ScanCannon: The speed of masscan with the reliability and detailed enumeration of nmap
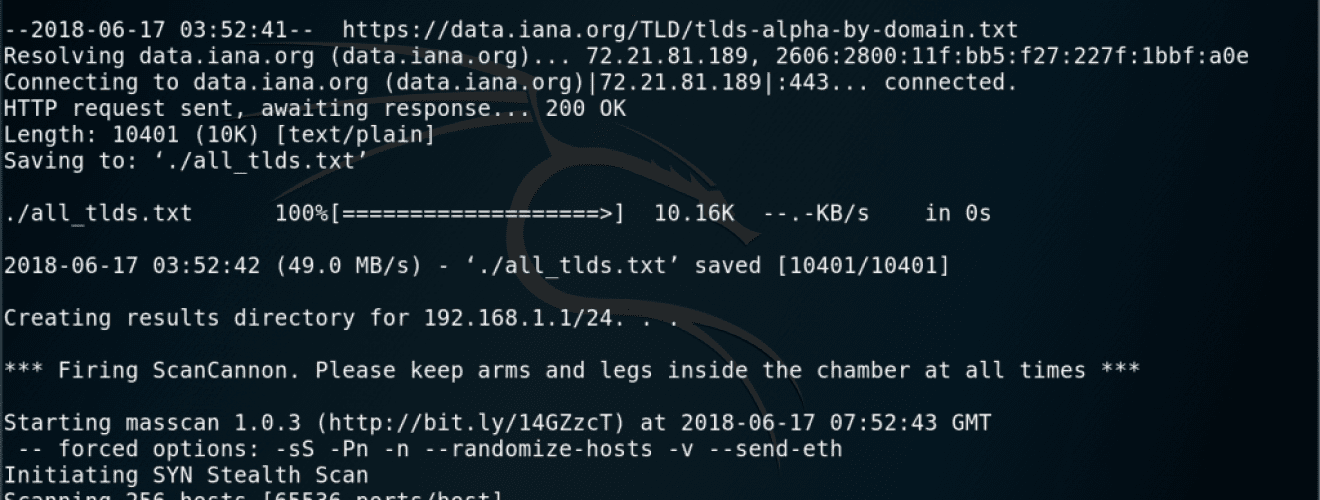
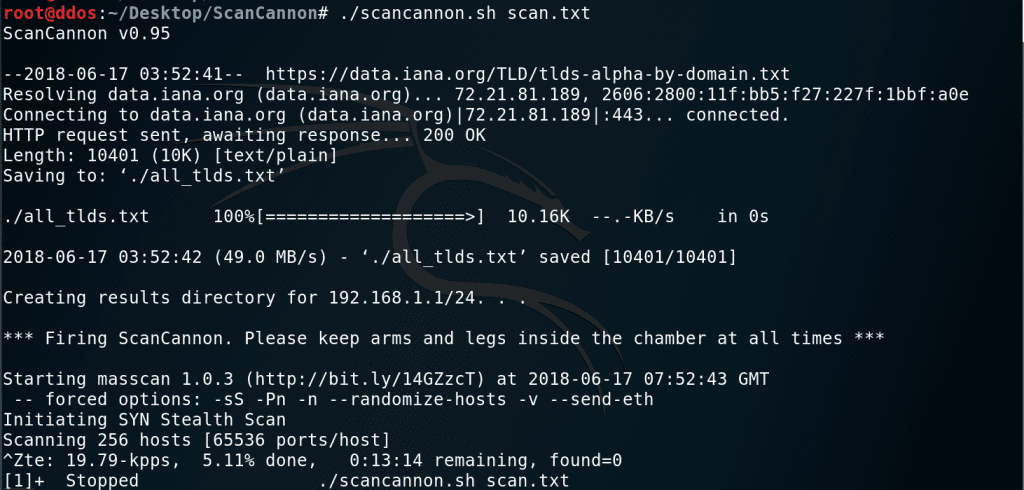
ScanCannon v0.95
The speed of masscan with the reliability and detailed enumeration of nmap!
Handles the enumeration of large networks, including banner grabbing & OS/service version guessing at high speed. Uses masscan to quickly identify open ports, then calls nmap to gain details on the systems/services listening on those ports. Data is stored in both masscan & nmap standard outputs, as well as a few other greppable intermediary files that include identified domains & subdomains, all nicely organized into per-network directories to make your boss think you know what you’re doing.
CHANGELOG FOR v0.95:
- Fixed issue with some final catalogue files being generated
- Now moves nma *.xml files to their own directory to more easily suck them into other tools
TO-DO:
- Root domain detection for International TLDs (Such as .co.uk) doesn’t work too well due to InterNIC, etc not complying with ARIN standards. Need to fix this.
- Add arguments for Masscan & nmap speeds
- Tarpit detection
Download
Requirement
- GNU Utilities
- Masscan v1.0.3+
- nmap v7.0.1+
- Root \ sudo privs (for TCP fingerprinting)
git clone https://github.com/johnnyxmas/ScanCannon.git
Usage:
$ scancannon.sh [file . . .]
A file contains a line-separated list of CIDR networks, i.e.:
Masscan & nmap arguments can be modified within the script.
WARNING:
It is VERY FEASIBLE to execute a Denial of Service against the target networks, even when launching from a single source. You should start with a very low masscan max-rate (5,000-10,000 kbps) and increase slowly to test. On bare metal, pushing beyond 20,000 seems to increase the chances of missing responses from the target. 40,000 kbps has been known to DoS ESXi virtual switches (even on the source). ~200,000 is often enough to take out ISP equipment.
Similar warnings exist for nmap, though it is much less dangerous. Some older or over-utilized LANs may hiccup with a Timing of T4 or T5, but this is rare.
Source: https://github.com/johnnyxmas/





