tabi: BGP Hijack Detection Tool
TaBi – Track BGP Hijacks – BGP Hijack Detection
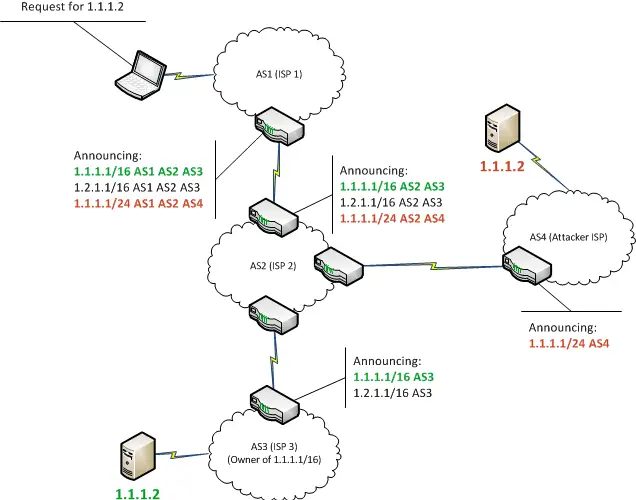
Developed since 2011 for the needs of the French Internet Resilience Observatory, TaBi is a framework that eases the detection of BGP IP prefixes conflicts, and their classification into BGP hijacking events. The term prefix hijacking refers to an event when an AS, called a hijacking AS advertises illegitimately a prefix equal or more specific to a prefix delegated to another AS, called the hijacked AS.
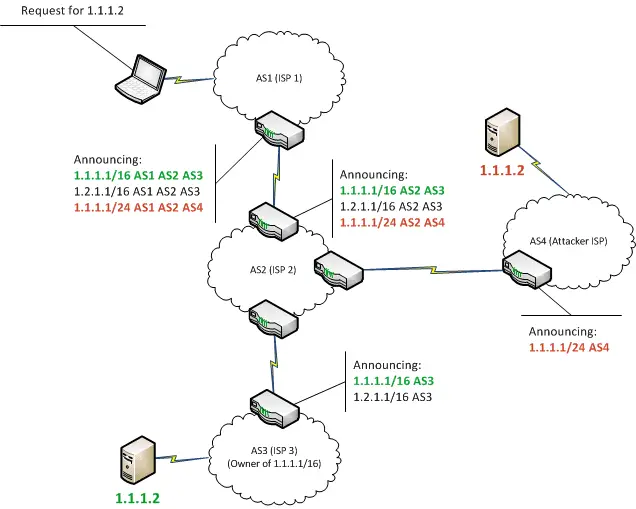 Image: bishopfox
Image: bishopfox
BGP hijacking (sometimes referred to as prefix hijacking, route hijacking or IP hijacking) is the illegitimate takeover of groups of IP addresses by corrupting Internet routing tables maintained using the Border Gateway Protocol (BGP). _Wiki
Usually, TaBi processes BGP messages that are archived in MRT files. Then, in order to use it, you will then need to install an MRT parser. Its favorite companion is MaBo, but it is also compatible with CAIDA’s bgpreader. Internally, TaBi translates BGP messages into its own representation. Therefore, it is possible to implement new inputs depending on your needs.
Authors
- Nicolas Vivet nicolas.vivet@ssi.gouv.fr
- Guillaume Valadon guillaume.valadon@ssi.gouv.fr
- Julie Rossi julie.rossi@ssi.gouv.fr
- François Contat francois.contat@ssi.gouv.fr
Install
TaBi depends on two external Python modules. The easiest method to install them is to use virtualenv and pip.
If you use a Debian-like system you can install these dependencies using:
apt-get install python-dev python-pip python-virtualenv
Then install TaBi in a virtual environment:
git clone https://github.com/ANSSI-FR/tabi.git
virtualenv ve_tabi
source ve_tabi/bin/activate
pip install py-radix python-dateutil
python setup.py install
Removing TaBi and its dependencies are therefore as simple as removing the cloned repository.
Usage
Historically TaBi was designed to process MRT dump files from the collectors of the RIPE RIS.
Grabbing MRT dumps
You will then need to retrieve some MRT dumps. Copying and pasting the following commands in a terminal will grab a full BGP view and some updates.
wget -c http://data.ris.ripe.net/rrc01/2016.01/bview.20160101.0000.gz
wget -c http://data.ris.ripe.net/rrc01/2016.01/updates.20160101.0000.gz
tabi – the command line tool
The tabi command is the legacy tool that uses TaBi to build technical indicators for the Observatory reports. It uses mabo to parse MRT dumps.
Given the name of the BGP collector, an output directory and MRT dumps using the RIS naming convention, tabi will follow the evolution of routes seen in MRT dumps (or provided with the –ases option) and detect BGP IP prefixes conflicts.
Several options can be used to control tabi behavior:
Among this options, two are very interesting:
-jthat forks severaltabiprocesses to process the MRT dumps faster-athat can be used to limit the output to a limited list of ASes
Note that the legacy output mode will likely consume all file descriptors as it creates two files per processed AS (i.e. around 100k opened files). The default is the combined output mode.
Here is an example call to tabi:
tabi -j 8 rrc01 results/ bview.20160101.0000.gz updates.20160101.0000.gz
After around 5 minutes of processing, you will find the following files in results/2016.01/:
all.defaults.json.gzthat contains all default routes seen by TaBiall.routes.json.gzthat contains all routes monitoredall.hijacks.json.gzthat contains all BGP prefix conflicts
Using TaBi as a Python module
TaBi could also be used as a regular Python module in order to use it in your own tool.
The example provided in this repository enhance BGP prefix conflicts detection, with possible hijacks classification. To do so, it relies on external data sources such as RPKI ROA, route objects, and other IRR objects.
Source: https://github.com/ANSSI-FR/tabi






