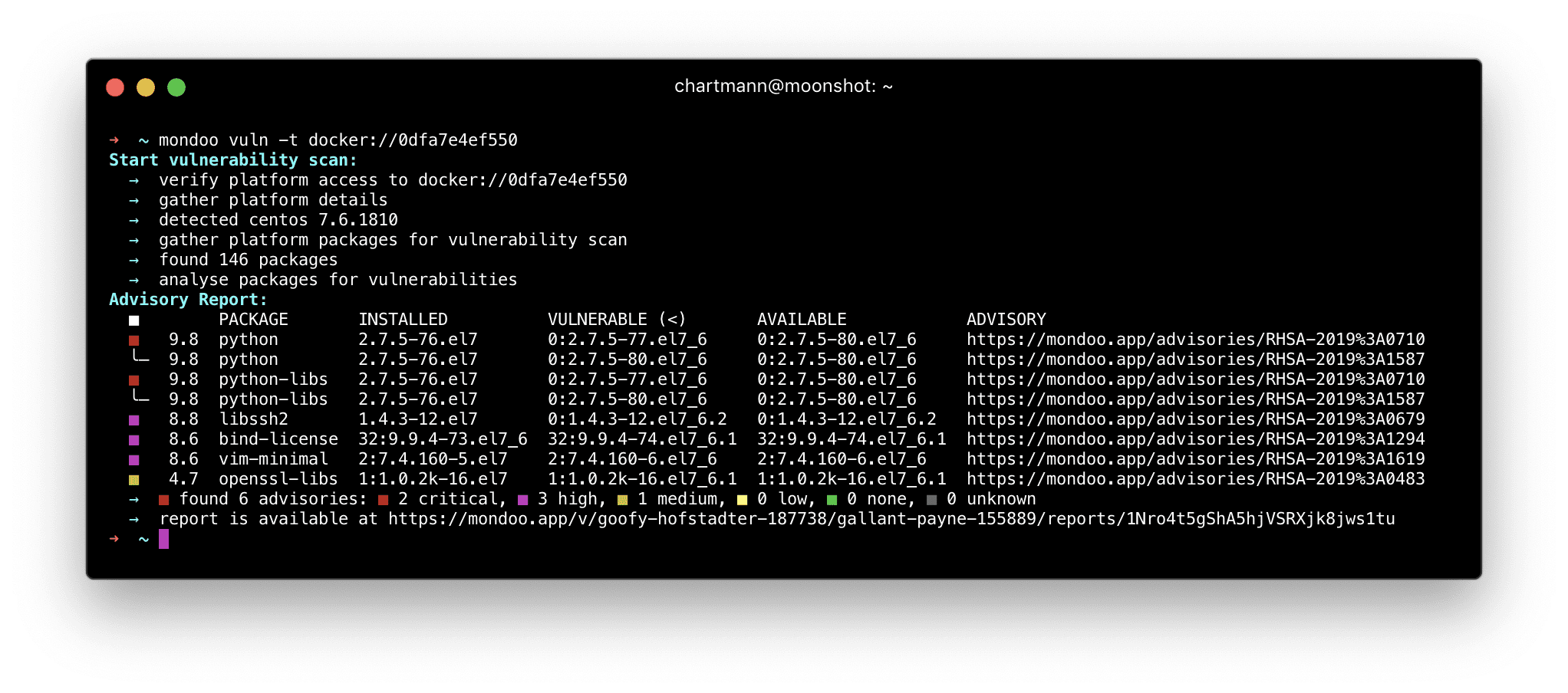
How it works
The agent works by continuously assessing the installed packages and submitting the package metadata to Mondoo API over HTTPS. After the registration with your Mondoo Space, the agent is ready for vulnerability assessments.
The CLI is designed for two use cases:
- run as service for continuous vulnerability assessment
- run on a workstation to assess vulnerabilities for remote systems or docker images
- run docker image scan as part of a CI/CD
Use case: Service
You want to see the vulnerability assessment of your server continuously. The agent runs in the background and submits changes of the installed packages for vulnerability analysis. By using this approach, you always have the latest view of your infrastructure.
The agent can scan the following assets:
- Local Operating System
- Remote Operating System via SSH
- Docker images (local or remote)
- Docker containers (running or stopped)
Install && Use
© Copyright 2019 Mondoo.





