Paladin Cloud v3.0.1 releases: an extensible, Security-as-Code (SaC) platform

Paladin Cloud
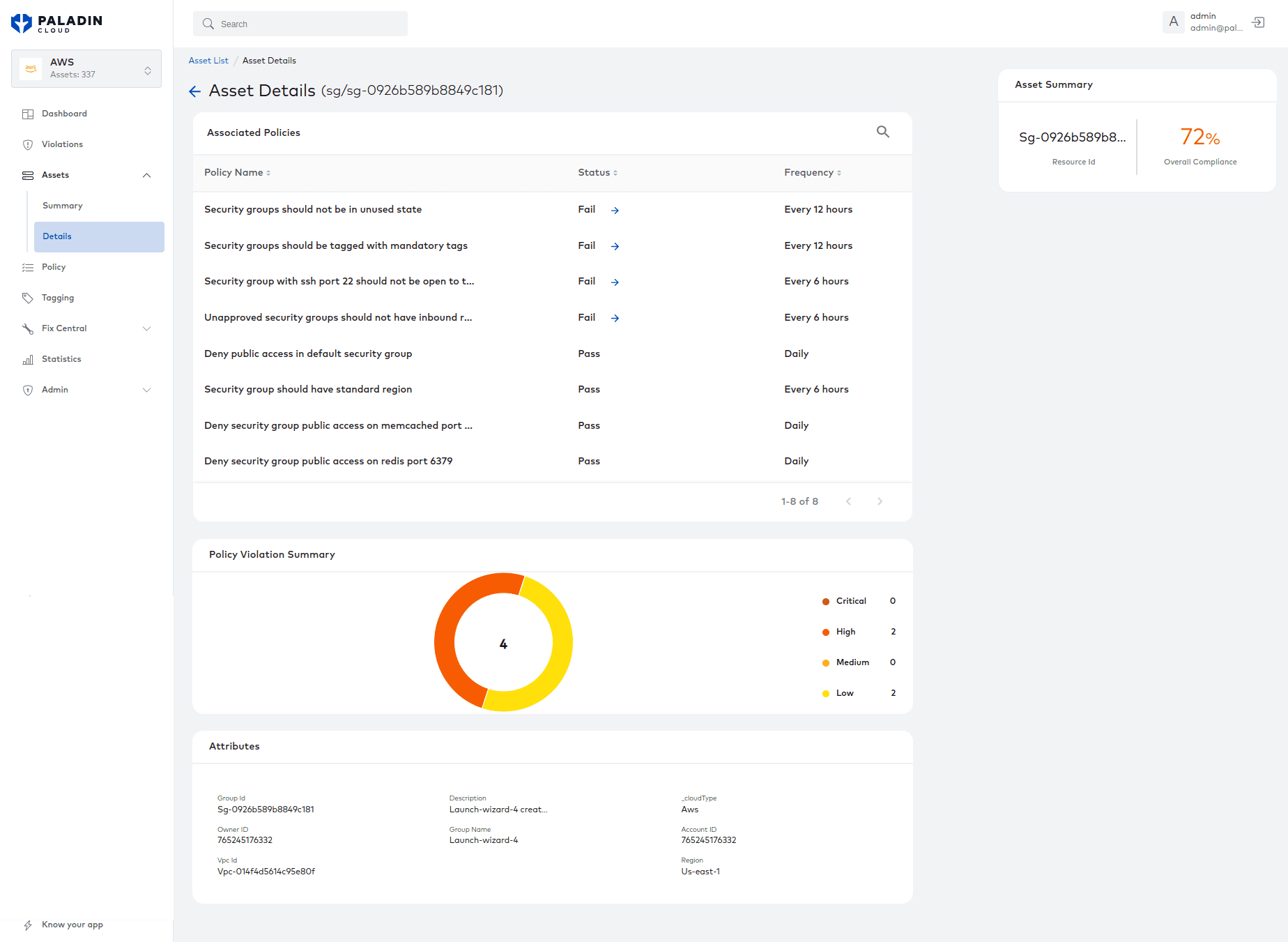
Paladin Cloud is an extensible, Security-as-Code (SaC) platform designed to help developers and security teams reduce risks in their cloud environments. It functions as a policy management plane across multi-cloud and enterprise systems, protecting applications and data. The platform contains best-practice security policies and performs continuous monitoring of cloud assets, prioritizing security violations based on severity levels to help you focus on the events that matter..
Its resource discovery capability creates an asset inventory, then evaluates security policies against each asset. Powerful visualization enables developers to quickly identify and remediate violations on a risk-adjusted basis. An auto-fix framework provides the ability to automatically respond to policy violations by taking predefined actions.
Paladin Cloud is more than a tool to manage cloud misconfiguration. It’s a holistic cloud security platform that can be used for continuous monitoring and reporting across any domain.

Extend your Coverage
Paladin Cloud’s plugin-based connector architecture allows for data ingestion from multiple sources. Plugins allow you to pull data from various cloud-based enterprise systems, such as Kubernetes management, API gateways, and threat intelligence systems in order to holistically manage cloud security. Examples include Qualys Vulnerability Assessment Platform, Bitbucket, TrendMicro Deep Security, Tripwire, Venafi Certificate Management, and Redhat. You can write rules based on data collected by these plugins to get a complete picture of your cloud security posture.
How Does It Work?
Assess -> Report -> Remediate -> Repeat
Paladin Cloud constantly assesses and monitors your cloud security posture on a near real-time basis. The platform discovers assets, evaluates policy, creates issues for policy violations, and prioritizes remediation. If an auto-fix is configured with the policy, those auto-fixes are executed when the resources fail the evaluation. Policy violations can not be closed manually; the issue must be fixed on the inspected asset, and then Paladin Cloud will mark it closed in the next scan.
Exceptions can be added to policy violations. Sticky exceptions (exceptions based on resource attribute matching criteria) can be added to exempt similar resources that may be created in the future. Note that exceptions should be used sparingly and only if they are aligned with corporate security guidelines.
Asset groups are a powerful way to visualize cloud security and compliance. Asset groups are created by defining one or more target resource’s attribute-matching criteria. For example, you could create an asset group of all running assets by defining criteria to match all EC2 instances with attribute instancestate.name=running. Any new EC2 instance launched after the creation of an asset group will be automatically included in the group.
In the Paladin Cloud UI, you can select the scope of the portal to a specific asset group. All the data points shown in the UI will be confined to the selected asset group. It is common practice to create asset groups per account (or subscription, project), per application, per business unit, or per environment.
Asset groups are not just for setting the scope of the data shown in the UI. The groups can be used to scope rule execution as well. Policies contain one or more rules. These rules can be configured to run against all resources or a specific asset group. The rules will evaluate all resources in the asset group configured as the scope for the rule. This provides an opportunity to write policies that are very specific to an application or organization.
A good example is when some teams would like to enforce additional tagging standards beyond the global requirements. They implement this policy with their custom rules and configure it to run only on their assets.
Paladin Cloud Key Capabilities
- Continuous asset discovery
- Continuous security policy evaluation
- Detailed reporting
- Auto-Fix for policy violations
- Ability to search all discovered resources
- Simplified policy violation tracking and prioritization
- Easy to use Self-Service portal
- Custom policies and custom auto-fix actions
- Dynamic asset grouping to view compliance
- Ability to create multiple compliance domains
- Exception management
- Email digests
- Supports unlimited AWS, Azure, and GCP accounts
- Completely automated installer
- OAuth2 Support
- Azure AD integration for login
- Role-based access control
Changelog v3.0.1
UI Changes
- Fixed bugs across the application
- Enhanced the filtering on UI list views
Policy Updates
- Added 3 Azure and 2 GCP cost policies
- Updated the Policy documentation
- Enhanced the Policy implementation for a few policies.
- Other minor policy fixes and updates
- Updated the resolution links for all the policies to point to appropriate descriptions
Other Updates
- Fixed bugs related to Azure and GCP autofix functionality
What’s Changed
- Chores/pavel test workflow by @plyubich in #1474
- fix: [UIUX-281] change status filter option from configured to online by @sidharthjain-zemoso in #1466
- fix:[CUS-172] update subscriptionStatus correctly in azure subscripti… by @raviteja-mandala in #1475
- fix:[CORE-938][CORE-1079] Plugins Date format and updated PolicyDispl… by @kushZemoso in #1463
- feat: preapply status filter in violations screen by @sidharthjain-zemoso in #1467
- bug:[CORE-1148]plugin status filter issue by @shefalibisht1992 in #1473
- fix:[Core-959] Set date according to the payload. by @kushZemoso in #1476
- removed trynow from README.md by @PaladinCloudJohn in #1480
- fix:[CUS-180][CORE-1186][CORE-1097] update db enteries for policies. by @kushZemoso in #1481
- Fix/data dog issues by @raviteja-mandala in #1479
- fix:[CORE-1207] fix for data dog reported issue with policy – Enable_… by @raviteja-mandala in #1484
- fix:[CORE-1214]Fix policyUUID by @AishwaryaKulkarni97 in #1485
- fix:[CORE-1051]Rename policy by @AishwaryaKulkarni97 in #1478
- fix:[CORE-1069] CE sync by @AnandPaladin in #1482
- fix:[CORE-1209] fix for data dog reported issue for rule – AWS_IAM_Us… by @raviteja-mandala in #1490
- fix:[CORE-1230][CORE-1241][CORE-1242]Ops Alert by @AishwaryaKulkarni97 in #1492
- fix:[CORE-1231]Ops Alert by @AishwaryaKulkarni97 in #1493
- refact: violations column names map code by @sidharthjain-zemoso in #1477
- chore:[devops-95]acs_notification by @rnithinpaladin in #1483
- fix:[CORE-1227]Fix email values by @AishwaryaKulkarni97 in #1486
- fix:[CORE-841]AWS resolutions links by @AishwaryaKulkarni97 in #1488
- fix:[CORE-1135]GCP resolutions links by @AishwaryaKulkarni97 in #1489
- bug:[CORE-1240]region filter url corrected by @shefalibisht1992 in #1491
- fix:[CORE-1138]Azure Links by @AishwaryaKulkarni97 in #1495
- bug:[CORE-1220]removing fixed filter from issues api and omitting iss… by @shefalibisht1992 in #1497
- bug:[CORE-1249]violation api failure by @shefalibisht1992 in #1496
- fix: gcp asset loadbalancer and cloudstorage mapping fix. by @arunpaladin in #1499
- fix:[CORE-1206] fix for data dog reported issue for policy – IamPassw… by @raviteja-mandala in #1494
- bug:[CORE-1251]issues filter need to skip issues with unknown status. by @shefalibisht1992 in #1501
- Fix/violation asset filters by @sidharthjain-zemoso in #1498
- bug:[CORE-1257]region sort breaks by @shefalibisht1992 in #1502
- bug:[CUS-183]correcting asset api download endpoint by @shefalibisht1992 in #1503
- bug:[CORE-1265]severity fails when autofix is true by @shefalibisht1992 in #1506
- fix:[CORE-1138][CORE-1135][CORE-841]Missing resolution Links by @AishwaryaKulkarni97 in #1509
- fix:[CUS-179]Updated policy description by @AishwaryaKulkarni97 in #1510
- Porting/ce ee changes by @ranadheer-b in #1504
- bug:[CUS-192]download api failure by @shefalibisht1992 in #1511
- fix:Sorted TargetType List on DisplayName field by @kushZemoso in #1512
- fix:[Core-1015] Added cloud Type in Duplicate DisplayName. by @kushZemoso in #1508
- feat:[CUS-160][CUS-161] Gcp cost Policies. by @kushZemoso in #1505
- Fix/list download by @sidharthjain-zemoso in #1514
- feat:[PLG-150] RedHat Deployment asset by @arunpaladin in #1513
- fix:[CORE-1263] CE Sync by @AnandPaladin in #1515
- fix: sorted filter options irrespective of case by @sidharthjain-zemoso in #1516
- fix:[CORE-1274][CORE-1275][CORE-1277][CORE-1276]Ops alert by @AishwaryaKulkarni97 in #1518
- fix:[CORE-760]Issue audit log captures request and revoke request by @AishwaryaKulkarni97 in #1519
- Fix/asset details by @ranadheer-b in #1521
- fix:[CORE-1201] Fix for rate exceeded issue by @raviteja-mandala in #1520
- fix:[CORE-760]Issue audit log captures grant and deny request exemption by @AishwaryaKulkarni97 in #1523
- fix:[CUS-196]fix azure cost policies. by @kushZemoso in #1525
- fix:[CORE-1288] fix for remove unused vm disk rule by @raviteja-mandala in #1524
- fix:[CORE-1058] CE Sync by @AnandPaladin in #1526
- fix:[CUS-161] Delete Unused VM disk. by @kushZemoso in #1527
- fix:Added UUID in rulengine.json by @kushZemoso in #1528
- fix:VM ScaleSet collector. by @kushZemoso in #1531
- fix:[CUS-217] Gcp Disks Collector. by @kushZemoso in #1535
- Fix/fix for npe azure collector by @raviteja-mandala in #1530
- Fix/violations filters by @sidharthjain-zemoso in #1537
- fix:[CORE-1239]Search in violation filter by @AishwaryaKulkarni97 in #1538
- bug:[CORE-978]autofix filter by @shefalibisht1992 in #1539
- feat: [PLG-174],[PLG-175] Added Node and Cluster asset by @arunpaladin in #1533
- Feat: [PLG-63] [PLG-162] [PLG-152] Added Violation, Polices and Images assets in shipper by @arunpaladin in #1541
- fix:[CORE-349][CORE-1216] policy category and severity. by @kushZemoso in #1542
- fix:[CORE-1290]Violation should not be raised when permission not given by @AishwaryaKulkarni97 in #1543
- fix:[CORE-1315]Ignore data dog alerts for Trusted advisor by @AishwaryaKulkarni97 in #1545
- fix:[CORE-1298][CORE-1300] Policy Sort by fixing the displayName. by @kushZemoso in #1546
- fix:[CORE-760]Request and revoking exemption should be captured in au… by @AishwaryaKulkarni97 in #1544
- Fix/ce porting for assetdetails fix by @raviteja-mandala in #1551
- fix:[CORE-1304] handle NPE when fetching addOnProfiles() for kubernet… by @raviteja-mandala in #1552
- Feat/redhat new assets by @arunpaladin in #1553
- Fix/violation filters by @sidharthjain-zemoso in #1550
- Porting EE changes to CE by @ranadheer-b in #1554
- fix:[CORE-1379] handle noentityfound exception for iam policies by @raviteja-mandala in #1556
- Fix/redhat display name by @sidharthjain-zemoso in #1555
- fix:[CORE-1348] fix for data ops alerts for cequence by @raviteja-mandala in #1557
- Fix/handle nosuchentityexcpetion for iampolicies by @raviteja-mandala in #1558
- feat:[CUS-170] Added ec2 launch template. by @kushZemoso in #1540
- fix:[CORE-1385] changed Platfrom and CloudType to Source. by @kushZemoso in #1560
- fix:[CUS-170] added region in keys. by @kushZemoso in #1561
- fix:[CORE-1391] Fix for data dog alert issues reported for vertex by @raviteja-mandala in #1565
- fix:[CORE-1352]Remove ops alert for access denied by @AishwaryaKulkarni97 in #1562
- PLG-186-Shipper Changes by @AnandPaladin in https://github.com/Pala…






