Threat Mapper v2.0 releases: Identify vulnerabilities in running containers, images, hosts and repositories
Deepfence Runtime Threat Mapper
The Deepfence Runtime Threat Mapper is a subset of the Deepfence cloud-native workload protection platform, released as a community edition. This community edition empowers the users with the following features:
- Visualization: Visualize kubernetes clusters, virtual machines, containers and images, running processes, and network connections in near real-time.
- Runtime Vulnerability Management: Perform vulnerability scans on running containers & hosts as well as container images.
- Container Registry Scanning: Check for vulnerabilities in images stored on AWS ECR, Azure Container Registry, Google Container Registry, Docker Hub, Docker Self-Hosted Private Registry, Quay, Harbor, Gitlab, and JFrog registries.
- CI/CD Scanning: Scan images as part of existing CI/CD Pipelines like CircleCI, Jenkins & GitLab.
- Integrations with SIEM, Notification Channels & Ticketing: Ready to use integrations with Slack, PagerDuty, HTTP endpoint, Jira, Splunk, ELK, Sumo Logic, and Amazon S3.
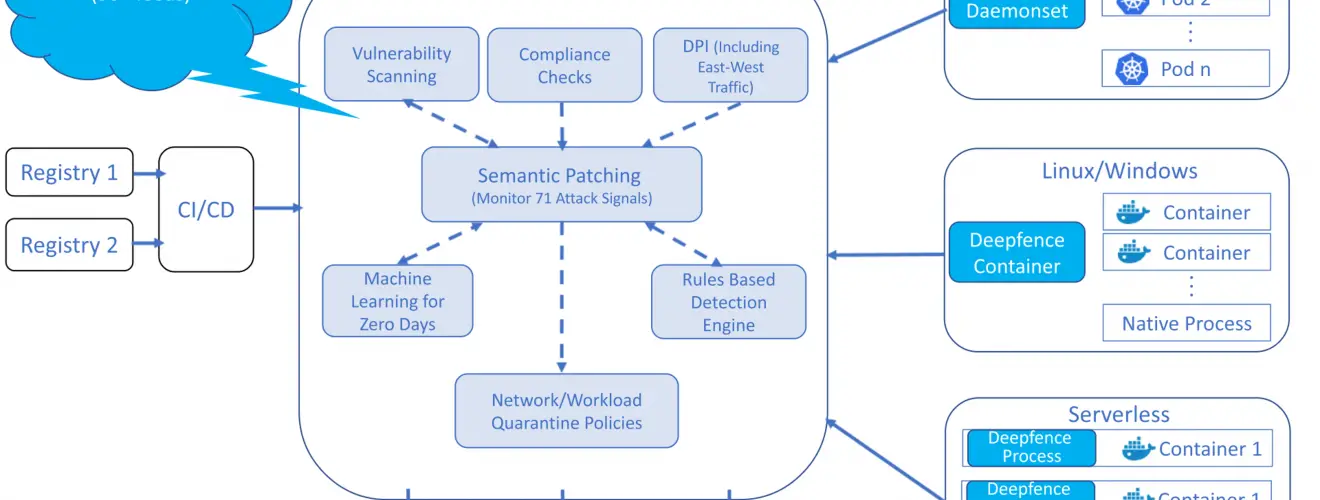
Architecture
A pictorial depiction of the Deepfence Architecture is below
Feature Availability
| Features | Runtime Threat mapper (Community Edition) | Workload Protection Platform (Enterprise Edition) |
|---|---|---|
| Discover & Visualize Running Pods, Containers and Hosts | ✔️ (unlimited) | ✔️ (unlimited) |
| Runtime Vulnerability Management for hosts/VMs | ✔️ (unlimited) | ✔️ (unlimited) |
| Runtime Vulnerability Management for containers | ✔️ (unlimited) | ✔️ (unlimited) |
| Container Registry Scanning | ✔️ | ✔️ |
| CI/CD Integration | ✔️ | ✔️ |
| Multiple Clusters | ✔️ | ✔️ |
| Integrations with SIEMs, Slack and more | ✔️ | ✔️ |
| Compliance Automation | ❌ | ✔️ |
| Deep Packet Inspection of Encrypted & Plain Traffic | ❌ | ✔️ |
| API Inspection | ❌ | ✔️ |
| Runtime Integrity Monitoring | ❌ | ✔️ |
| Network Connection & Resource Access Anomaly Detection | ❌ | ✔️ |
| Workload Firewall for Containers, Pods and Hosts | ❌ | ✔️ |
| Quarantine & Network Protection Policies | ❌ | ✔️ |
| Alert Correlation | ❌ | ✔️ |
| Serverless Protection | ❌ | ✔️ |
| Windows Protection | ❌ | ✔️ |
| Highly Available & Multi-node Deployment | ❌ | ✔️ |
| Multi-tenancy & User Management | ❌ | ✔️ |
| Enterprise Support | ❌ | ✔️ |
Changelog v2.0
- Add initial worker server by @noboruma in #691
- Add updated UI Setup by @manV in #698
- hoist storybook packages for new ui by @manV in #704
- Add reusable tailwind preset by @manV in #705
- Add fonts to dashboard and Readmes by @manV in #706
- added breadcrumb component by @milan-deepfence in #707
- V2 UI accordion component by @milan-deepfence in #710
- Fix typo in a component name by @milan-deepfence in #713
- added basic unit test for accordion and breadcrumb component by @milan-deepfence in #714
- fix warning caused by slot expecting ref attribute by @milan-deepfence in #716
- Update UI deps by @manV in #717
- use path aliases for ui components package by @manV in #719
- added to slide modal from left by @milan-deepfence in #723
- API client setup for UI by @manV in #736
- fix missing styles by @milan-deepfence in #738
- update styles by @milan-deepfence in #740
- fix:update styles by @milan-deepfence in #747
- update ui components style by @milan-deepfence in #794
- V2 UI login by @milan-deepfence in #795
- More…
Install & Use
Copyright (c) 2020 deepfence







