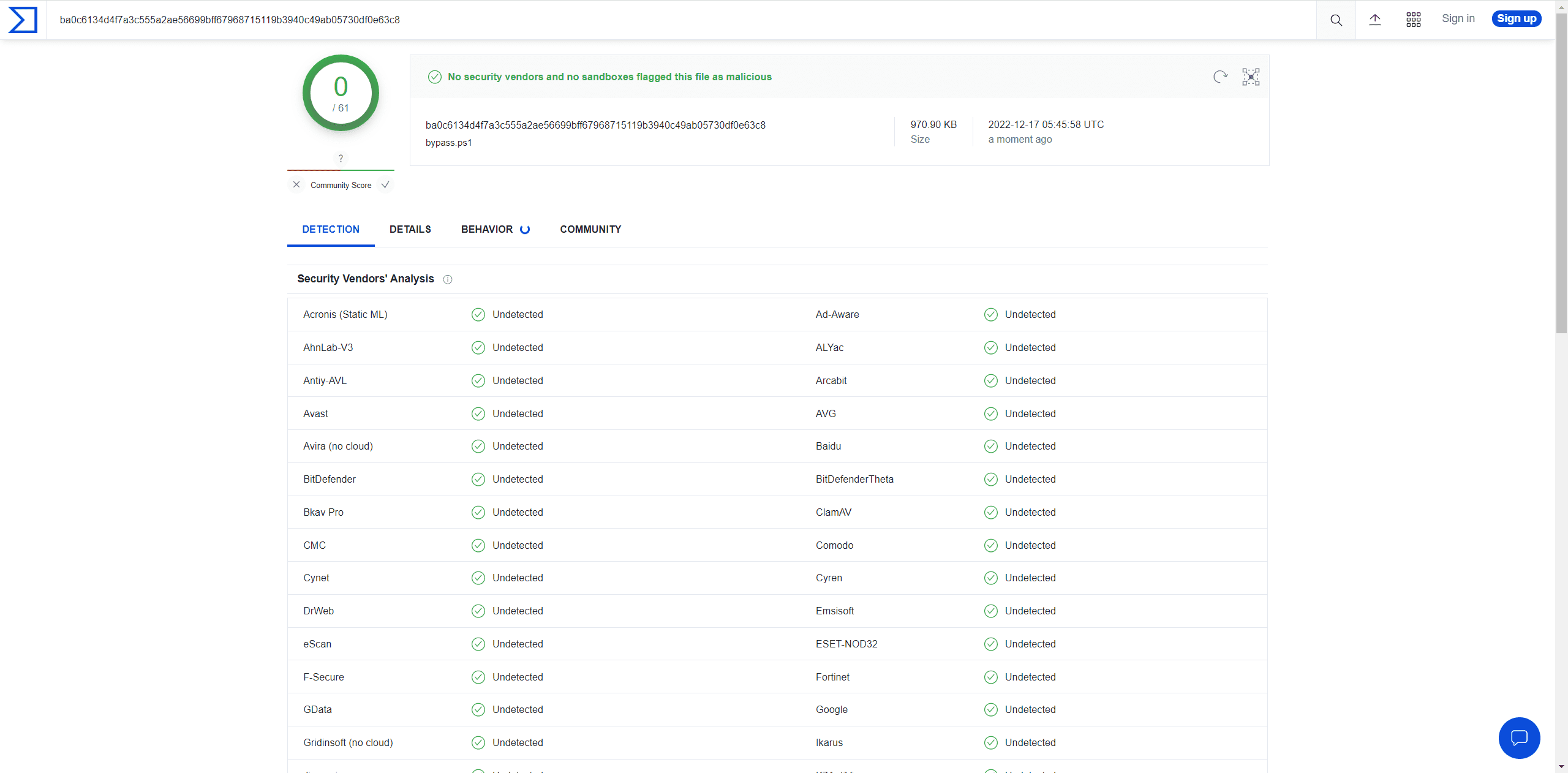
powershell obfuscation: simple and effective powershell obfuscaiton tool bypass Anti-Virus
Powershell obfuscation
A simple and effective powershell obfuscation tool bypass Anti-Virus, VT.
AMSI-bypass obfuscation + ETW-block obfuscation + powershell command obfuscation.
The tool with the best anti-obfuscation effect at present should be《Invoke-Deobfuscation: AST-Based and Semantics-Preserving Deobfuscation for PowerShell Scripts》. This paper uses variable tracking and invoke de-obfuscation at the AST level, the effect is much better than that of defender and VT.
However, this paper also mentioned the difficulties of the current powershell anti-obfuscation research. One is that the custom function encryption cannot be de-obfuscated, and the other is that it is difficult to track the variables in the loop.
Since some de-obfuscation tools de-obfuscate at the AST level, most of the encryption/encoding functions that come with powershell are useless, such as [System.Convert]::FromBase64String and so on. You should use custom encryption and decryption functions as much as possible.
Aiming at the difficulties of this academic research, I wrote a simple powershell obfuscator, and it turns out that the result is really good. The specific ideas are as follows:
-
Customize the encryption and decryption functions. In the function, reverse the string (reversing string does not use the function that comes with powershell to prevent de-confusing at the AST level) and the +- operation of characters (the reason why the XOR operation is not used here is that the defender monitors -bxor strictly).
-
Perform several loop operations on the encryption and decryption function.
-
In order to allow the characters to be effectively output, it is finally encoded with base64 (even if it is decoded at the AST level, it does not matter, because the decoded content is still obfuscated).
This tool implements AMSI-bypass obfuscation, ETW-block obfuscation, and powershell command obfuscation.
Download
git clone https://github.com/H4de5-7/powershell-obfuscation






