sslyze v6.0 releases: Fast and powerful SSL/TLS server scanning library
SSLyze
Fast and powerful SSL/TLS server scanning library for Python 2.7 and 3.4+.
Description
SSLyze is a Python library and a CLI tool that can analyze the SSL configuration of a server by connecting to it. It is designed to be fast and comprehensive and should help organizations and testers identify misconfigurations affecting their SSL/TLS servers.
Key features include:
- Fully documented Python API, in order to run scans and process the results directly from Python.
- New: Support for TLS 1.3 (draft 18) and the ROBOT vulnerability.
- Scans are automatically dispatched among multiple processes, making them very fast.
- Performance testing: session resumption and TLS tickets support.
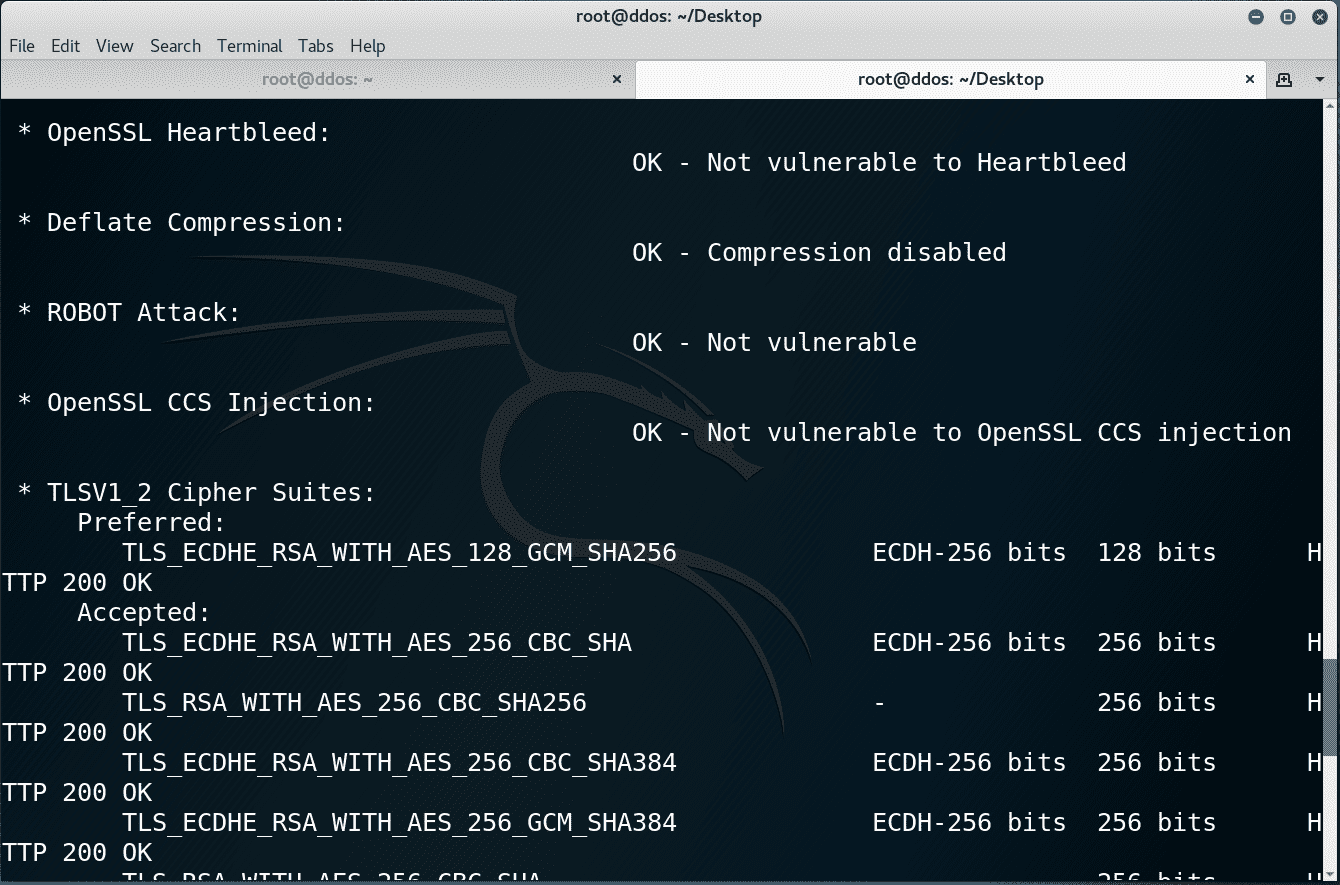
- Security testing: weak cipher suites, insecure renegotiation, CRIME, Heartbleed and more.
- Server certificate validation and revocation checking through OCSP stapling.
- Support for StartTLS handshakes on SMTP, XMPP, LDAP, POP, IMAP, RDP, PostGres, and FTP.
- Scan results can be written to an XML or JSON file for further processing.
- And much more!
How does it work?
SSLyze is all Python code but it uses an OpenSSL wrapper written in C called nassl, which was specifically developed for allowing SSLyze to access the low-level OpenSSL APIs needed to perform deep SSL testing.
Changelog v6.0
- Added support for Python 3.12 (#630).
- Removed support for Python 3.7 (#616).
- Switched to Python Cryptography’s implementation of certificate validation, in order to simplify the validation logic and make it more reliable (#638).
- Removed direct dependency to pyOpenSSL.
- Removed usages of
ssl.match_hostname()(#627). - JSON output changes for the certificate information plugin:
leaf_certificate_subject_matches_hostnamehas been removed because hostname validation is now directly reported in thepath_validation_results, which makes it simpler to process them.- Similarly,
openssl_error_stringwas renamed tovalidation_error.
- Fixed crash caused by “invalid padding” and “invalid encoding” errors (#632, #634).
- Better output when an SMTP EHLO is rejected ( #635).
Install
SSLyze can be installed directly via pip:
pip install --upgrade setuptools pip install sslyze sslyze --regular www.yahoo.com:443 www.google.com "[2607:f8b0:400a:807::2004]:443"
It is also easy to directly clone the repository and the fetch the requirements:
git clone https://github.com/nabla-c0d3/sslyze.git cd sslyze pip install -r requirements.txt --upgrade python -m sslyze --regular www.yahoo.com:443 www.google.com "[2607:f8b0:400a:807::2004]:443"
On Linux, the python-dev package needs to be installed first so that the nassl C extension can be compiled:
sudo apt-get install python-dev
SSLyze has been tested on the following platforms: Windows 7 (32 and 64 bits), Debian 7 (32 and 64 bits), macOS Sierra
Usage as a library
SSLyze can be used as a Python module in order to run scans and process the results directly in Python. Full documentation is available here.
Copyright (C) 2017 nabla-c0d3
Source: https://github.com/nabla-c0d3/





