NixImports: .NET malware loader, using API-Hashing and dynamic invoking to evade static analysis
NixImports
A .NET malware loader, using API-Hashing and dynamic invoking to evade static analysis.
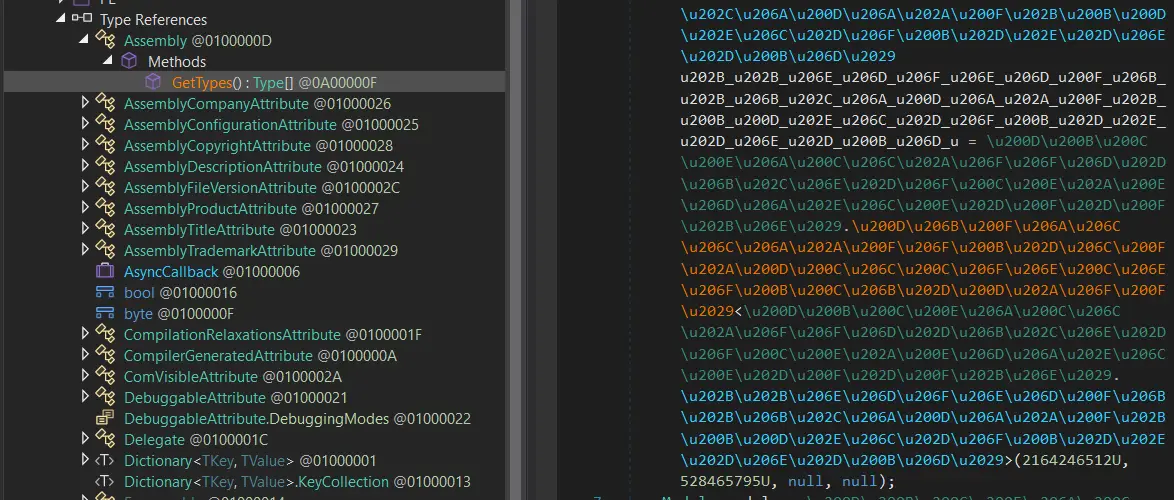
NixImports aims to build a loader with little to no direct function calls and reduce referenced methods to a minimum. Importing a function in .NET adds some metadata, for example, the namespace and name of the referenced method. This metadata gives away potential capabilities of our binary and can be used for detection, see, for example, GDATA’s TypeRefHash. To avoid this kind of metadata as much as possible, NixImports uses my managed API hashing implementation HInvoke. HInvoke does not require the method we want to invoke to be referenced in the assembly; instead, it will dynamically resolve the method or property on runtime, using only two hash values to identify the target method.

How does it work?
NixImports uses my managed API-Hashing implementation HInvoke, to dynamically resolve most of it’s called functions at runtime. To resolve the functions HInvoke requires two hashes the typeHash and the methodHash. These hashes represent the type name and the method FullName, on runtime HInvoke parses the entire mscorlib to find the matching type and method. Due to this process, HInvoke does not leave any import references to the methods called through it.
Another interesting feature of NixImports is that it avoids calling known methods as much as possible, whenever applicable NixImports uses internal methods instead of their wrappers. By using internal methods only we can evade basic hooks and monitoring employed by some security tools.
Download & Use
Copyright (c) 2023 dr4k0nia





