saferwall v0.5 releases: Collaborative and Streamlined Threat Analysis at Scale
saferwall – Collaborative and Streamlined Threat Analysis at Scale
Saferwall allows you to analyze, triage, and classify threats in just minutes.
⭐ Collaborative – Built for security teams and researchers to streamline analysis, identification, and sharing of malware samples.
☁️ Fast & cloud-native – Scalable and cloud-native by design, deploy in minutes to bare metal or in the cloud.
⚡ Save time – Automate cumbersome tasks, generate IoC’s and reports with zero friction.
📦 Batteries included – All your favorite tools included, build intelligence feeds for hunting threats or generating signatures.
❤️ Open source first – We are open-source, developer-friendly, and user driven.
Batteries Included
-
Static Analysis:
- File metadata, packer identification and crypto hashes.
- String (ASCII/Unicode and ASM) extraction.
- PE (Portable Executable) file parser.
- ELF (Executable Linkable Format) file parser.
-
Dynamic Analysis:
- Automated Malware Analysis using a Hypervisor based VM.
- Intercepting OS System Calls to build an exeuction trace of executable files.
- Generate detailed reports and gain insight into malware behavior.
- Choose which API’s to trace, grab screenshots and file changes aswell as memory dumps.
-
Multiple AV scanner supporting major vendors:
Vendors status Vendors status Avast ✔️ FSecure ✔️ Avira ✔️ Kaspersky ✔️ Bitdefender ✔️ McAfee ✔️ ClamAV ✔️ Sophos ✔️ Comodo ✔️ Symantec ✔️ ESET ✔️ Windows Defender ✔️ TrendMicro ✔️ DrWeb ✔️ -
Integrations with your own data processing pipeline.
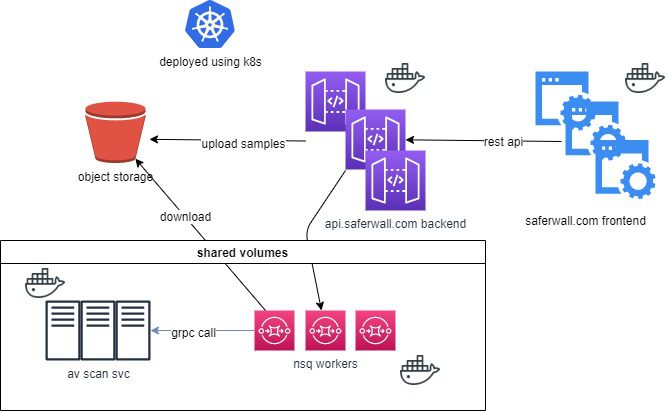
Current architecture / Workflow:
Here is a basic workflow which happens during a file scan:
- Frontend talks to the backend via REST APIs.
- Backend uploads samples to the object storage.
- Backend pushes a message into the scanning queue.
- Consumer fetches the file and copy it into to the nfs share avoiding to pull the sample on every container.
- Consumer calls asynchronously scanning services (like AV scanners) via gRPC calls and waits for results.
Changelog v0.5
- fix(github workflow) depcreated set-output and docker/build-push-action by @LordNoteworthy in #412
- feat (services) post-processor to include first_seen when it’s absent by @LordNoteworthy in #413
- feat: add loki-stack chart for log aggregation by @LordNoteworthy in #414
- fix(storage): guarantee sequential write in s3 download by @LordNoteworthy in #415
- fix: Set the nsq config maxInFlight to the same # of goroutines by @LordNoteworthy in #416
- fix(services): increase multi-av scan timeout and nsq msg timeout by @LordNoteworthy in #417
- doc: add documentation how to use compose to develop in the codebase by @LordNoteworthy in #418
- feat: make pulling image contrainers more generic from private registries by @LordNoteworthy in #419
- feat: externalize multi-av scan timeout by @LordNoteworthy in #420
- helm: populate multiav default values for scanTimeout and logLevel by @LordNoteworthy in #421
- feat: change multiav scan timeout from an int (seconds) to duration (string) by @LordNoteworthy in #427
- chore(helm): fix _helpers template by @LordNoteworthy in #428
- chore(helm): default values for new config entries in web apis by @LordNoteworthy in #429
- fix(services): set the status for task progress by @LordNoteworthy in #431
- fix(helm): webapis extra cors origins + new UI by @LordNoteworthy in #432
- fix: update compose to match new UI env vars & bump go to v1.18 by @LordNoteworthy in #433
- feat: Create a summary of behavior activities in sandbox by @LordNoteworthy in #435
- chore(deps): bump google.golang.org/grpc from 1.52.0 to 1.53.0 by @dependabot in #437
- feat(sandbox): append process ID to system events and make events an array instead of an object by @LordNoteworthy in #438
- feat(sandbox): scanning artifacs with Yara by @LordNoteworthy in #439
- feat(sandbox): store process tree data by @LordNoteworthy in #441
- increase gRPC msg size + fix timeout fmt + artifacts length by @LordNoteworthy in #442
- feat: store big byte* API parameters to object storage by @LordNoteworthy in #443
Installation
Copyright (C) 2018 saferwall







