Spray365 v0.2.2 beta releases: password spraying tool
What is Spray365?
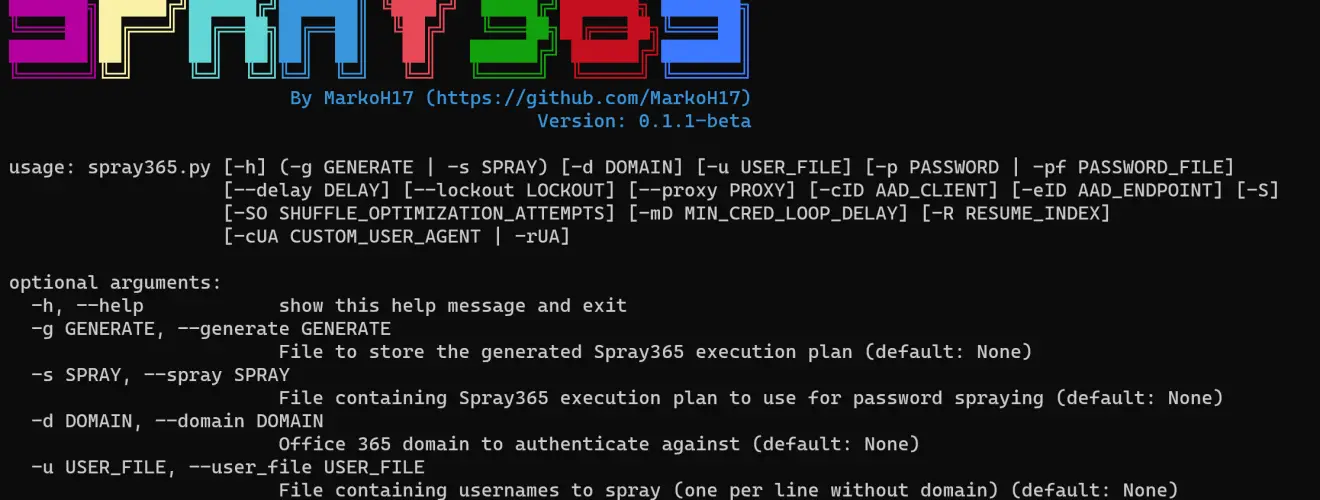
Spray365 is a password spraying tool that identifies valid credentials for Microsoft accounts (Office 365 / Azure AD). How is Spray365 different from the many other password spraying tools that are already available? Spray365 enables passwords to be sprayed from an “execution plan”. While having a pre-generated execution plan that describes the spraying operation well before it occurs has many other benefits that Spray365 leverages, this also allows password sprays to be resumed (-R option) after a network error or other interruption. While it is easiest to generate a Spray365 execution plan using Spray365 directly, other tools that produce a compatible JSON structure make it easy to build unique password spraying workflows.
Spray365 exposes a few options that are useful when spraying credentials. Random user agents can be used to detect and bypass insecure conditional access policies that are configured to limit the types of allowed devices. Similarly, the –shuffle_auth_order argument is a great way to spray credentials in a less-predictable manner. This option was added in an attempt to bypass intelligent account lockouts (e.g., Azure Smart Lockout). While it’s not perfect, randomizing the order in which credentials are attempted has other benefits too, like making the detection of these spraying operations even more difficult. Spray365 also supports proxying traffic over HTTP/HTTPS, which integrates well with other tools like Burp Suite for manipulating the source of the spraying operation.
Changelog v0.2.2 beta
🎉 What’s New
- Review module now shows which AAD endpoints are accessible (e.g., not protected by MFA / conditional access policies)
🏗️ What’s Changed
- Exceptions are now displayed in more detail to aid in debugging
- Code cleanup (import re-ordering)
Install
$ git clone https://github.com/MarkoH17/Spray365
$ cd Spray365
~/Spray365$ pip3 install -r requirements.txt
Use
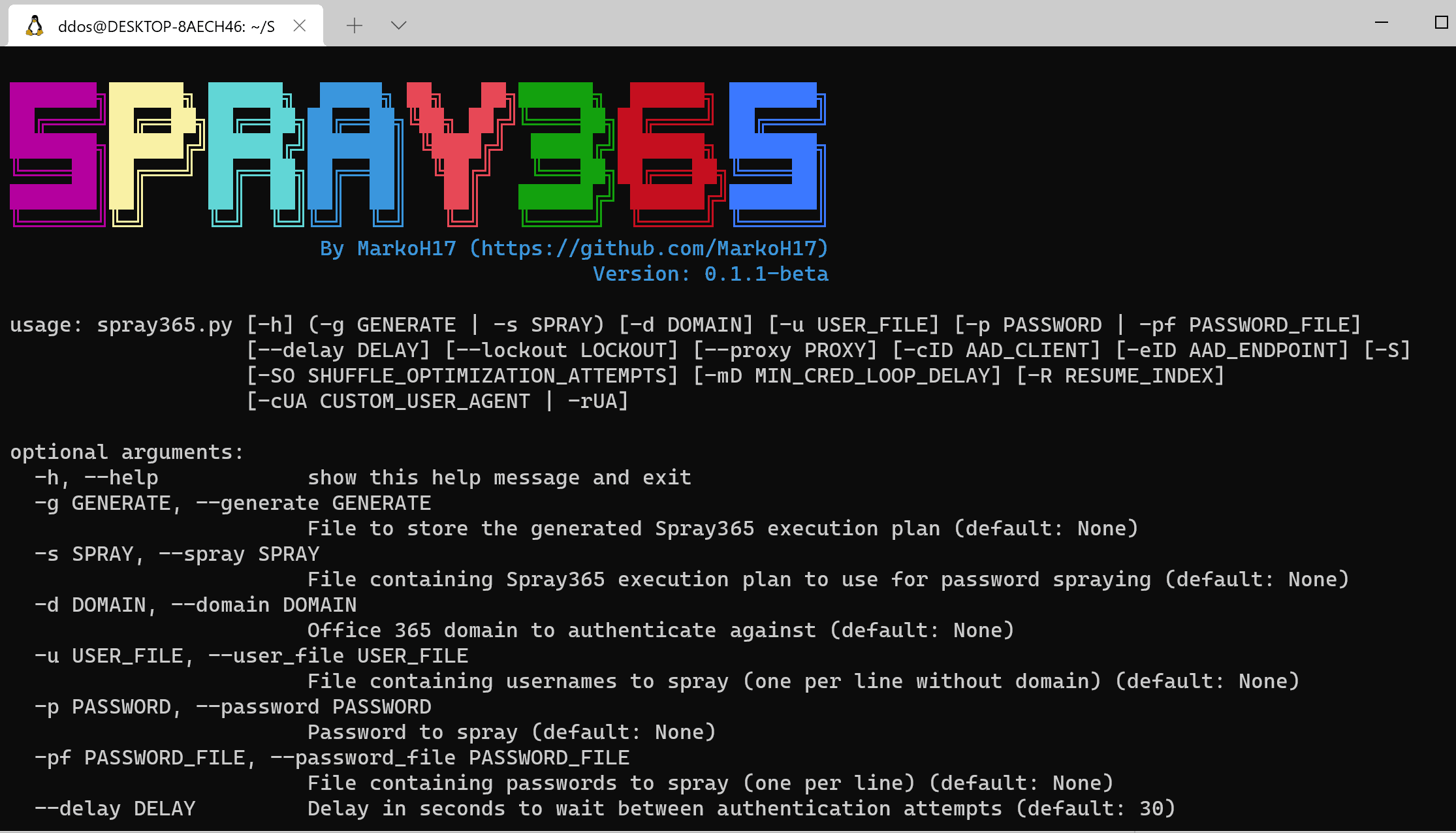
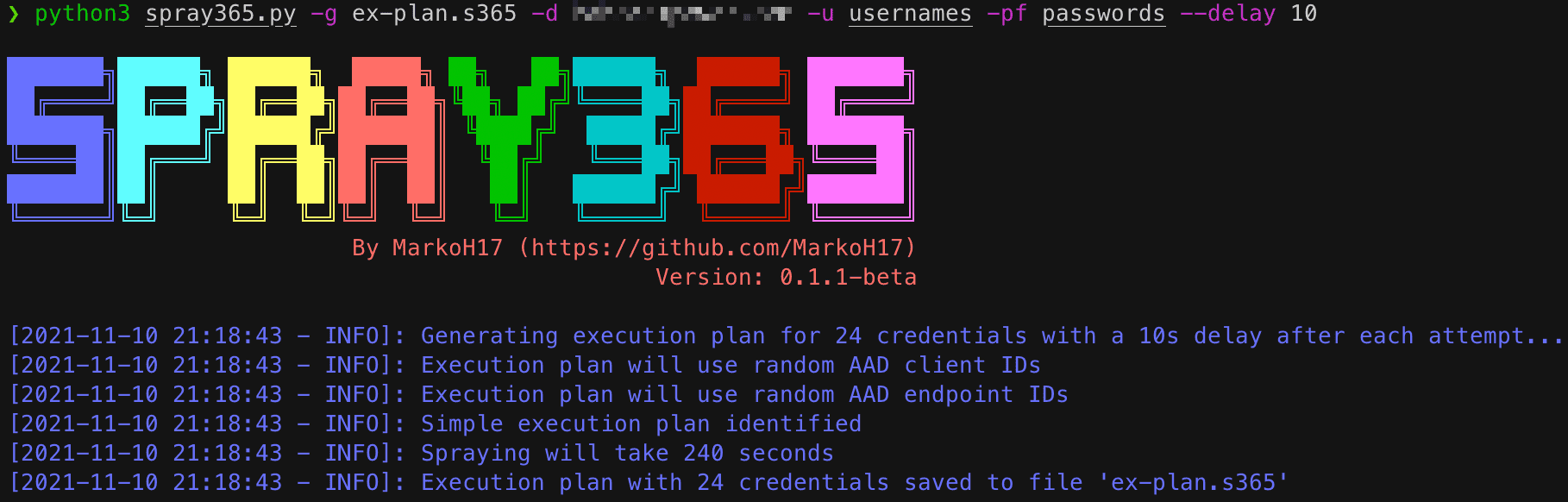
Generate an Execution Plan
An execution plan is needed to spray credentials, so we need to create one! Spray365 can generate its own execution plan by running it in “generate” (-g) mode.
$ python3 spray365.py -g <path_for_saved_execution_plan> -d <domain_name> -u <file_containing_usernames> -pf <file_containing_passwords>
e.g.
$ python3 spray365.py -g ex-plan.s365 -d example.com -u usernames -pf passwords
Spraying an Execution Plan
Once an execution plan is available, Spray365 can be used to process it. Running Spray365 in “spray” (-s) mode will process the specified execution plan and spray the appropriate credentials.
$ python3 spray365.py -s <path_to_execution_plan>
e.g.
$ python3 spray365.py -s ex-plan.s365
Copyright (c) 2021 Mark Hedrick
Source: https://github.com/MarkoH17/






