reportly: AzureAD user activity report tool
reportly
Reportly is an AzureAD user activity report tool.
This is a tool that will help blue teams during a cloud incident. When running the tool, the researcher will enter as input a suspicious user and a time frame and will receive a report detailing the following:
- Information about the user
- Actions are taken by the user
- Actions are taken on the user
- User login and failure logs
Installation
Clone the repo:
git clone https://github.com/sap8899/reportly.git
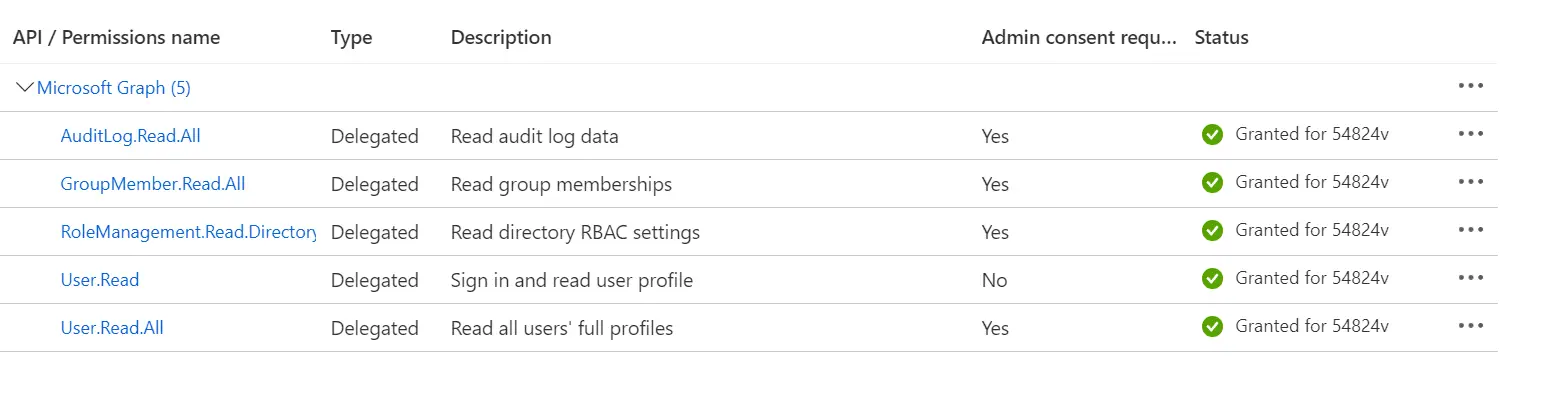
In order to use the tool you will need an AzureAD application with the following delegated Microsoft graph api permissions:
- AuditLog.Read.All
- GroupMember.Read.All
- RoleManagement.Read.Directory
- User.Read
- User.Read.Alldont forget to grant admin consent
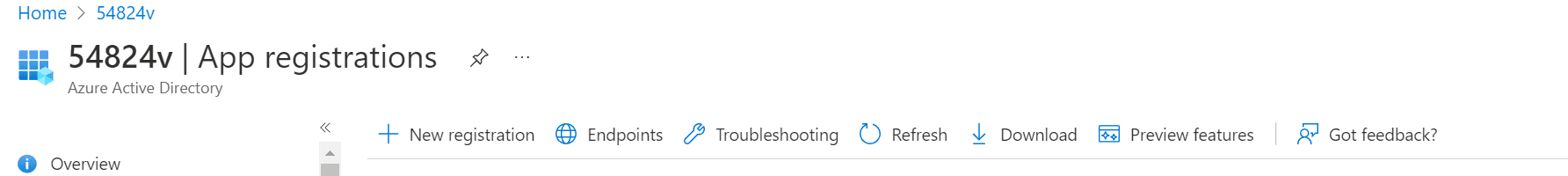
To create an application go to the “App registration” tab and select the “New registration” option.
Also, when creating the application, make sure you mark the following option as “yes”: 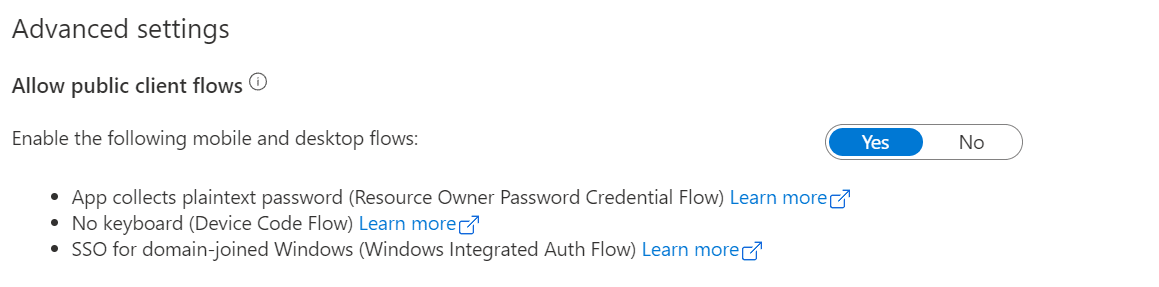
- you can find this property under the application’s “Authentication” tab.
Add a secret to the application. 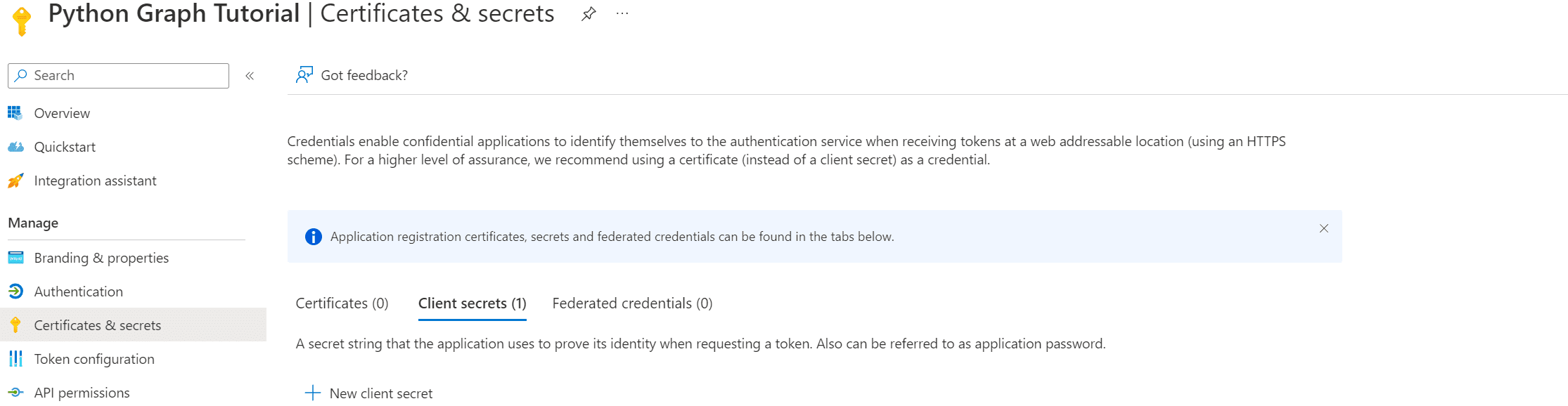
- Go to “Certificates & secrets”
- Add a secret
- Immediately copy the secret to the config file (after you watch it once, it disappears)
After you created the application you need to fill in the config.cfg file:
clientId = application id
clientSecret = application secret
tenantId = tenant id
Usage
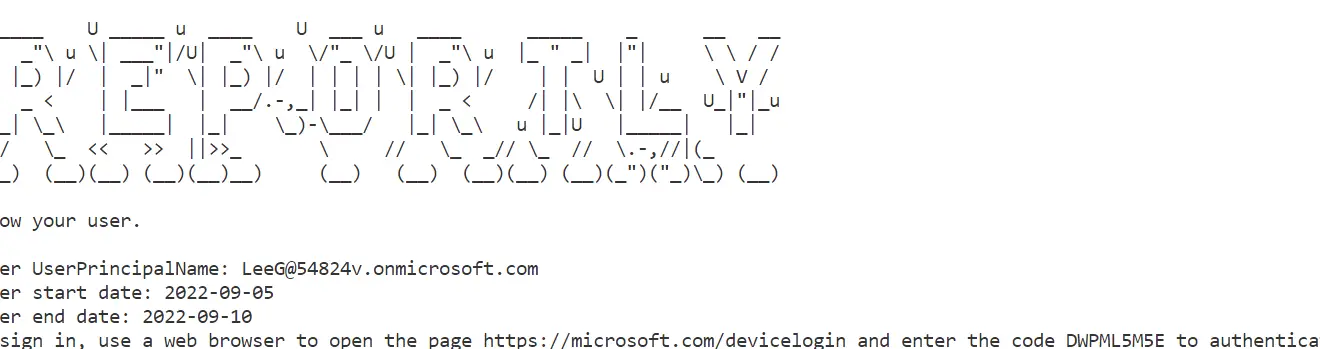
When running the tool, a link to authentication and a device code will show, follow the link and enter the code to authenticate.
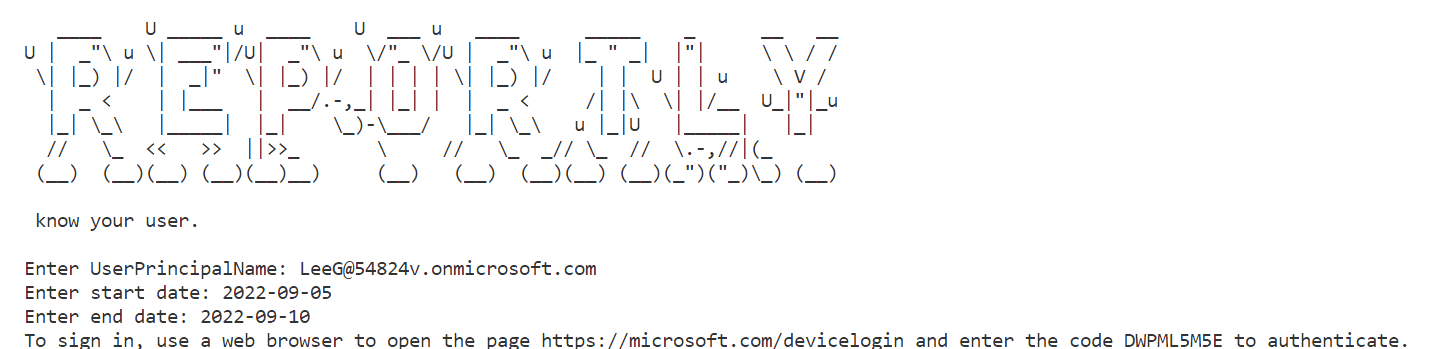
Insert the User principal name of a suspicious user.
Insert start and end times in the following format: 2022-11-16
I recommend a range of no longer than a week.
After authentication, in order to create a full report choose option “5”
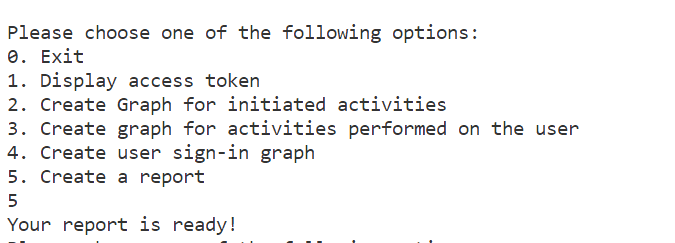
When the report will be ready the tool will print “Your report is ready!”. The reports are created in the executable’s directory.
Source: https://github.com/sap8899/






