Researcher Releases Open-Source Scanner for CVE-2024-47176 CUPS Vulnerability
Renowned security researcher Marcus Hutchins has unveiled a new open-source tool designed to help administrators and security professionals identify vulnerable instances of the Common Unix Printing System (CUPS), which is widely used across UNIX and UNIX-like systems. This tool is crucial for detecting systems that could be exploited due to a newly discovered chain of vulnerabilities in CUPS, potentially leading to remote code execution (RCE).
CUPS is a fundamental component in many UNIX-based environments, managing network printing and providing a robust framework for printing tasks. Its widespread use on Linux and even some Apple devices makes it a prime target for exploitation. Recently, a series of critical vulnerabilities—CVE-2024-47176, CVE-2024-47076, CVE-2024-47175, and CVE-2024-47177—have been discovered in CUPS, allowing attackers to remotely add or reconfigure network printers and execute arbitrary code on vulnerable systems.
At the core of this vulnerability chain is CVE-2024-47176, a critical flaw in the cups-browsed daemon. This flaw arises from the fact that cups-browsed binds its control port (UDP port 631) to all available network interfaces, including external ones, through INADDR_ANY. Worse, this service does not authenticate incoming requests, meaning that any attacker capable of reaching this port can exploit the vulnerability.
In essence, the flaw allows an attacker to trick cups-browsed into reaching out to a malicious server, starting a process that can result in complete system compromise. This is particularly dangerous because the vulnerability is exploitable both remotely and via local networks, potentially allowing lateral movement within an organization.
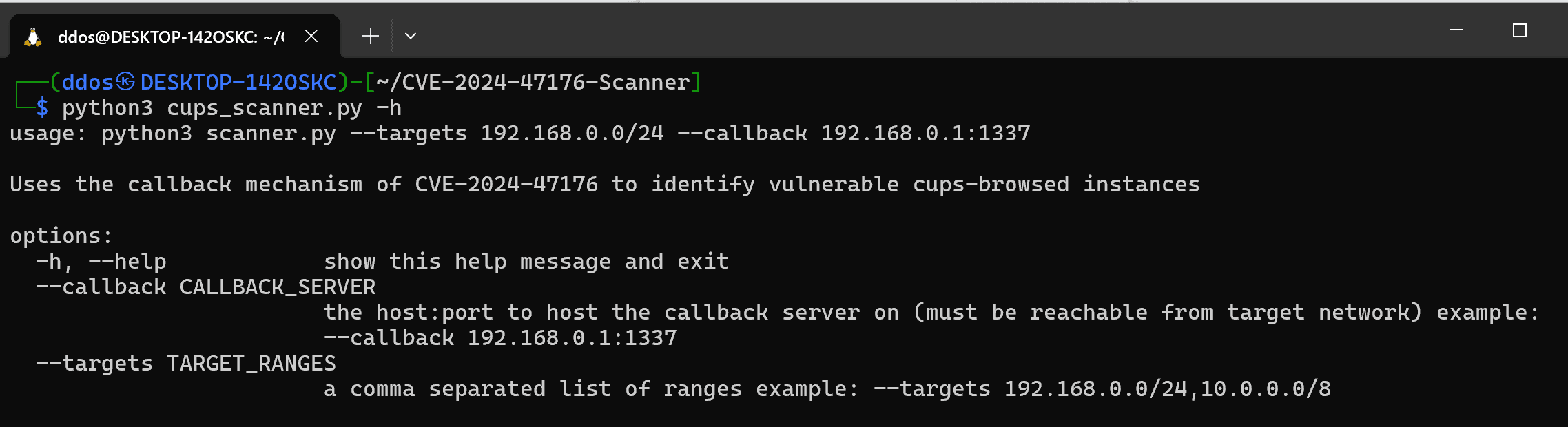
Recognizing the severity of these vulnerabilities, Marcus Hutchins has released cups_scanner.py, a Python-based tool designed to automate the process of scanning local networks for vulnerable cups-browsed instances. The tool simplifies the complex process of manually detecting vulnerable devices by performing the following actions:
- Set up a basic HTTP server (no need to identify as a printer, since we will not be exploiting the RCE vulnerability).
- Craft a UDP packet which will instruct cups-browsed to connect to our HTTP server.
- Send the UDP packet to every IP in a give range on port 631.
- Log any POST requests to the
/printers/endpoint, which are triggered by vulnerable cups-browsed instances.
The vulnerabilities in CUPS are a ticking time bomb, particularly CVE-2024-47176, which could allow attackers to gain a foothold within an organization’s network. Because the cups-browsed service is so commonly exposed to local networks, administrators must scan for and patch any vulnerable instances immediately.





