sslsplit v0.5.5 releases: Transparent SSL/TLS interception
SSLsplit – transparent SSL/TLS interception
Overview
SSLsplit is a tool for man-in-the-middle attacks against SSL/TLS encrypted network connections. It is intended to be useful for network forensics, application security analysis, and penetration testing.
SSLsplit is designed to transparently terminate connections that are redirected to it using a network address translation engine. It then terminates SSL/TLS and initiates a new SSL/TLS connection to the original destination address, while logging all data transmitted. Besides NAT-based operation, it also supports static destinations and using the server name indicated by SNI as the upstream destination. SSLsplit is purely a transparent proxy and cannot act as an HTTP or SOCKS proxy configured in a browser.
SSLsplit supports plain TCP, plain SSL, HTTP and HTTPS connections over both IPv4 and IPv6. It also has the ability to dynamically upgrade plain TCP to SSL in order to generically support SMTP STARTTLS and similar upgrade mechanisms. It fully supports Server Name Indication (SNI) and is able to work with RSA, DSA, and ECDSA keys and DHE and ECDHE cipher suites. Depending on the version of OpenSSL built against, SSLsplit supports SSL 3.0, TLS 1.0, TLS 1.1 and TLS 1.2, and optionally SSL 2.0 as well.
For SSL and HTTPS connections, SSLsplit generates and signs forged X509v3 certificates on-the-fly, mimicking the original server certificate’s subject DN, subjectAltName extension, and other characteristics. It has the ability to use existing certificates of which the private key is available, instead of generating forged ones. It supports NULL-prefix CN certificates but otherwise does not implement exploits against specific certificate verification vulnerabilities in SSL/TLS stacks.
SSLsplit implements a number of defences against mechanisms which would normally prevent MitM attacks or make them more difficult. SSLsplit can deny OCSP requests in a generic way. For HTTP and HTTPS connections, SSLsplit mangles headers to prevent server-instructed public key pinning (HPKP), avoid strict transport security restrictions (HSTS), avoid Certificate Transparency enforcement (Expect-CT) and prevent switching to QUIC/SPDY, HTTP/2 or WebSockets (Upgrade, Alternate Protocols). HTTP compression, encodings and keep-alive are disabled to make the logs more readable.
Logging options include traditional SSLsplit connect and content log files as well as PCAP files and mirroring decrypted traffic to a network interface. Additionally, certificates, master secrets and local process information can be logged.
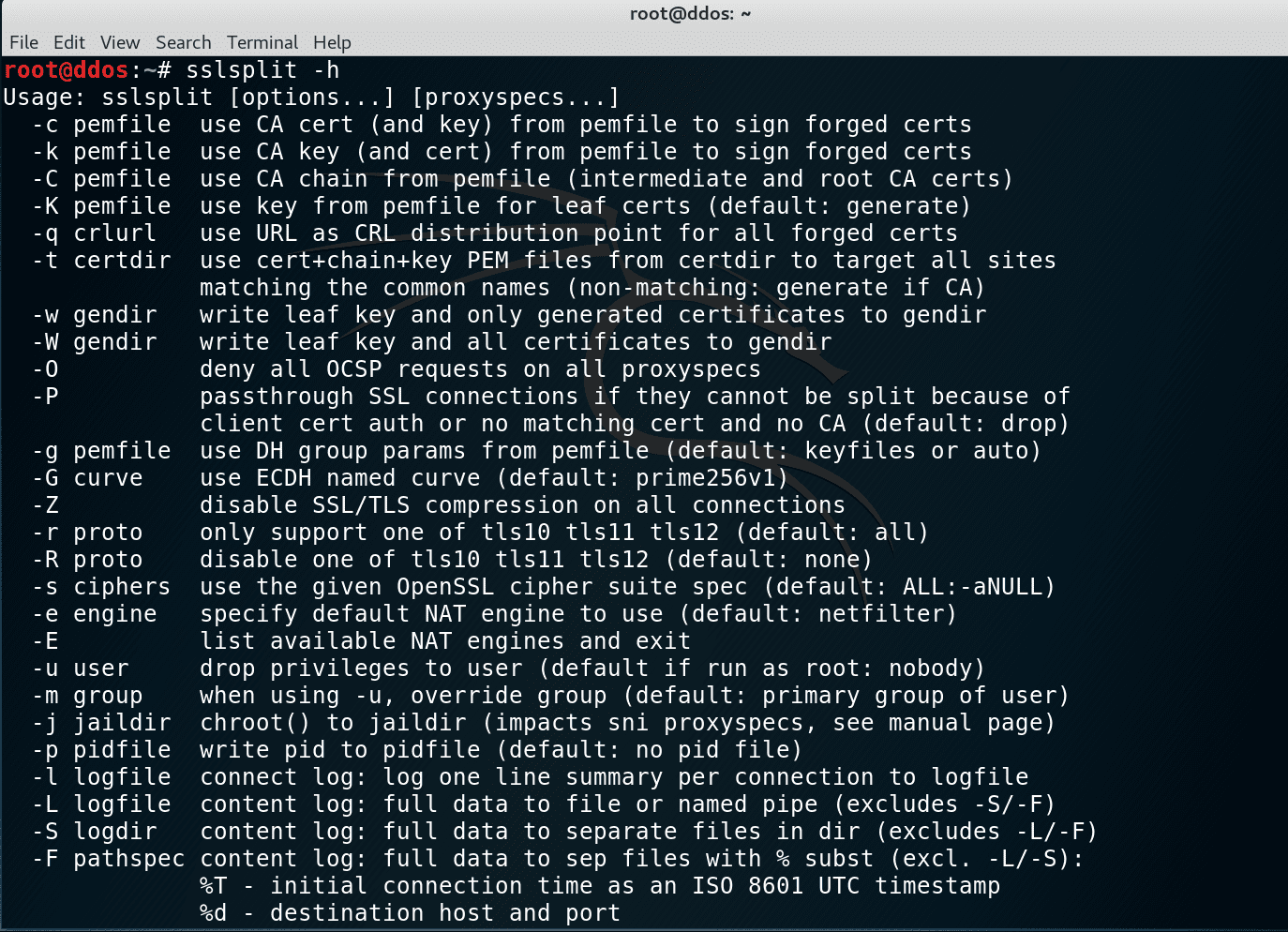
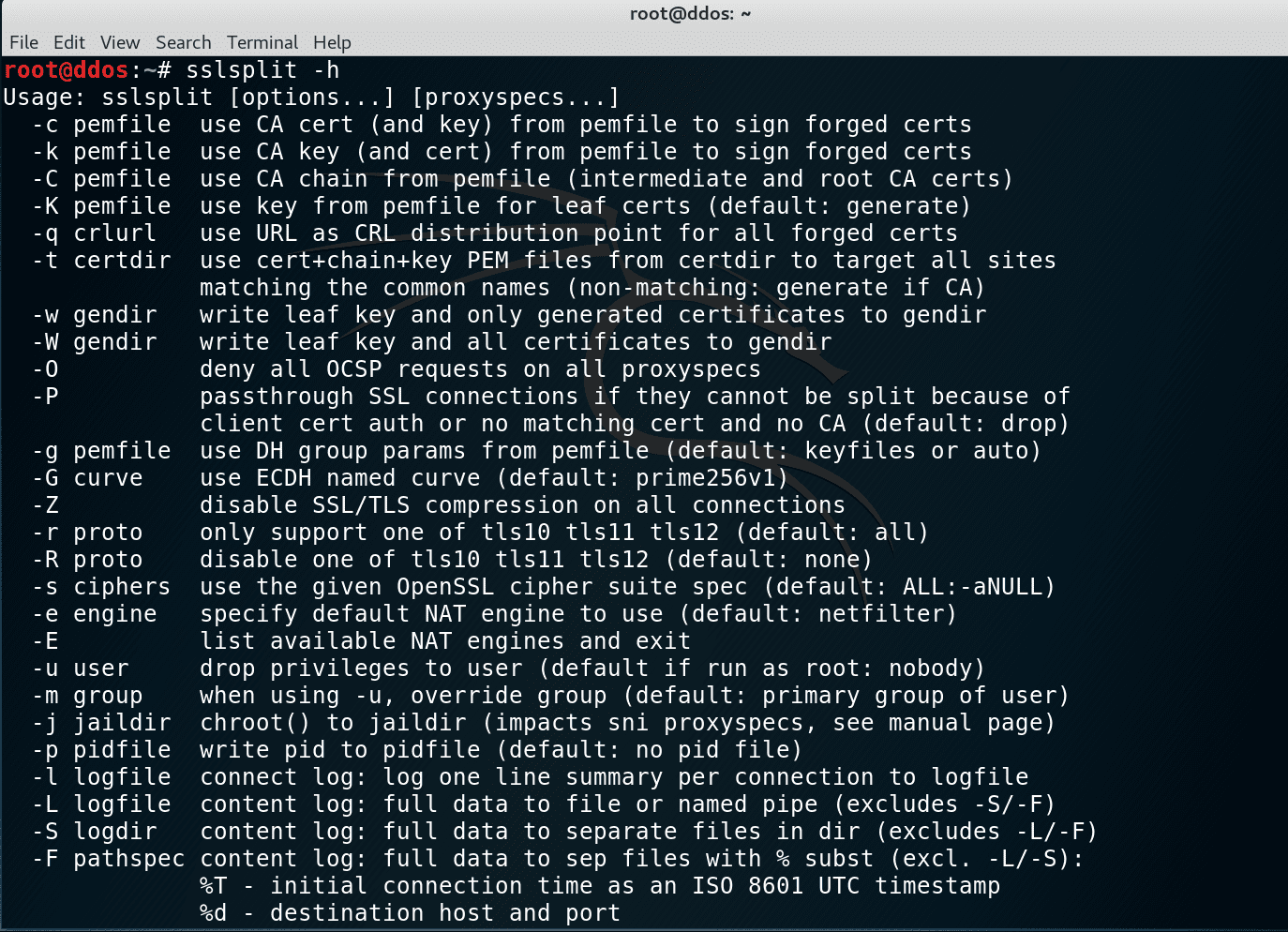
See the manual page sslsplit(1) for details on using SSLsplit and setting up the various NAT engines.
Changelog
SSLsplit 0.5.5 2019-08-30
- Add -A option for specifying a default leaf certificate instead of generating it on the fly (issue #139).
- Rename the following config file options for clarity and consistency:
- LeafCerts to LeafKey
- TargetCertDir to LeafCertDir
- CRL to LeafCRLURL The old syntax is still accepted for backwards compatibility.
- Increase the default RSA leaf key size to 2048 bits and force an OpenSSL security level of 0 in order to maximize interoperability in the default configuration. OpenSSL with a security level of 2 or higher was rejecting our old default leaf key size of 1024 bits (issue #248).
- Propagate the exit status of the privsep child process to the parent process and use 128+signal convention (issue #252).
- Fix unexpected connection termination for certificates without a subject common name.
- Fix TCP ports in packet mirroring mode (issue #247).
- Fix certificate loading with LibreSSL 2.9.2 and later.
- Fix MANDIR make variable semantics to GNU standards and introduce BINDIR and SYSCONFDIR in order to allow better control over where files are installed by the install target (pull request #255 by @arkamar and follow-up work). Also fixes the sample config file to be installed to $(SYSCONFDIR)/sslsplit/ instead of $(PREFIX)/sslsplit/ by default.
- No longer create /var/log/sslsplit and /var/run/sslsplit directories as part of
make install(issue #251). - Add XNU headers for macOS Mojave 10.14.1 to 10.14.3.
- Minor bugfixes and improvements.
Install
git clone https://github.com/droe/sslsplit.git make make test # optional unit tests make sudotest # optional unit tests requiring privileges make install # optional install
Copyright (c) 2009-2019, Daniel Roethlisberger and contributors.
All rights reserved.





