SysWhispers: AV/EDR evasion via direct system calls
SysWhispers
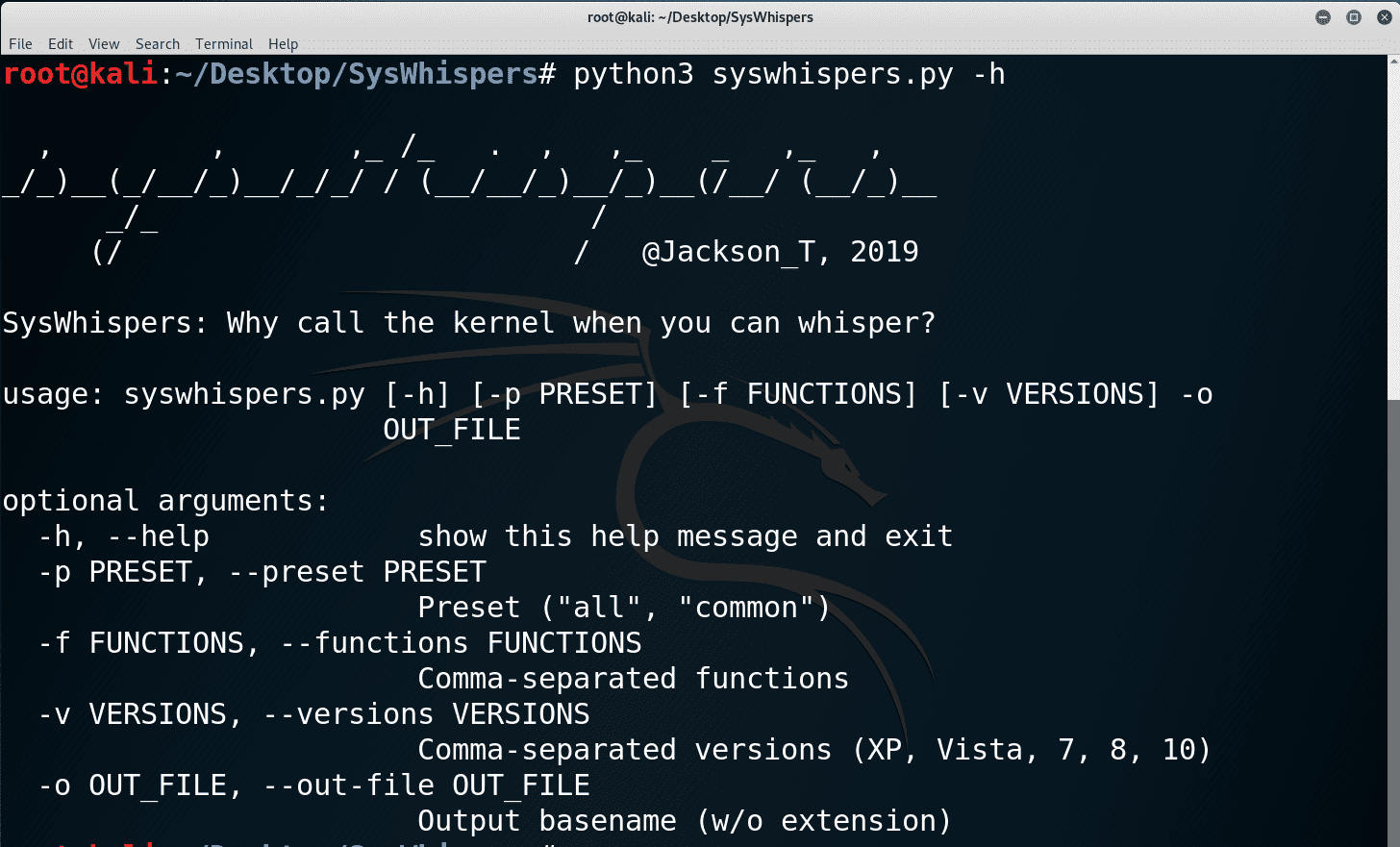
SysWhispers helps with evasion by generating header/ASM files implants can use to make direct system calls.
All core syscalls are supported from Windows XP to 10. Example generated files available in example-output/.
Introduction
Various security products place hooks in user-mode APIs which allow them to redirect execution flow to their engines and detect for suspicious behavior. The functions in ntdll.dll that make the syscalls consist of just a few assembly instructions, so re-implementing them in your own implant can bypass the triggering of those security product hooks. This technique was popularized by @Cn33liz and his blog post has more technical details worth reading.
SysWhispers provides red teamers the ability to generate header/ASM pairs for any system call in the core kernel image (ntoskrnl.exe) across any Windows version starting from XP. The headers will also include the necessary type of definitions.
The main implementation difference between this and the Dumpert POC is that this doesn’t call RtlGetVersion to query the OS version, but instead does this in the assembly by querying the PEB directly. The benefit is being able to call one function that supports multiple Windows versions instead of calling multiple functions each supporting one version.
Installation
> git clone https://github.com/jthuraisamy/SysWhispers.git
> cd SysWhispers
> pip3 install -r .\requirements.txt
Use
Tutorial
Copyright 2019 Jackson T.





