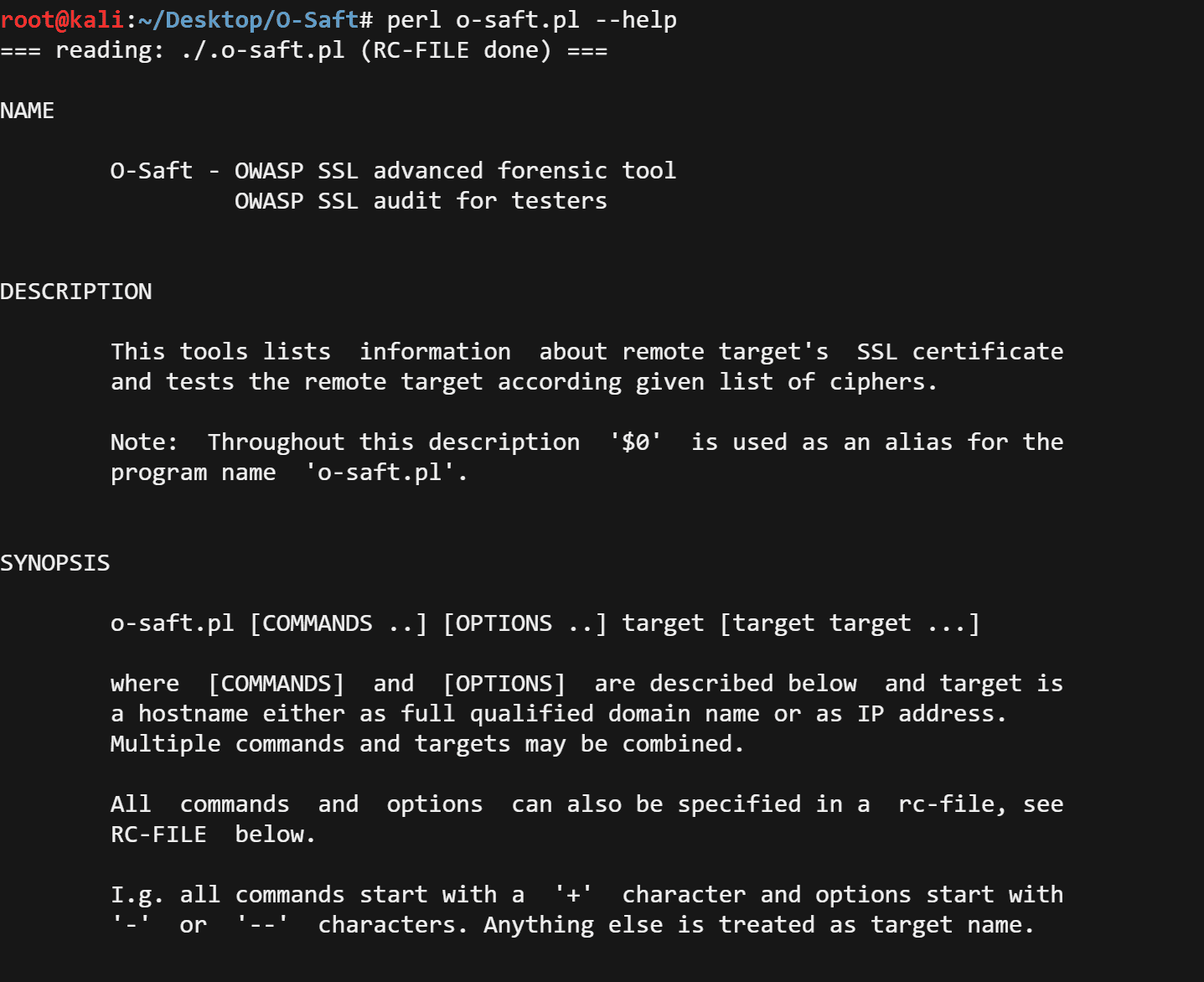
O-Saft v24.01.24 releases – OWASP SSL advanced forensic tool
- OWASP SSL advanced forensic tool / OWASP SSL audit for testers
O-Saft is easy to use tool to show information about SSL certificate and tests the SSL connection according to given list of ciphers and various SSL configurations.
It’s designed to be used by penetration testers, security auditors or server administrators. The idea is to show the important information or the special checks with a simple call of the tool. However, it provides a wide range of options so that it can be used for comprehensive and special checks by experienced people.
O-Saft is a command-line tool, so it can be used offline and in closed environments. There is also a GUI based on Tcl/Tk. However, it can simply be turned into an online CGI-tool.
In a Nutshell
- show SSL connection details
- show certificate details
- check for supported ciphers
- check for ciphers provided in your own libssl.so and libcrypt.so
- check for ciphers without any dependency to a library (+cipherall)
- checks the server’s priority for ciphers (+cipherall)
- check for special HTTP(S) support (like SNI, HSTS, certificate pinning)
- check for protections against attacks (BEAST, CRIME, DROWN, FREAK, Heartbleed, Lucky 13, POODLE, RC4 Bias, Sweet32 …)
- check the length of Diffie Hellman Parameters by the cipher (+cipherall needs option ‘–experimental’)
- may check for a single attribute
- may check multiple targets at once
- can be scripted (headless or as CGI)
- should work on any platform (just needs Perl, OpenSSL optional)
- can be used in CI / CD environments
- the output format can be customized
- various trace and debug options to hunt unusual connection problems
- supports STARTTLS for various protocols like (SMTP, POP3, IMAP, LDAP, RDP, XMPP, IRC (experimental) …),[without options using openssl]
slows down to prevent blockades of requests due to too many connections (supported by some protocols like SMTP) - Proxy is supported (besides commands using OpenSSL)
- a check of STARTTLS/SMTP for all servers of an MX Resource Record (e.g. checkAllCiphers –mx your.tld:25 –starttls=smtp)
- checkAllCiphers.pl and ‘+cipherall’ support DTLS for ‘–experimental’ use (if records are *not* fragmented)
UNIQUE FEATURES
( ===============
) ### * working in closed environments, i.e. without an internet connection
( ### * checking availability of ciphers independent of installed library
) ### * checking for all possible ciphers (up to 65535 per SSL protocol)
( ### * needs just Perl without modules for checking ciphers and protocols
) ### * mainly the same results on all platforms
Changelog v24.01.24
New
* OSaft/Doc/openssl.txt: ND: file for internal (developer) documentation
* Net/SSLinfo.pm: EF: test_openssl() for –test-openssl implemented
* t/Makefile.mod: ET: target testarg-mod-Net-SSLinfo.pm_–test-openssl added
* t/Makefile.cipher: ET: targets added to test +cipher –trace*
* t/Makefile.cipher: ET: target testcmd-cipher-+cipher—openssl-local_ added
* t/Makefile.warnings: ET: warning-015 implemented, warning-413 implemented
* osaft.pm EF: cfg{openssl_version} added
* OSaft/Ciphers: EF: cophers TLS13_GOSTR341112_256* added
* OSaft/Trace.pm: NF: added (replace o-saft-dbx.pm 2.44)
* OSaft/USR.pm: NF: added (replace o-saft-usr.pm 2.8)
BugFix
* o-saft.pl: BT: print sorted list of ciphers for –ciphermode=dump (important for testing only)
* o-saft.pl: BF: avoid “Use of …” for –legacy=testsslserver
output for –legacy=testsslserver may now miss some informations values
* t/Makefile.warnings: BT: duplicate target warning-141 removed
* OSaft/Ciphers: BD: description for $cipher_results adapted to new definitions
* Net/SSLhello.pm: BF: typos in cipher suite names corrected
* o-saft-dbx.pm: BF: avoid “Use of uninitialized value in join or string …”; output for –trace=3 improved
* o-saft-man.pm: BF: <details> tag with overflow-y:auto
* o-saft-man.pm: BF: <aside> tag with higher z-index
More…
Download
git clone git@github.com:OWASP/O-Saft.git
Copyright (C) 2013 Achim Hoffmann
Source: https://github.com/OWASP/