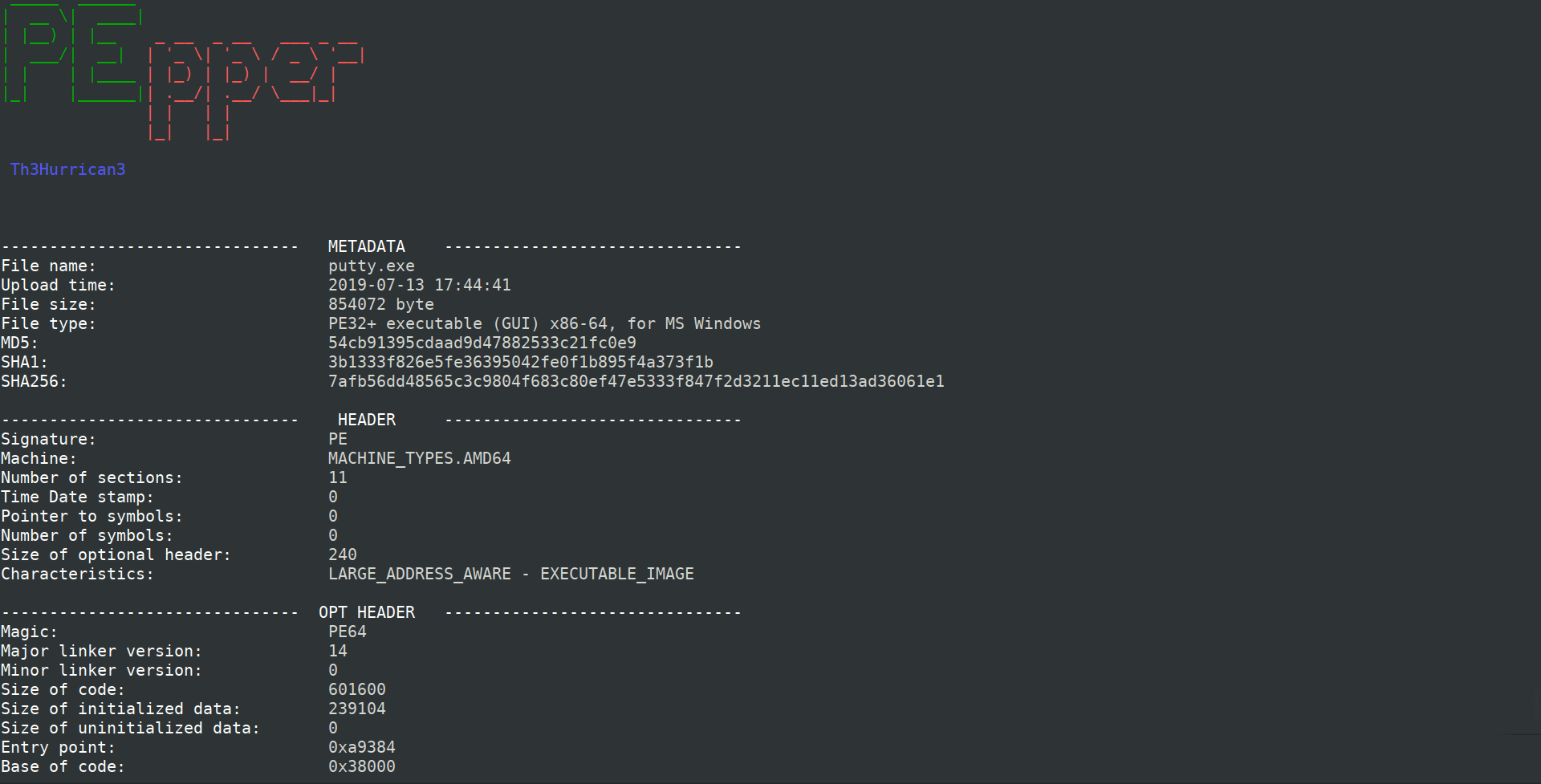
PEpper
An open source tool to perform malware static analysis on Portable Executable.
Feature extracted
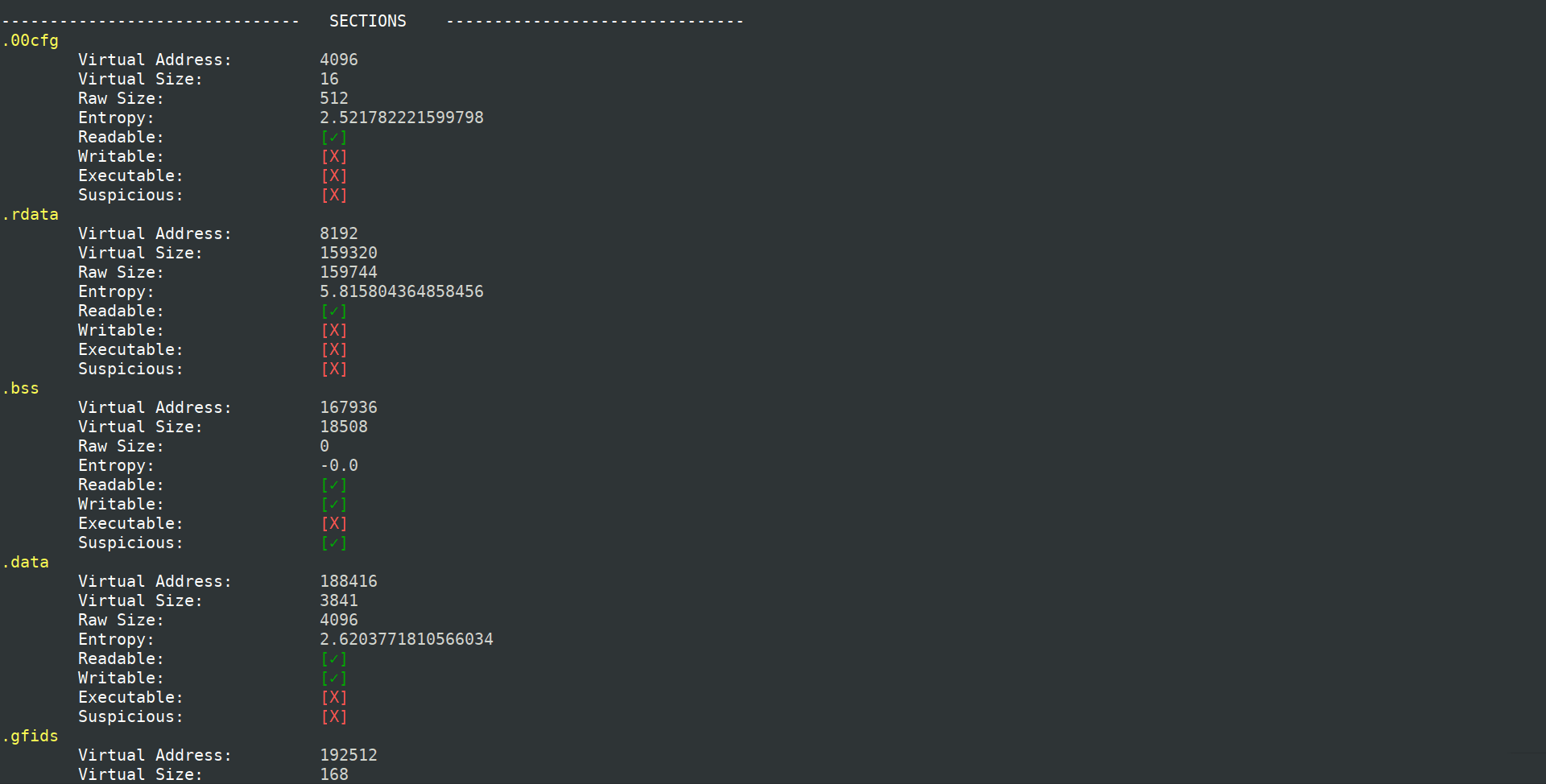
- Suspicious entropy ratio
- Suspicious name ratio
- Suspicious code size
- Suspicious debugging time-stamp
- Number of export
- Number of anti-debugging calls
- Number of virtual-machine detection calls
- Number of suspicious API calls
- Number of suspicious strings
- Number of YARA rules matches
- Number of URL found
- Number of IP found
- Cookie on the stack (GS) support
- Control Flow Guard (CFG) support
- Data Execution Prevention (DEP) support
- Address Space Layout Randomization (ASLR) support
- Structured Exception Handling (SEH) support
- Thread Local Storage (TLS) support
- Presence of manifest
- Presence of version
- Presence of digital certificate
- Packer detection
- VirusTotal database detection
- Import hash
Installation
git clone https://github.com/Th3Hurrican3/PEpper.git
cd PEpper
pip3 install -r requirements.txt
Use
python3 pepper.py ./malware_dir
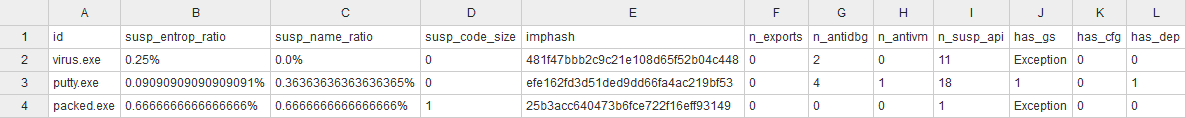
CSV output
and more columns.
Copyright (C) 2019 Th3Hurrican3
Source: https://github.com/Th3Hurrican3/