In March and April 2023, cybersecurity researchers at Trend Micro uncovered a new ransomware variant, dubbed “Rapture,” that employs a minimalistic approach and leaves a minimal footprint. The findings provide insight into the attackers’ preparations and the rapidity with which they execute the ransomware attack.
Rapture shares similarities with the Paradise ransomware, such as the RSA key configuration file and the requirement of a .NET 4.0 framework for execution. However, Rapture’s behavior differs from that of Paradise. The ransomware was found to be injected into legitimate processes, and in some instances, the attackers dropped it as a *.log file. Rapture appends six characters to encrypted files and requires specific command lines for proper execution.
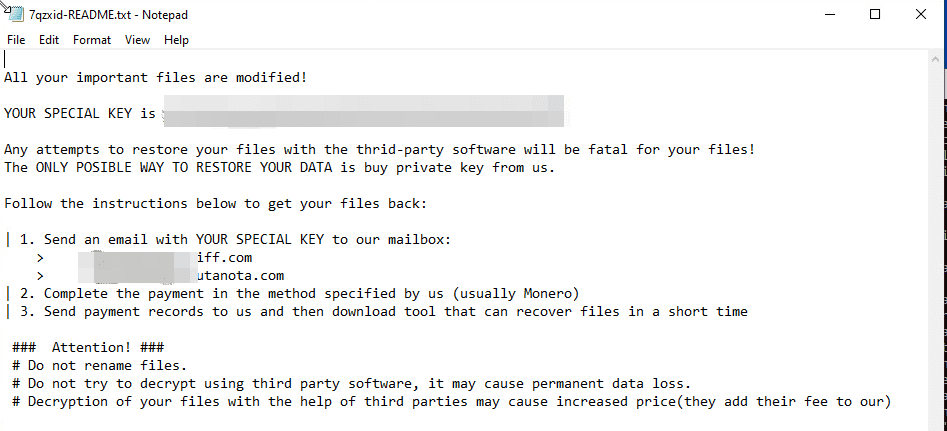
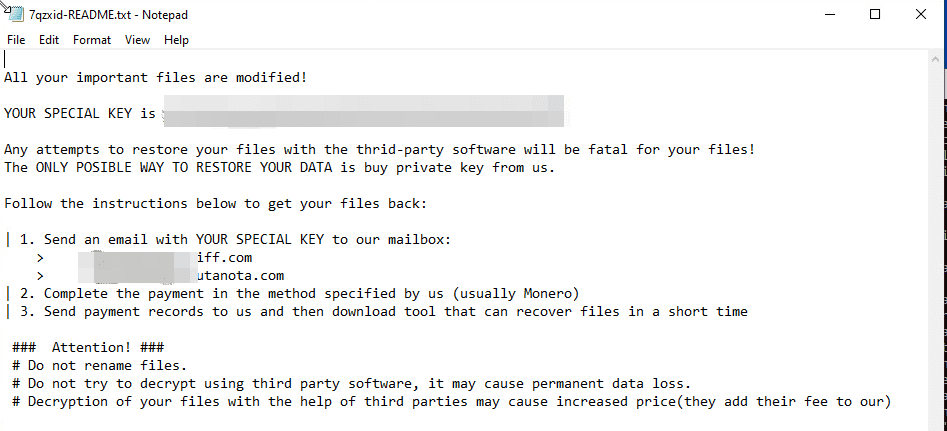
The ransom note dropped by Rapture bears a resemblance to the Zeppelin ransomware, although no other connections between the two have been identified. The researchers discovered that Rapture has been active for some time, but no samples were available during its initial emergence.
The infection chain spans three to five days, starting with the attackers inspecting firewall policies, checking the PowerShell version, and searching for vulnerable Log4J applets. They then download and execute a PowerShell script to install a Cobalt Strike beacon in the target’s system.
The attackers gain access to the victim’s network, likely through vulnerable public-facing websites and servers. They then employ a unique method of obtaining higher privileges to execute the payload by injecting malicious activity into an existing svchost.exe process. This process then executes explorer.exe using the /NOUACCHECK command, which allows explorer.exe to drop and execute the second-stage Cobalt Strike beacon downloader.
The second-stage downloader connects to an address to download the main Cobalt Strike beacon. The beacon then attempts to connect to another subfolder on the same command-and-control (C&C) server to receive the backdoor command and other payloads. The response from the C&C server is sandwiched in another JavaScript code, which the beacon decodes.
The researchers found that the beacon performed ransomware activities in the majority of the affected systems, indicating that the code is downloaded and executed in memory. Further investigation of the Cobalt Strike beacon’s watermark revealed that it is likely that Rapture’s operators are using a pirated Windows license, which is also being used by several other threat actors.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
