Ninja v2.2 releases: Open source C2 server created for stealth red team operations
What is Ninja?
Ninja C2 is an Open source C2 server created by Purple Team to do stealthy computer and Active directory enumeration without being detected by SIEM and AVs, Ninja still in beta version, and when the stable version released it will contain many more stealthy techniques and anti-forensic to create a real challenge for the blue team to make sure all the defenses configured correctly and they can detect sophisticated attacks.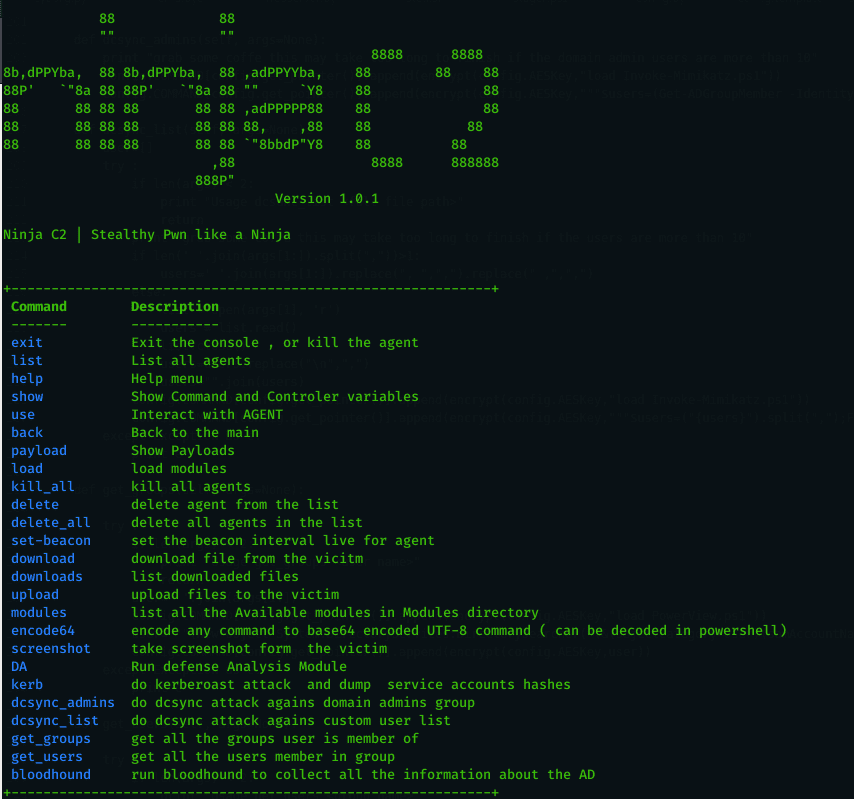
Ninja uses python to the server the payload and controls the agents. the agents are based on C# and powershell which can bypass leading AVs. Ninja communicate with the agents in secure channel encrypted with AES-256 and the key is not hardcoded but randomly generated on the campaign start, every agent connects to the C2 get the key and if the C2 restarted a new key will be used by all old agents and the new. Ninja also randomizes the callback URLs for every campaign to bypass static detection.
- The main feature in Ninja is called DA ( Defense Analysis ), which will do the required enumeration to get below important information and do analysis on them to get the score for system defenses and sandbox detection.
- Detect SIEM solutions: right now it detects Splunk, Log beat collector, sysmon.
- detect AV using two ways, using powershell command and using processes.
- check if the powershell logging enabled
- check if the user has admin privileges
- provide information about the system : hostname, OS, build number, local time, time zone, last boot, and bios.
- provide information about the installed security updates.
- provide a System pwn hardness score based on multiple factors.
- provide a sandbox detection score based on ( privileges, bios manufacturer, joined to a domain or not, the existence of Sysinternals processes ).
- show all domain users ( using powershell commands ).
- show all domain groups ( using powershell commands ) .
- show all domain computers ( using powerview.ps1 – taken from : https://github.com/PowerShellEmpire/PowerTools/blob/master/PowerView/powerview.ps1 ).
- show available shares.
Ninja is designed to be easy to set up and to add more commands and do automation for boring tasks. you can find many short commands that a red teamer struggle to memorize and search for them. please check this article to know more about ninja.
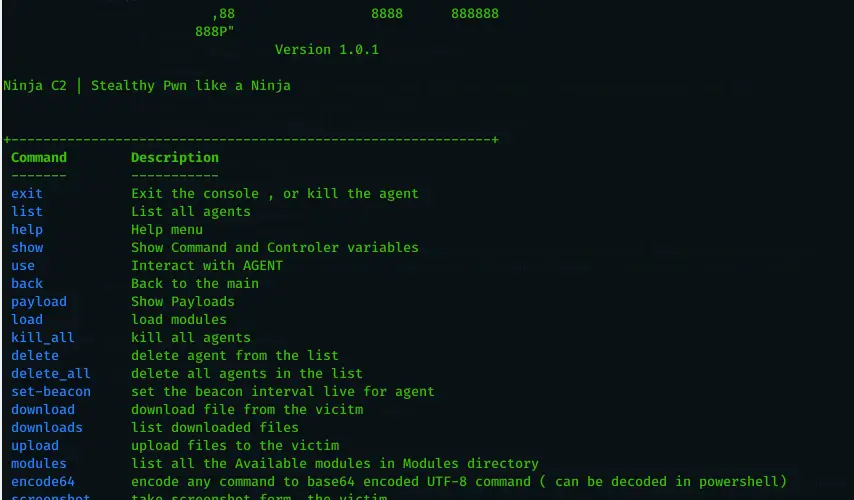
Ninja key features
Ninja is packed with a number of features that allows you to gain an insight into your upcoming engagement before you actually need to deploy your full arsenal of tools and techniques, such as:
- Defense Analysis
- automation for kerberoast attack from generating the Kerberos tickets to extracting the SPN hashes into hashcat format.
- automation for dc_sync to get hashes for a list of users or domain admin group.
- Undetected Automation to get groups the user belongs to and the users’ members in a group.
- Automation for bloodhound AD data collection.
- customized c# payloads that encrypt strings to bypass static detection.
- encode any command you want to Unicode base64 to be used in powershell encoded commands.
- full encryption of all communications between Agent and command and control to bypass AV and IPS detection.
- dynamic URLs for all functions, just place your list of url names and the c2 will use it randomly to bypass any static detection.
- get random encryption key on the fly ( not hardcoded ) every time the agent connect ( even reconnection needs a new key )
- take screenshots and send it encrypted to C2
- upload files from C2 to victim encrypted to bypass AV and IPS
- download files from the victim encrypted to bypass AV and IPS
- staged payloads to bypass detection ( base64 and base52 )
- bypasses AVs ( tested on Kaspersky and trendmicro )
- Bypasses SIEM detection ( tested on Splunk collecting usual event logs along with sysmon logs ) not tested on powershell v5 script block and module logging ( will be done in the next release ).
- set the beacon interval dynamically even after the agent connected and provide a starting beacon interval in the campaign start configurations
- logging for all commands and results in order to return to any data you missed in your operation.
- set the configuration one time when you start the campaign and enjoy it.
- global kill switches to end campaigns.
- delete table entries.
- all the payload is written to payloads folder for easy access and further customization.
- easy to add automation for any command you want.

Changelog v2.2
- new user interface for CnC script
- Now each campaign will include all the files related to the campaign and the configuration file.
- new script automate AWS instance creation with NinjaC2 configuration.
- Updated Invoke-Mimikatz powershell script to latest Mimikatz release.
- Bug Fixes
Install & Use
Copyright (C) 2020 Purple Team






