SharpEDRChecker v1.2 PRE releases: Checks running processes, process metadata, Dlls
SharpEDRChecker
New and improved C# Implementation of Invoke-EDRChecker. Checks running processes, process metadata, Dlls loaded into your current process and each DLLs metadata, common install directories, installed services and each service binaries metadata, installed drivers and each drivers metadata, all for the presence of known defensive products such as AV’s, EDR’s and logging tools. Catches hidden EDRs as well via its metadata checks, more info in a blog post coming soon.
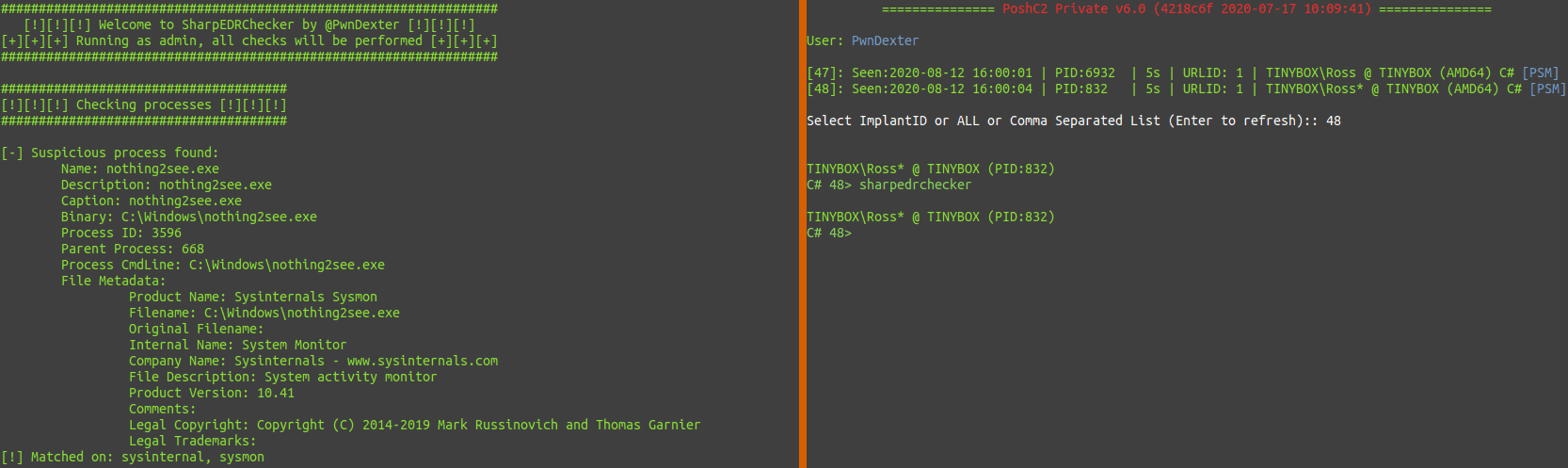
This binary can be loaded into your C2 server by loading the module then running it. Note: this binary is now included in PoshC2 so no need to manually add it.
I will continue to add and improve the list when time permits. A full roadmap can be found below.
Roadmap
- – Add more EDR Products – never-ending
- – Test across more Windows and .NET versions
- – Add remote host query capability
- – Port to Python for Unix/macOS support
Use
Once the binary has been loaded onto your host or into your C2 of choice, you can use the following commands:
Run the binary against the local host and perform checks based on current user integrity:
.\SharpEDRChecker.exe run-exe SharpEDRChecker.Program SharpEDRChecker
For use in PoshC2 is the following:
sharpedrchecker
Example
Initial start down C2:
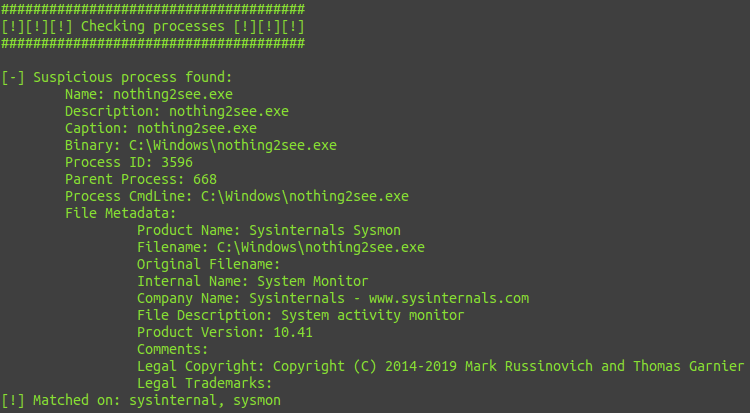
Processes:
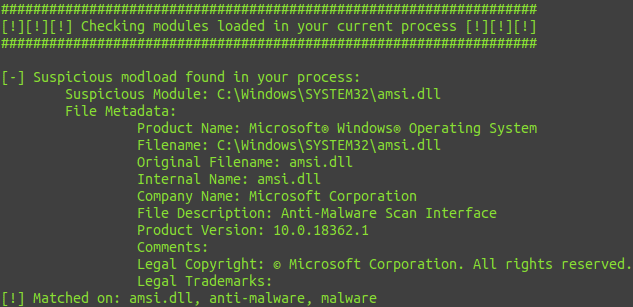
Modloads in your process:
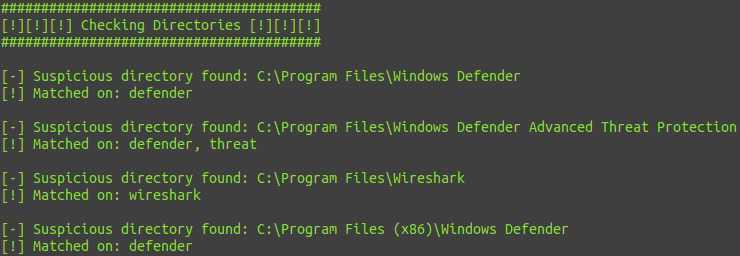
Directories:
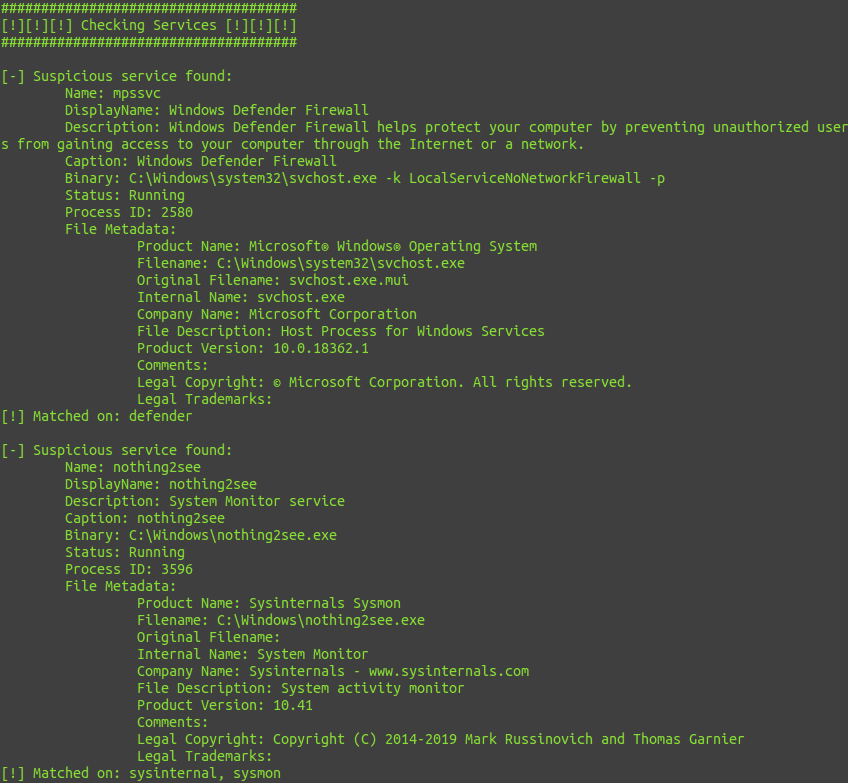
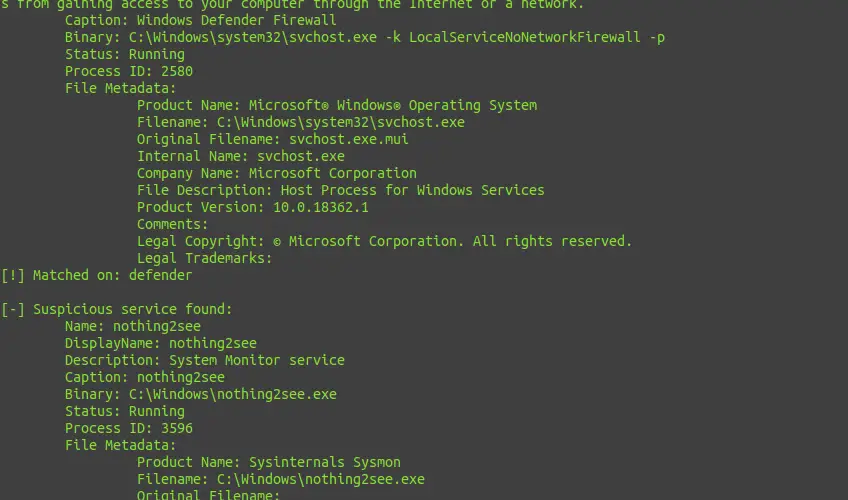
Services:
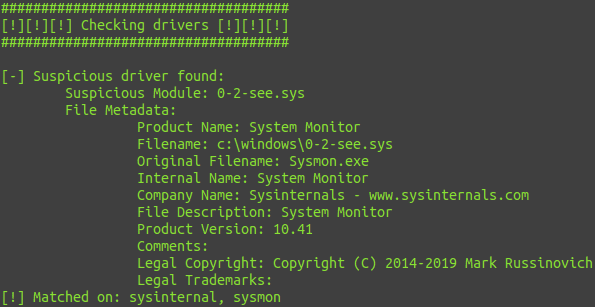
Drivers:
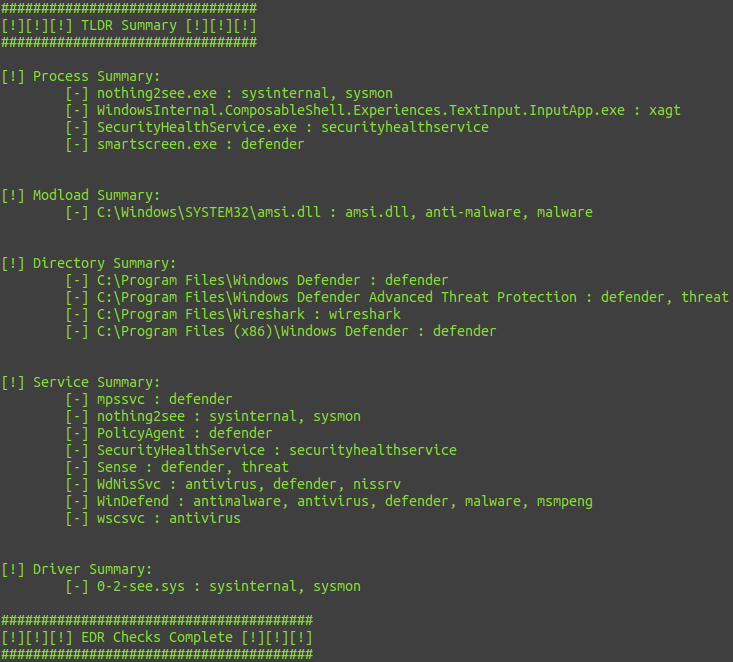
TLDR Summary:
Changelog v1.2 PRE
Added a bunch more EDR products, vendors etc seen as it has been to long since the project got an update, stay tuned for more to come!
Download
Copyright (c) 2020, Ross