NimPackt-v1: Nim-based packer for .NET executables and raw shellcode
NimPackt-v1 – A Nim-based packer for .NET executables and raw shellcode
NimPackt is a Nim-based packer for .NET (C#) executables and shellcode targeting Windows. It automatically wraps the payload in a Nim binary that is compiled to Native C and as such harder to detect and reverse engineer. There are two main execution methods:
- Execute-Assembly re-packs a .NET executable and runs it, optionally applying evasive measures such as API unhooking, AMSI patching, or disabling ETW.
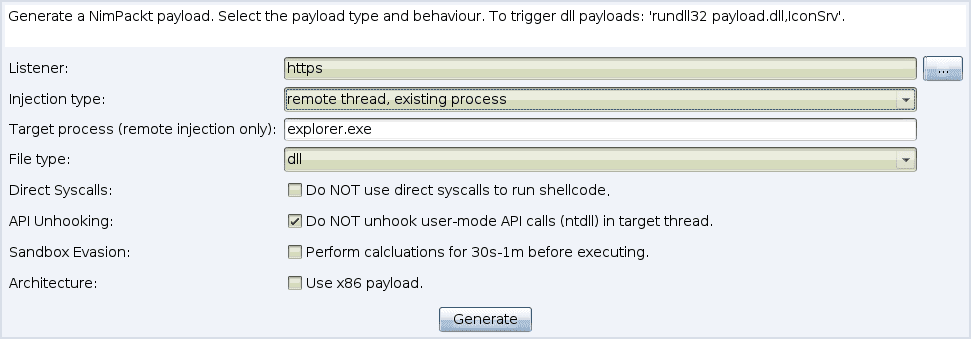
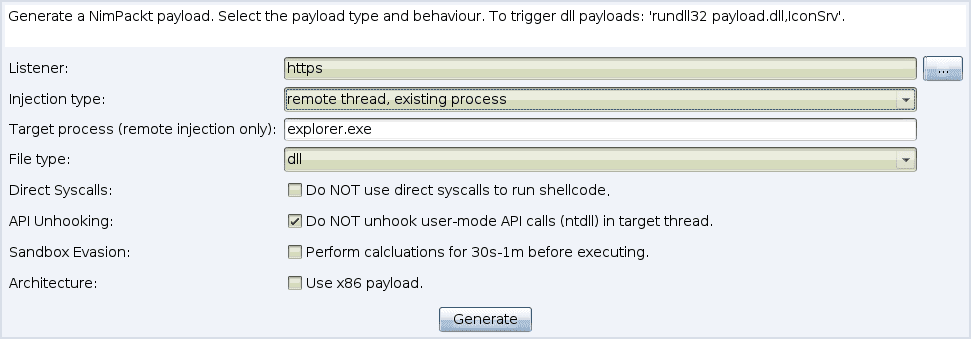
- Shinject takes raw a .bin file with raw, position-independent shellcode and executes it locally or in a remote process, optionally using direct syscalls to trigger the shellcode or patching API hooks to evade EDR.
Currently, NimPackt has the following features.
- Uses static syscalls to patch execute to evade EDR
- Unhooks user-mode APIs for the spawned thread by refreshing NTDLL.dll using ShellyCoat
- Patches Event Tracing for Windows (ETW)
- Patches the Anti-Malware Scan Interface (AMSI)
- AES-encrypts payload with a random key to preventing static analysis or fingerprinting
- Compiles to exe or dll
- Supports cross-platform compilation (from both Linux and Windows)
- Integrates with CobaltStrike for ezpz payload generation 😎
A great source for C#-based binaries for offensive tooling can be found here. It is highly recommended to compile the C# binaries yourself. Even though embedded binaries are encrypted, you should obfuscate sensitive binaries (such as Mimikatz) to lower the risk of detection.
Install & Use
Copyright (c) 2022 Cas van Cooten (@chvancooten)






