polichombr: Collaborative malware analysis framework
Polichombr
This tool aims to provide a collaborative malware analysis framework. It was originally presented at SSTIC 2016,
Analysis platform
Polichombr is designed to help analysts to reverse malware, as a team. It provides an engine to automate the analysis tasks, and identify hotpoints in the binary, a script to collaborate during the reverse of binaries, and can be used to store and manage pieces of information about malware families.
Taking notes right from IDA
Plugins / tasks
Tasks are loaded from the app/controllers/tasks directory and must inherit from the Task object. In particular, several tasks are already implemented:
- AnalyzeIt, a ruby script based on metasm, which is used to identify interesting points in the binary. The goal is to help the analyst by giving hints about where to start. For example, we try to identify crypto loops, functions which call sensitive API (file, process, network, …)
- Peinfo: We load the PE metadata with the peinfo library.
- Strings: extract ASCII and Unicode strings
Signatures
We use several signature models to classify malware:
- Yara
- imphash
- Machoc
Machoc
Machoc is a CFG-based algorithm to classify malware. For more information, please refer to this paper.
Skelenox
This is an IDAPython script, which is used to synchronize the names and comments with the knowledge base, and with other users database
Usage
Example
Scripts under the folder examples permit some basic actions for a Polichombr instance.
Generic sample information
Family/Threat overview
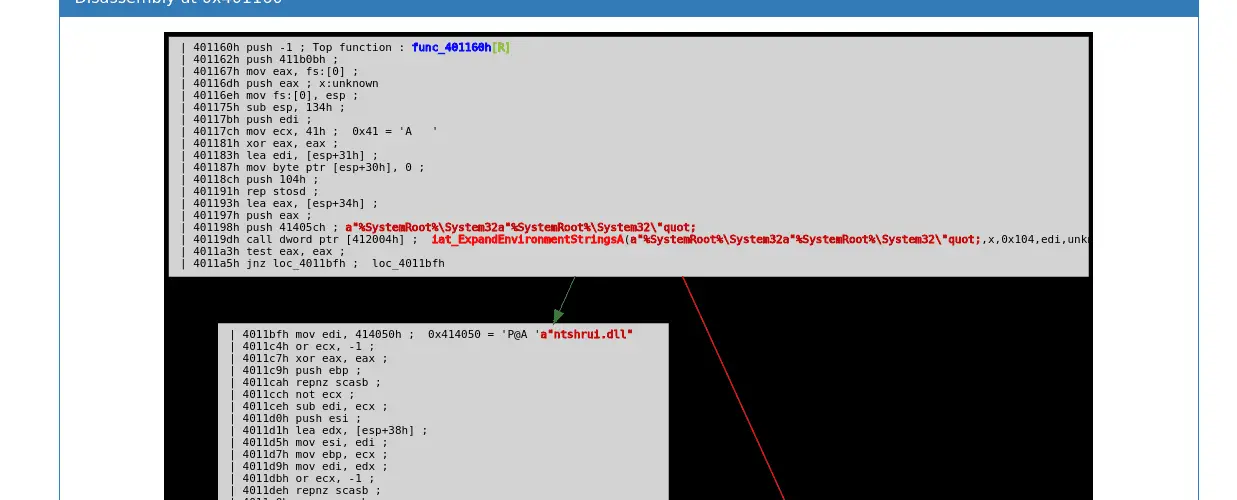
Online disassembly
Share IDA Pro information from the WebUI / directly to other users
Automated hotpoints detection
Source: https://github.com/ANSSI-FR/












