S3 Account Search: find the account id an S3 bucket
S3 Account Search
This tool lets you find the account id an S3 bucket belongs to.
For this to work you need to have at least one of these permissions:
- Permission to download a known file from the bucket (s3:getObject).
- Permission to list the contents of the bucket (s3:ListBucket).
Additionally, you will need a role that you can assume with (one of) these permissions on the bucket you’re examining
Some more background can be found on the Cloudar Blog
How this works
There is an IAM policy condition s3:ResourceAccount, that is meant to be used to give access to S3 in specified (set of) account(s), but also supports wildcards. By constructing the right patterns, and seeing which ones will lead to a Deny or an Allow, we can determine the account id by discovering it one digit at a time.
- We verify that we can access the object or bucket with the provided role
- We assume the same role again, but this time add a policy that restricts our access to S3 buckets that exist in an account starting with 0. If our access is allowed we know that the account id has to start with
0. If the request is denied, we try again with 1 as the first digit. We keep incrementing until our request is allowed, and we find the first digit - We repeat this process for every digit. Using the already discovered digits as a prefix. E.g. if the first digit was 8, we test account ids starting with 80, 81, 82, etc.
Install
pipx install s3-account-search
pip install s3-account-search
Use
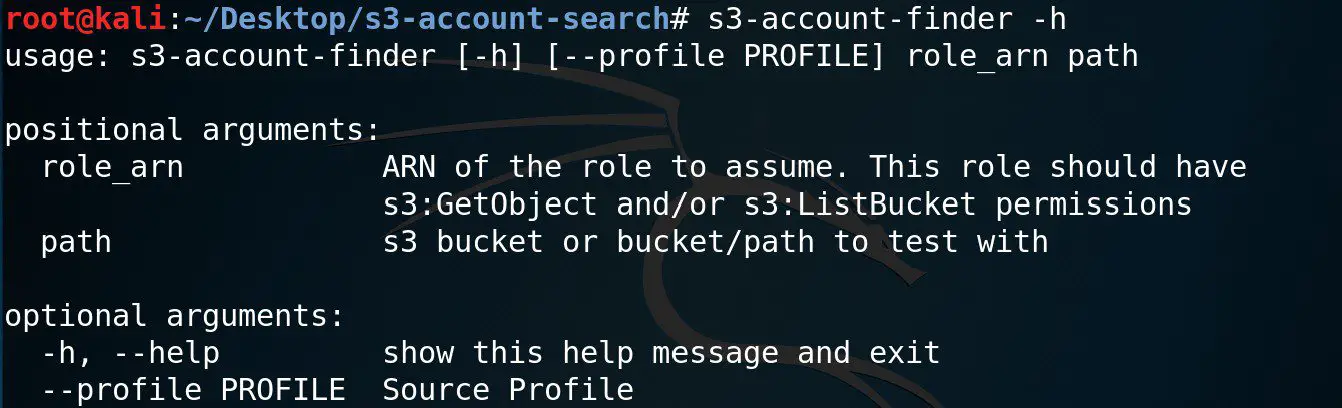
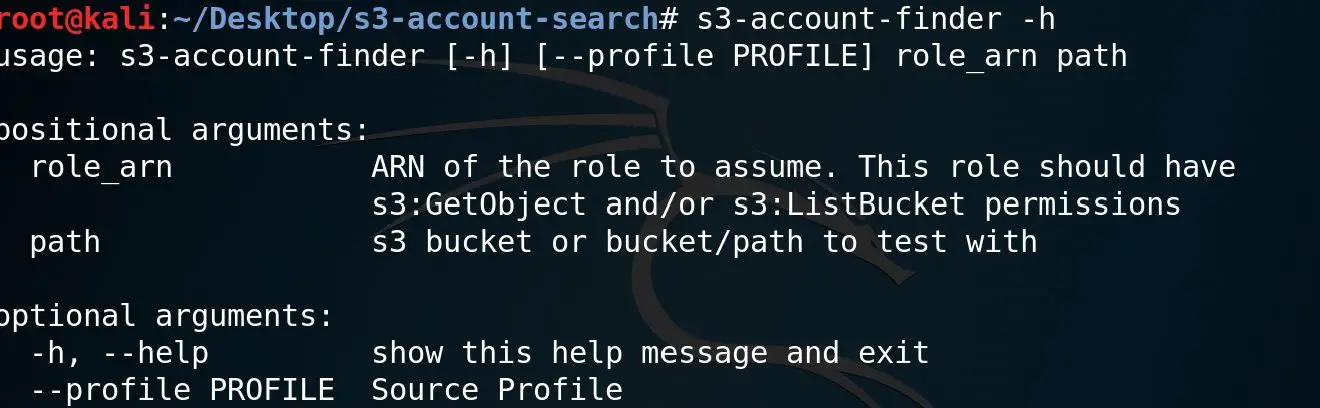
Example:
# with a bucket
s3-account-finder arn:aws:iam::123456789012:role/s3_read s3://my-bucket
# with an object
s3-account-finder arn:aws:iam::123456789012:role/s3_read s3://my-bucket/path/to/object.ext
# You can also leave out the s3://
s3-account-finder arn:aws:iam::123456789012:role/s3_read my-bucket
# Or start from a specified source profile
s3-account-finder –profile source_profile arn:aws:iam::123456789012:role/s3_read s3://my-bucket
Copyright (c) 2021 Cloudar
Source: https://github.com/WeAreCloudar/