Racketeer Project: Ransomware emulation toolkit
Racketeer Project – Ransomware emulation toolkit
The goal of this project is to provide a way for teams to simulate and test detection of common ransomware operations, in a controlled manner, against a set of company assets and network endpoints.
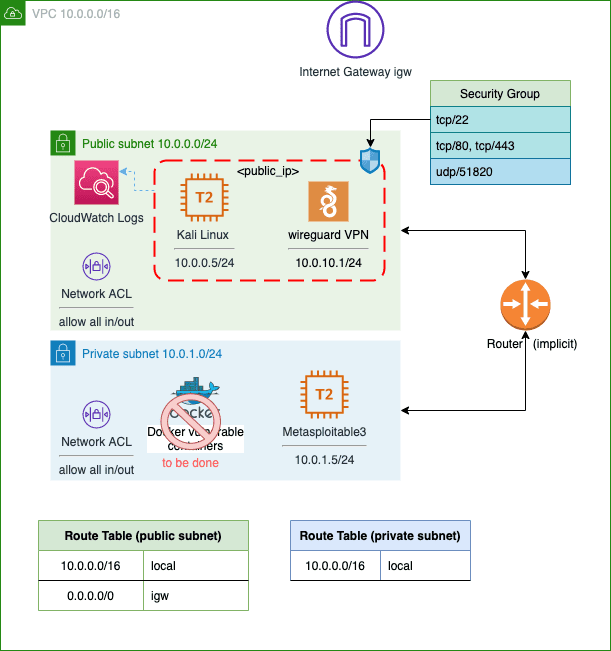
Deployment model
The Racketeer toolkit operates on an agent/base model and currently supports Windows OS systems at the agent level, while the command and control base cross-platform.
Architecture diagram
Agent features and operation
RNS agent is an executable which is deployed on an asset for the purpose of carrying out tasks sent to it from the base (C2).
The primary job of the RNS agent is to perform:
- Local or networked encryption and decryption of files within an environment.
- Managing one or several network account credentials.
- Managing connectivity to the base.
Secondary tasks include:
- Revealing agent presence by signaling a console or launching a payment collection or notification application.
- Managing run logs
- Self-termination and cleanup
Currently, encryption and decryption are performed with a set of pre-shared keys, loaded as part of the policy into the agent.
The encryption keys can be specified per host, or per file, which allows for a more granular approach for the offensive team to manage decryption in the field after a simulated attack.
The run of the policy is triggered by providing a correct master key which ensures proper authentication of the intent and serving as a key for managing shielded account credentials to avoid leaks.
RNS Agent is governed by a policy which is comprised of a set of configuration directives used for both the operation of the agent and its interaction with the assets it is meant to encrypt. The policy can be dynamically pushed to the agent by the base, or it can be embedded into the agent for certain lights-out scenarios.