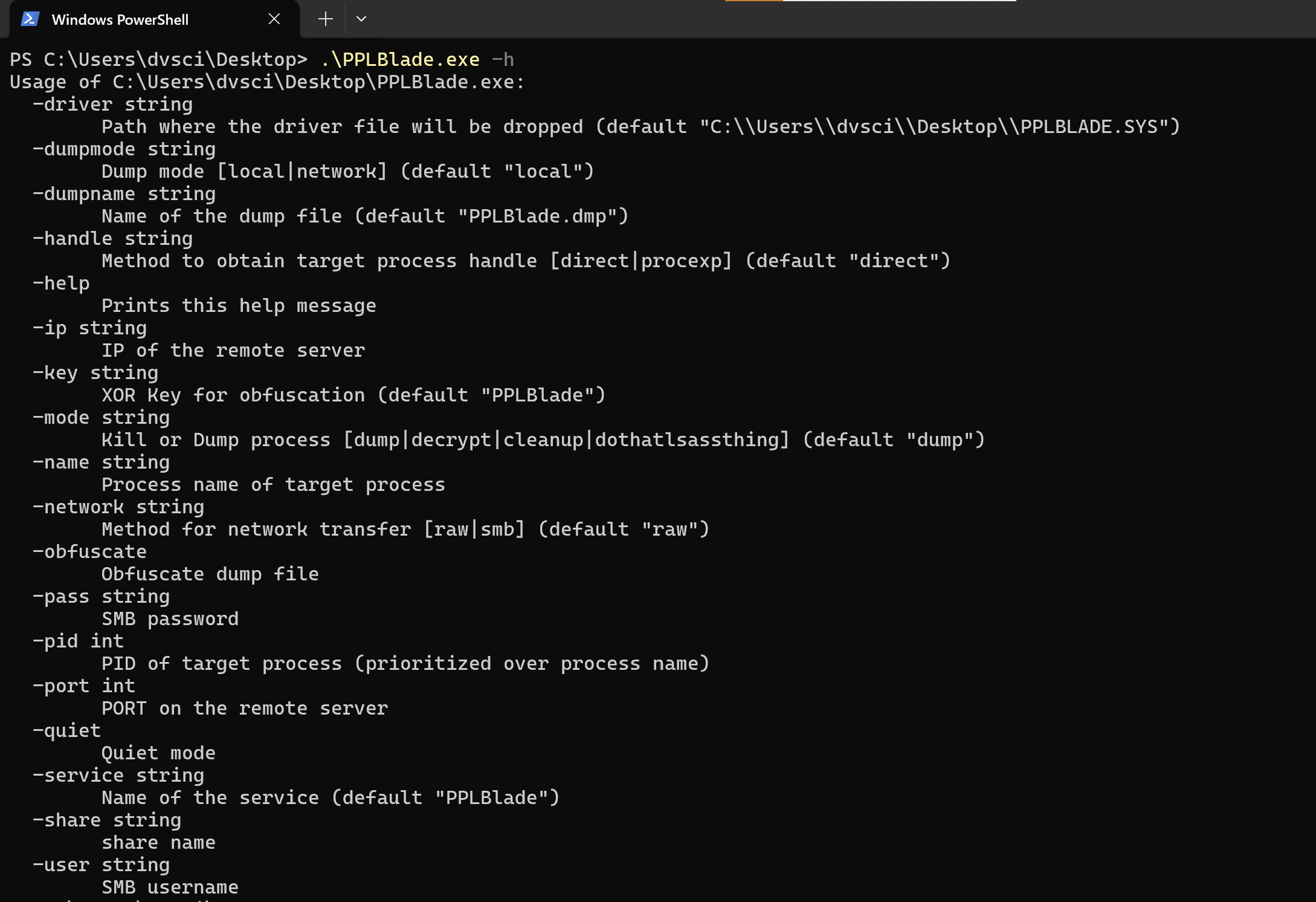
PPLBlade: Protected Process Dumper Tool
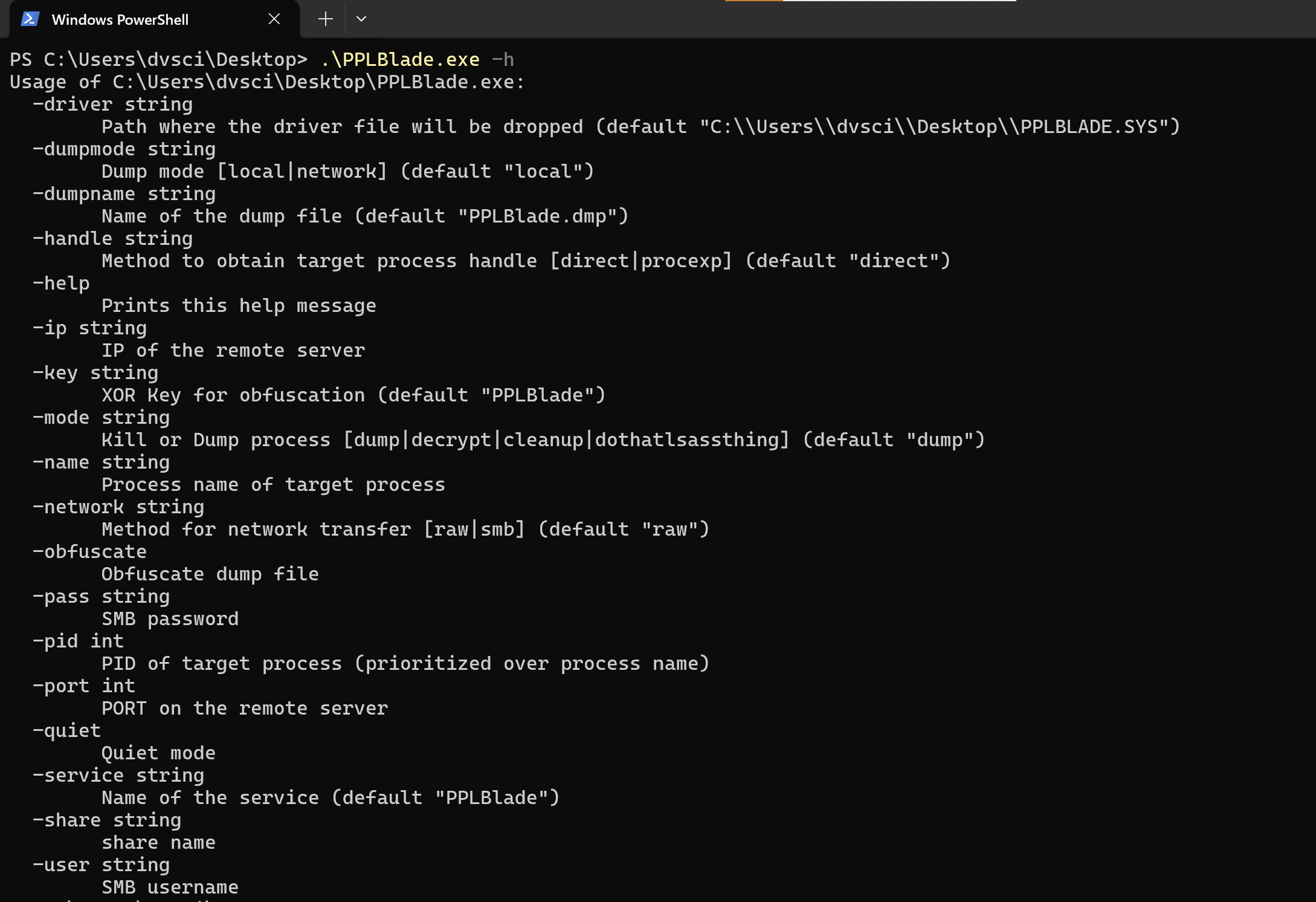
PPLBlade
Protected Process Dumper Tool that supports obfuscating memory dump and transferring it on remote workstations without dropping it onto the disk.
Key functionalities:
- Bypassing PPL protection
- Obfuscating memory dump files to evade Defender signature-based detection mechanisms
- Uploading memory dump with RAW and SMB upload methods without dropping it onto the disk (fileless dump)
An overview of the techniques, used in this tool can be found here.
Note that PROCEXP15.SYS is listed in the source files for compiling purposes. It does not need to be transferred on the target machine alongside the PPLBlade.exe.
It’s already embedded into the PPLBlade.exe. The exploit is just a single executable.
Modes:
- Dump – Dump process memory using PID or Process Name
- Decrypt – Revert obfuscated(–obfuscate) dump file to its original state
- Cleanup – Do cleanup manually, in case something goes wrong on execution (Note that the option values should be the same as for the execution, we’re trying to clean up)
- DoThatLsassThing – Dump lsass.exe using Process Explorer driver (basic poc)
Handle Modes:
- Direct – Opens PROCESS_ALL_ACCESS handle directly, using OpenProcess() function
- Procexp – Uses PROCEXP152.sys to obtain a handle