pe_to_shellcode v1.2 releases: Converts PE into a shellcode
pe_to_shellcode
Converts PE so that it can be then injected just like a normal shellcode.
(At the same time, the output file remains to be a valid PE).
Supports both 32 and 64-bit PEs
Objective:
The goal of this project is to provide a possibility to generate PE files that can be injected with minimal effort. It is inspired by Stephen Fewer’s ReflectiveDLLInjection – but the difference is that with pe2shc you can add the reflective loading stub post-compilation. Also, the header of the PE file is modified in such a way, that you can start executing the injected buffer from the very beginning – just like you would do with a shellcode. It will automatically find the stub and continue loading the full PE.
Changelog v1.2
FEATURE
- The shellcodified module keeps a state informing whether it was executed, etc
- Added: DLL detach, that allows to cleanly finish execution of a shellcodified DLL
- the shellcodified DLL can be detached simply by a second run (while the first run calls
DllMainwithDLL_PROCESS_ATACH, the second calls it withDLL_PROCESS_DETACH)
- the shellcodified DLL can be detached simply by a second run (while the first run calls
The package contains:
- pe2shc.exe – PE to shellcode converter (supports both 32 and 64 bit PEs)
- a utility to run/test shellcode (loads and deploys):
- runshc32.exe – for 32-bit shellcodes
- runshc64.exe – for 64-bit shellcodes
- a utility to inject shellcode into a given process:
- injector32.exe – for 32-bit shellcodes
- injector64.exe – for 64-bit shellcodes
Download
Use
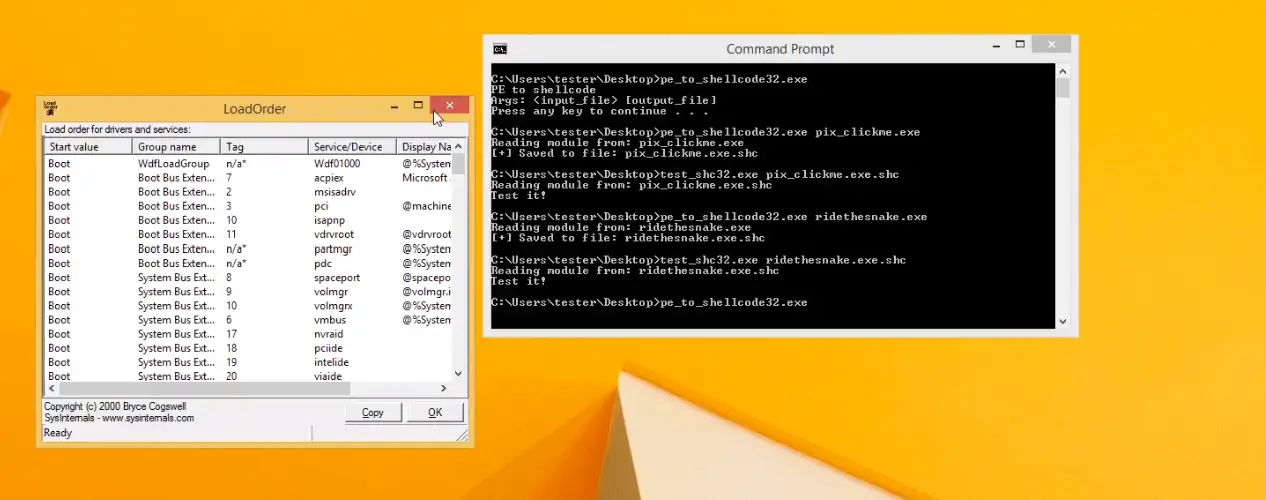
- Use pe2shc.exe to convert a PE of your choice:
pe2shc.exe <path to your PE> [output path*] * - optional
If the PE was successfully converted, pe2shc will let you know where the output was saved:
[+] Saved to file: <converted file>
i.e.
[+] Saved to file: test_file.shc.exe
- Use runshc.exe(*) to run the output file and check if the conversion went fine.
runshc.exe <converted file>
(*)Warning: remember to use the version of runshc with a bitness appropriate to your converted application (32 or 64 bit) – otherwise the application will crash!
- If the file runs as the original PE, it confirms that the conversion was successful!
Now you can use the converted PE just like you would use a shellcode: inject it to a target and execute from the beginning of the buffer. No additional PE loaders are required.
At the same time, you can keep using the converted file as a regular PE.
Demo
Source: https://github.com/hasherezade/






