RMIScout
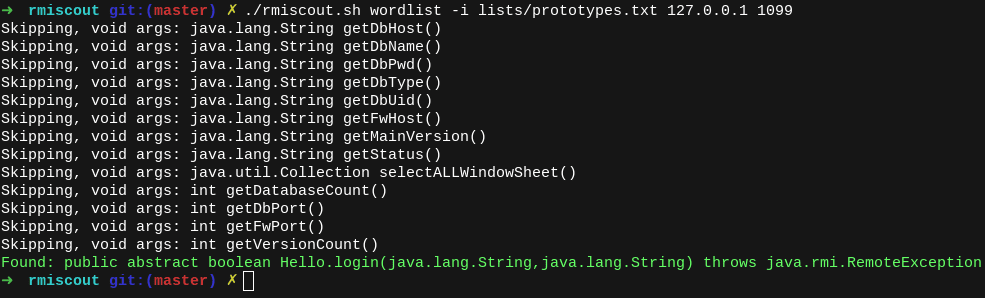
RMIScout performs wordlist and bruteforce attacks against exposed Java RMI interfaces to safely guess method signatures without invocation.
On misconfigured servers, any known RMI signature using non-primitive types (e.g., java.lang.String), can be exploited by replacing the object with a serialized payload. This is a fairly common misconfiguration (e.g., VMWare vSphere Data Protection + vRealize Operations Manager, Pivotal tc Server, and Gemfire, Apache Karaf + Cassandra) as highlighted in An Trinh’s 2019 Blackhat EU talk.
RMIScout integrates with ysoserial and GadgetProbe to perform deserialization attacks against services incorrectly configuring process-wide serialization filters (JEP 290).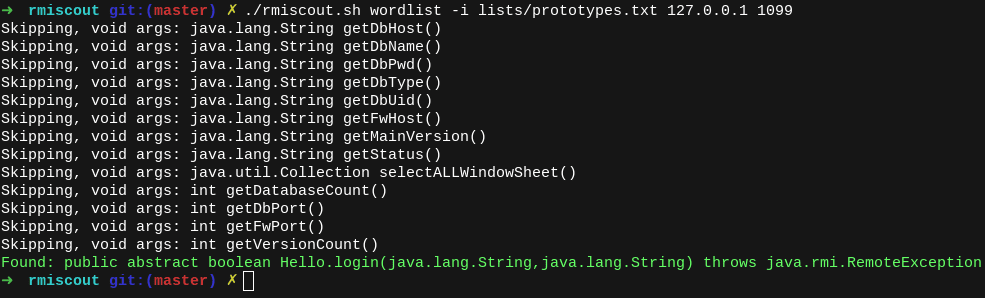
Motivation
I wanted a tool to do the following tasks:
- Provide wordlist and text-based bruteforce strategies instead of bruteforcing a 64-bit method hash.
- Identify RMI methods without invoking them.
- Provide a simple way to exploit the known issue of unsafe RMI parameter unmarshalling and integrate with ysoserial or payloads implementing ysoserial.payloads.ObjectPayload.
- Integrate GadgetProbe to identify remote classes to help identify relevant software and construct gadget chains.
To start off your search, the included lists/prototypes.txt wordlist is a deduplicated wordlist from 15,000 RMI prototypes found in OSS projects across GitHub. Feel free to submit a PR to include more 🙂
How it works
To identify but not execute RMI functions, RMIScout uses low-level RMI network functions and dynamic class generation to send RMI invocations with deliberately mismatched types to trigger remote exceptions. All parameters are substituted for a dynamically generated serializable class with a 255-character name assumed to not exist in the remote classpath. For example:
Remote Interface:
void login(String user, String password)
RMIScout will invoke:
login((String) new QQkzkn3..255 chars..(), (String) new QQkzkn3..255 chars..())
If the class is present this will result in a remote java.rmi.UnmarshalException cased by the ClassNotFoundException or argument unmarshalling error without invoking the underlying method.
Changelog v1.4
- Added RMI-IIOP support
- Added invoke mode
- Added automatic protocol selection for RMI-JRMP, activation stubs, and SSL
- Added automatic localhost bypass technique
- Added multi-protocol Docker demo
- More helpful error messages
- Various bug fixes
Use
Download
Copyright (c) 2020 BishopFox
Source: https://github.com/BishopFox/