slicer: automate the boring process of APK recon

Slicer
A tool to automate the recon process on an APK file.
Slicer accepts a path to an extracted APK file and then returns all the activities, receivers, and services which are exported and have null permissions and can be externally provoked.
Note: The APK has to be extracted via jadx or apktool.
Features
-
Check if the APK has set the android:allowbackup to true
-
Check if the APK has set the android:debuggable to true.
-
Return all the activities, services, and broadcast receivers which are exported and have null permission set. This is decided on the basis of two things:
- android:exporte=true is present in any of the component and have no permission set.
- If exported is not mention then slicer check if any Intent-filters are defined for that component, if yes that means that component is exported by default(This is the rule given in android documentation.)
-
Check the Firebase URL of the APK by testing it for .json trick.
- If the firebase URL is myapp.firebaseio.com then it will check if https://myapp.firebaseio.com/.json returns something or gives permission denied.
- If this thing is open then that can be reported as high severity.
-
Check if the google API keys are publically accessible or not.
- This can be reported on some bounty programs but have a low severity.
- But most of the time reporting this kind of thing will bring out the pain of Duplicate.
- Also sometimes the company can just close it as not applicable and will claim that the KEY has a usage cap – r/suspiciouslyspecific 😉
-
Return other API keys that are present in strings.xml and in AndroidManifest.xml
-
List all the file names present in /res/raw and res/xml directory.
-
Extracts all the URLs and paths.
- These can be used with tool like dirsearch or ffuf.
Download
git clone https://github.com/mzfr/slicer
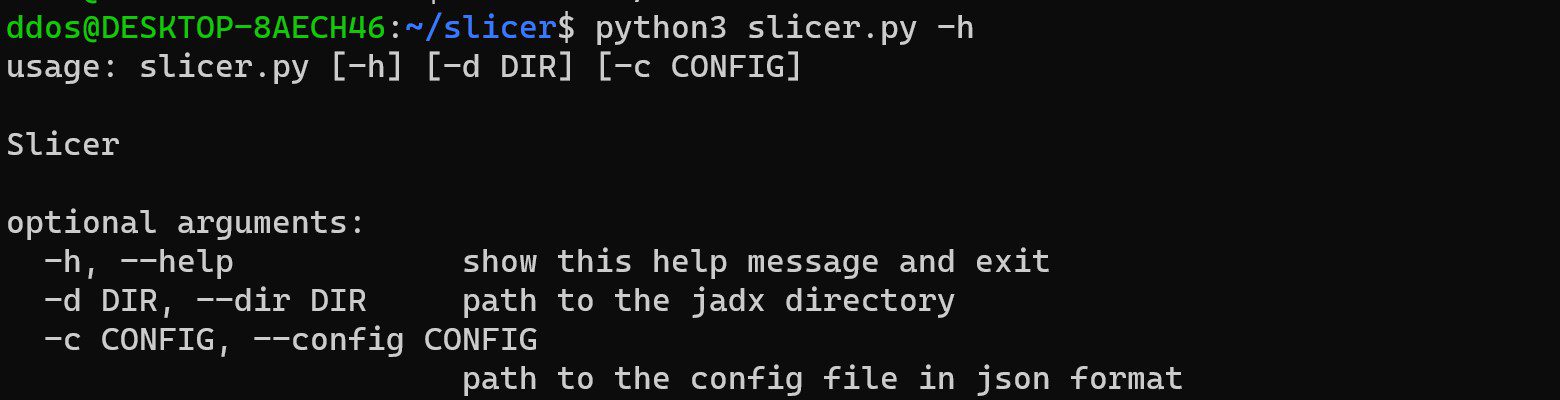
Use
Copyright (C) 2020 Mehtab Zafar
Source: https://github.com/mzfr/






